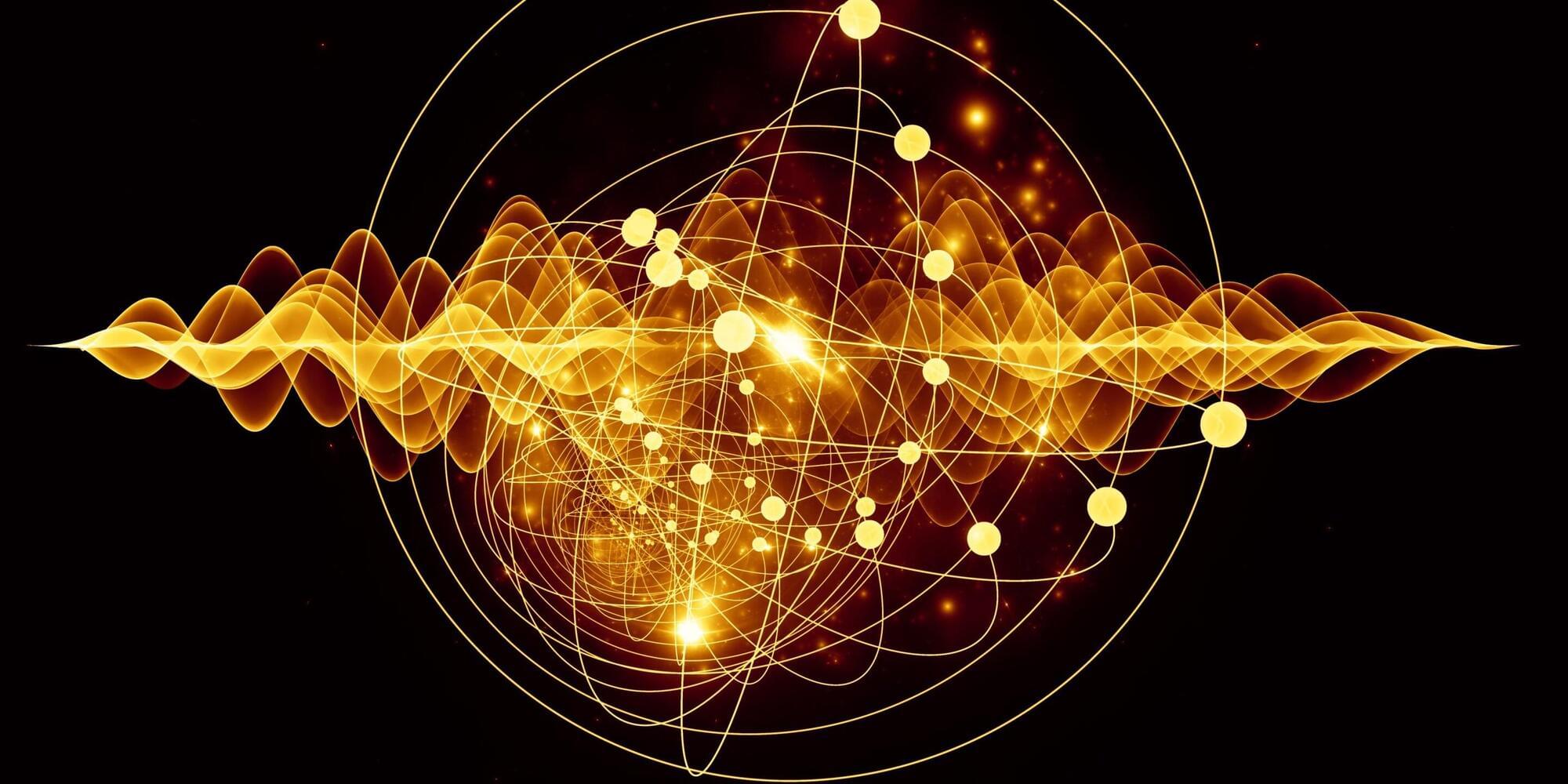
An international team of researchers has reported a major advance in understanding quantum dynamics in semiconductor materials. They directly observed how excitons and phonons evolve together in perovskite nanocrystals, revealing a fully coherent quantum dance between light-induced electronic excitations and crystal lattice vibrations. They published their findings in Nature Communications.
An exciton is created when light excites an electron inside a semiconductor. The electron absorbs energy and leaves behind a positively charged “hole”; the two bind together and move through the crystal as a single quantum object. A phonon is a different kind of quantum object, as it is a quantum of crystal lattice vibration. Though fundamentally different objects, in perovskites they are strongly linked and evolve together as a coupled quantum system.
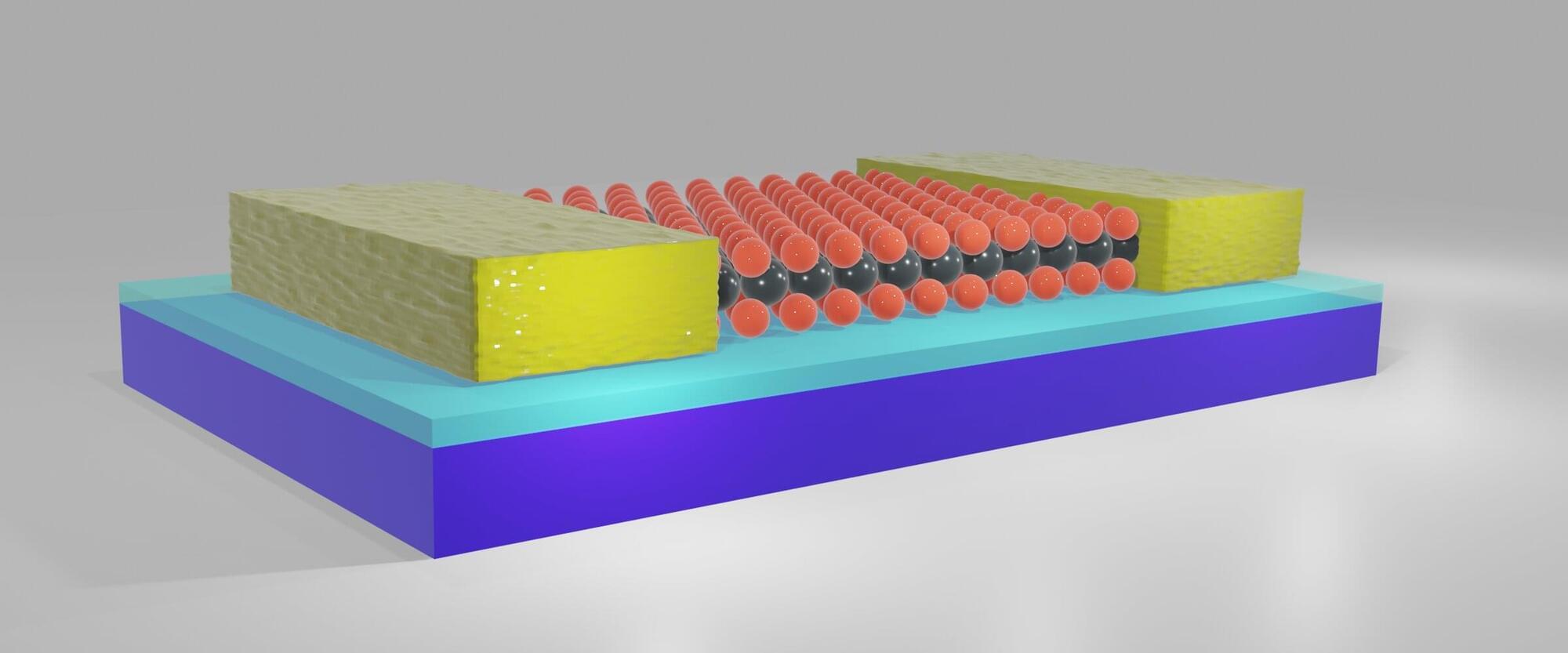
Perovskite nanocrystals are miniature crystals only a few nanometers in size, a thousand times smaller than the thickness of a hair. Each crystal forms a nanoscale “box” that traps both excitons and phonons. This confinement makes the interaction between them especially strong: An exciton inside the nanocrystal is tightly coupled to vibrations of the surrounding crystal lattice.