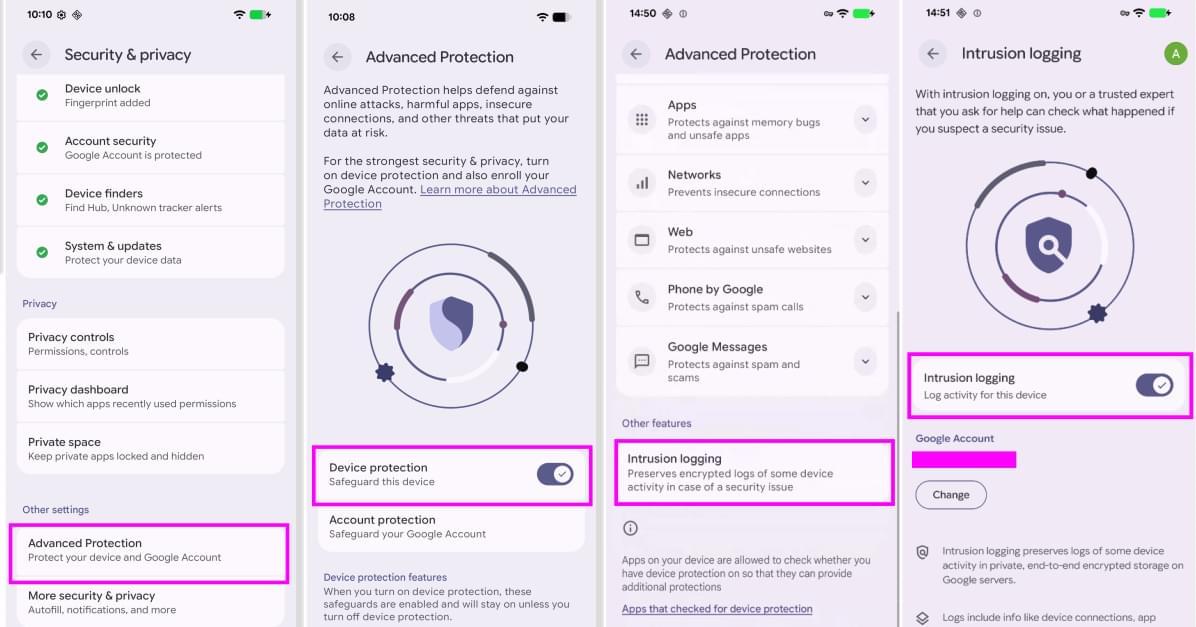
Android Intrusion Logging stores encrypted forensic logs for 12 months, helping experts investigate spyware attacks on high-risk users.

RCS is a modern, internet-based messaging protocol that allows Android and iPhone users to send high-resolution photos and videos, see typing indicators, and receive read receipts, features all typically present in instant messaging apps. It is built on an industry specification called the RCS Universal Profile.
“When RCS messages are end-to-end encrypted, they can’t be read while they’re sent between devices,” Apple said in a statement. “Users will know that a conversation is end-to-end encrypted when they see a new lock icon in their RCS chats.”
Apple began testing with E2EE in RCS messages in iOS and iPadOS 26.4 Beta, initially limiting it to only conversations between Apple devices. In early 2025, the GSM Association (GSMA) announced support for E2EE for safeguarding messages sent via the RCS protocol.
Perhaps the most famous example comes from a theorem by the logician Kurt Gödel’s celebrated result — one of two “incompleteness theorems” he published in 1931 — established that for any reasonable set of basic mathematical assumptions, called axioms, it’s impossible to prove that the axioms won’t eventually lead to contradictions. Though mathematicians continued their research much as they had before, they would never again be certain that their rules were self-consistent.
More than 50 years after Gödel’s theorem, cryptographers devised a radical new proof method in which unknowability played a very different role. Proofs based on this technique, called zero-knowledge proofs, can convince even the most skeptical audience that a statement is true without revealing why it’s true.
These two flavors of unknowability, which originated decades apart and in different fields, were long considered completely unrelated. Now the computer scientist Rahul Ilango (opens a new tab) has established a striking connection (opens a new tab) between them. While still a graduate student, he devised a new type of zero-knowledge proof in which secrecy stems from the fundamental limits of math. Ilango’s approach gets around limitations of zero-knowledge proofs that researchers have long thought insurmountable, pushing the boundaries of what such a proof can be. The work has also spurred researchers to explore other intriguing links between mathematical logic and cryptography.

As the United States, Europe, and China compete to shape the future of the Earth-Moon corridor, strategic advantage will depend not only on launch capacity or lunar infrastructure, but also on advances in quantum technologies. Just as secure systems are critical on Earth, satellites and space-based systems underpin high-value, high-impact operations from financial transactions and navigation to scientific discovery and classified military missions.
Quantum technologies, which enable new levels of speed, sensitivity, and security, are emerging as critical tools to improve existing extraterrestrial systems. Modern digital communications are secured by encryption built on math problems that are extremely difficult for regular computers to solve, but that sufficiently advanced quantum computers could eventually crack. Quantum communications technologies could add a new layer of protection by making it easier to detect when someone is trying to intercept sensitive information. Quantum sensors can measure position and time with an accuracy that GPS only approximates. Lastly, quantum computers could unlock new capabilities beyond current computational limits, from designing advanced materials to optimizing increasingly complex satellite networks.
Countries are racing to match their space and quantum ambitions with national strategies. The White House is reportedly drafting an executive order to strengthen US competitiveness in quantum technologies. The rumored draft directs multiple US government bodies, including NASA, to develop a five-year roadmap to expand quantum sensing and networking capabilities. The EU’s 2025 Quantum Europe Strategy highlights “Space and Dual-Use Quantum Technologies” as one of its five strategic focuses, and China’s 15th Five-Year Plan has called for expanding the country’s ground-to-space quantum communications network.
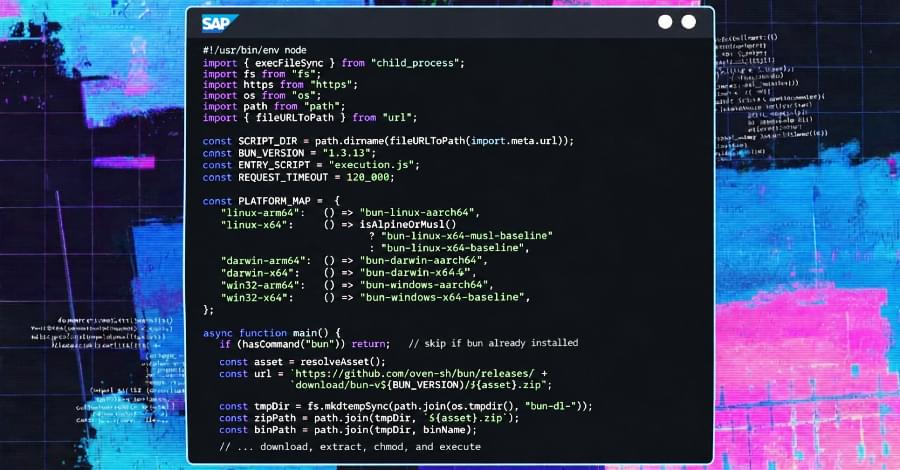
Threat hunters are warning that the cybercriminal operation known as VECT 2.0 acts more like a wiper than a ransomware due to a critical flaw in its encryption implementation across Windows, Linux, and ESXi variants that renders recovery impossible even for the threat actors.
The fact that VECT’s locker permanently destroys large files rather than encrypting them means even victims who opt to pay the ransom cannot get their data back, as the decryption keys are discarded by the malware during the time encryption occurs.
“VECT is being marketed as ransomware, but for any file over 131KB – which is most of what enterprises actually care about – it functions as a data destruction tool,” Eli Smadja, group manager at Check Point Research, said in a statement shared with The Hacker News.

A new Kyber ransomware operation is targeting Windows systems and VMware ESXi endpoints in recent attacks, with one variant implementing Kyber1024 post-quantum encryption.
Cybersecurity firm Rapid7 retrieved and analyzed two distinct Kyber variants in March 2026 during an incident response. Both variants were deployed on the same network, with one targeting VMware ESXi and the other focusing on Windows file servers.
“The ESXi variant is specifically built for VMware environments, with capabilities for datastore encryption, optional virtual machine termination, and defacement of management interfaces,” explains Rapid7.

A SystemBC proxy malware botnet of more than 1,570 hosts, believed to be corporate victims, has been discovered following an investigation into a Gentlemen ransomware attack carried out by a gang affiliate.
The Gentlemen ransomware-as-a-service (RaaS) operation emerged around mid-2025 and provides a Go-based locker that can encrypt Windows, Linux, NAS, and BSD systems, and a C-based locker for ESXi hypervisors.
Last December, it compromised one of Romania’s largest energy providers, the Oltenia Energy Complex. Earlier this month, The Adaptavist Group disclosed a breach that Gentlemen ransomware listed on its data leak site.
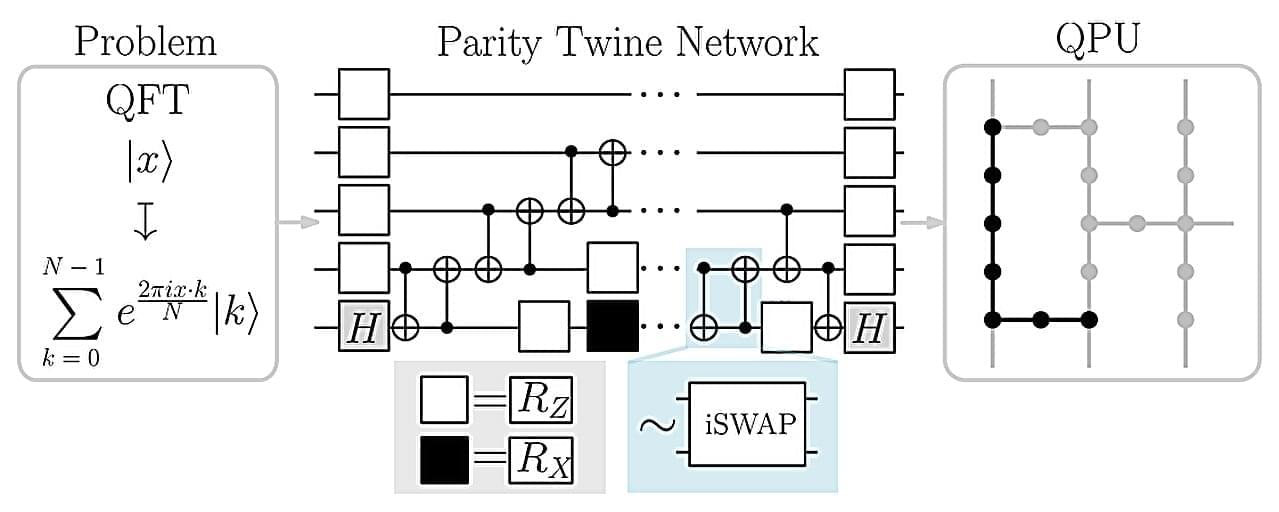
The spin-off company ParityQC has implemented the largest quantum Fourier transform ever reported using an IBM quantum computer, thereby setting a new milestone on the path toward the industrial application of quantum computers. The quantum Fourier transform is a cornerstone algorithm with applications in cryptography, financial modeling, and materials science.
Innsbruck-based quantum architecture company ParityQC performed a quantum Fourier transform using 52 superconducting qubits on an IBM Heron quantum processor. This surpasses the previous record of 27 qubits, which was set two years ago using an ion-trap quantum computer. The results were published this week on the arXiv preprint server.
“This milestone was only possible through the synergy of IBM’s latest quantum hardware and the ParityQC Architecture, which unlocked an exponential improvement in efficiency,” say Wolfgang Lechner and Magdalena Hauser, Co-CEOs of ParityQC. “What we are witnessing is European quantum innovation taking a global lead in translating theoretical potential into real-world performance.”
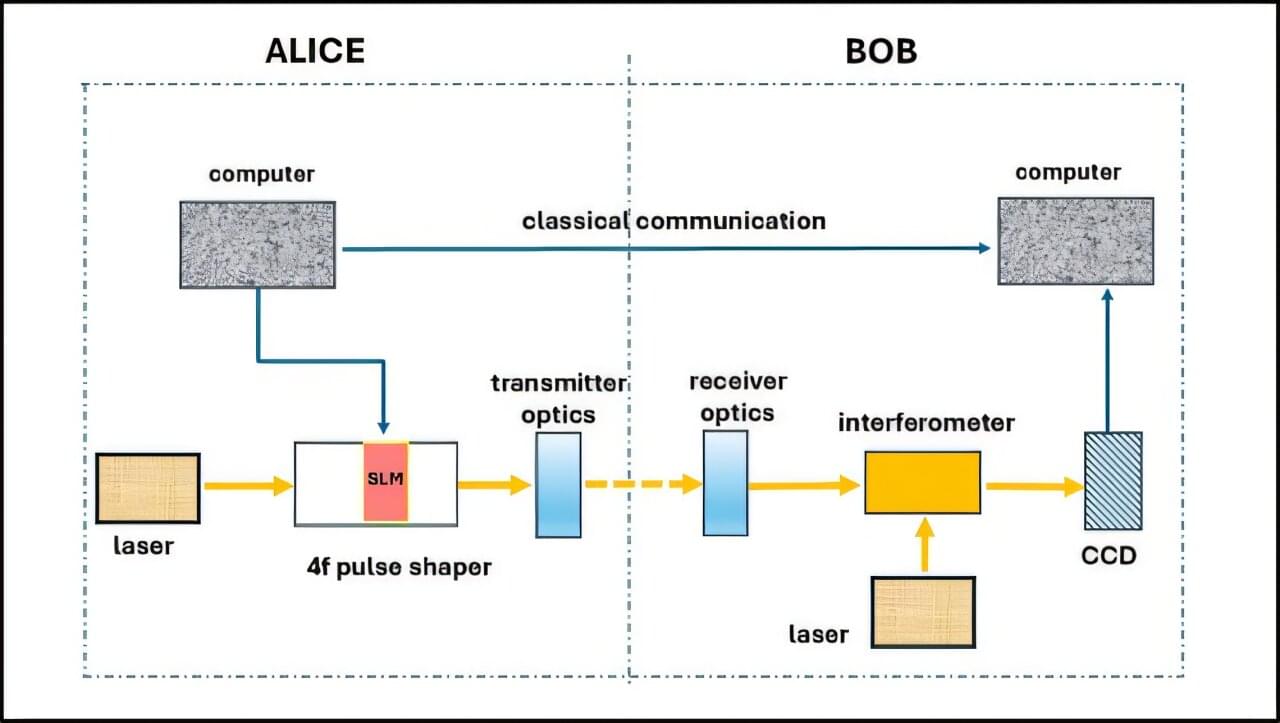
Researchers at Ben-Gurion University of the Negev have developed a new approach to secure optical communication that hides information in the physical structure of light, making it difficult for unauthorized parties to intercept or decode. The study addresses a growing challenge: advances in quantum computing are expected to weaken many of today’s encryption methods. While most security solutions rely on complex mathematical algorithms, this research adds protection earlier in the process—during the transmission of the signal itself.
The research was led by Dr. Judith Kupferman and Prof. Shlomi Arnon from the School of Electrical and Computer Engineering at Ben-Gurion University of the Negev. The findings were published in Optical and Quantum Electronics.
The researchers propose a communication method based on specially shaped light pulses, known as spatiotemporal optical vortices. These light beams are designed so that their key features are not visible in standard measurements.