WhatsApp VBS campaign began February 2026, abusing AWS and UAC bypass to gain persistent remote access.



A multi-pronged phishing campaign is targeting Spanish-speaking users in organizations across Latin America and Europe to deliver Windows banking trojans like Casbaneiro (aka Metamorfo) via another malware called Horabot.
The activity has been attributed to a Brazilian cybercrime threat actor tracked as Augmented Marauder and Water Saci. The e-crime group was first documented by Trend Micro in October 2025.
“This threat group employs a wider-ranging attack model focused on a bespoke delivery and propagation mechanism that includes WhatsApp, ClickFix techniques, and email-centric phishing,” BlueVoyant security researchers Thomas Elkins and Joshua Green said in a technical breakdown published Tuesday.


A new malware-as-a-service called CrystalRAT is being promoted on Telegram, offering remote access, data theft, keylogging, and clipboard hijacking capabilities.
The malware emerged in January with a tiered subscription model. Apart from the Telegram channel, the MaaS was also promoted on YouTube via a dedicated marketing channel that showcased its capabilities.
Kaspersky researchers say in a report today that the malware features strong similarities to WebRAT (Salat Stealer), including the same panel design, Go-based code, and a similar bot-based sales system.

A new malicious kit called EvilTokens integrates device code phishing capabilities, allowing attackers to hijack Microsoft accounts and provide advanced features for business email compromise attacks.
The kit is sold to cybercriminals over Telegram and is under continuous development, its author stating that they plan to extend support for Gmail and Okta phishing pages.
Device code phishing attacks abuse the OAuth 2.0 device authorization flow, in which attackers gain access to a victim account by tricking the owner into authorizing a malicious device.

A new Android malware named NoVoice was found on Google Play, hidden in more than 50 apps that were downloaded at least 2.3 million times.
The apps carrying the malicious payload included cleaners, image galleries, and games. They required no suspicious permissions and provided the promised functionality.
After launching an infected app, the malware tried to obtain root access on the device by exploiting old Android vulnerabilities that received patches between 2016 and 2021.

Remote access and trusted administrative tools play a central role in how organizations operate today. According to Blackpoint Cyber’s 2026 Annual Threat Report, they are also increasingly central to how intrusions begin.
Informed by analysis of thousands of security investigations conducted during the reporting period, the report highlights a shift in attacker behavior. Rather than relying primarily on vulnerability exploitation, threat actors frequently gained access by using valid credentials, legitimate tools, and routine user-driven actions.
The report examines these patterns, documents where intrusion activity was disrupted, and presents defensive priorities derived from analyzed incident response outcomes observed throughout 2025.

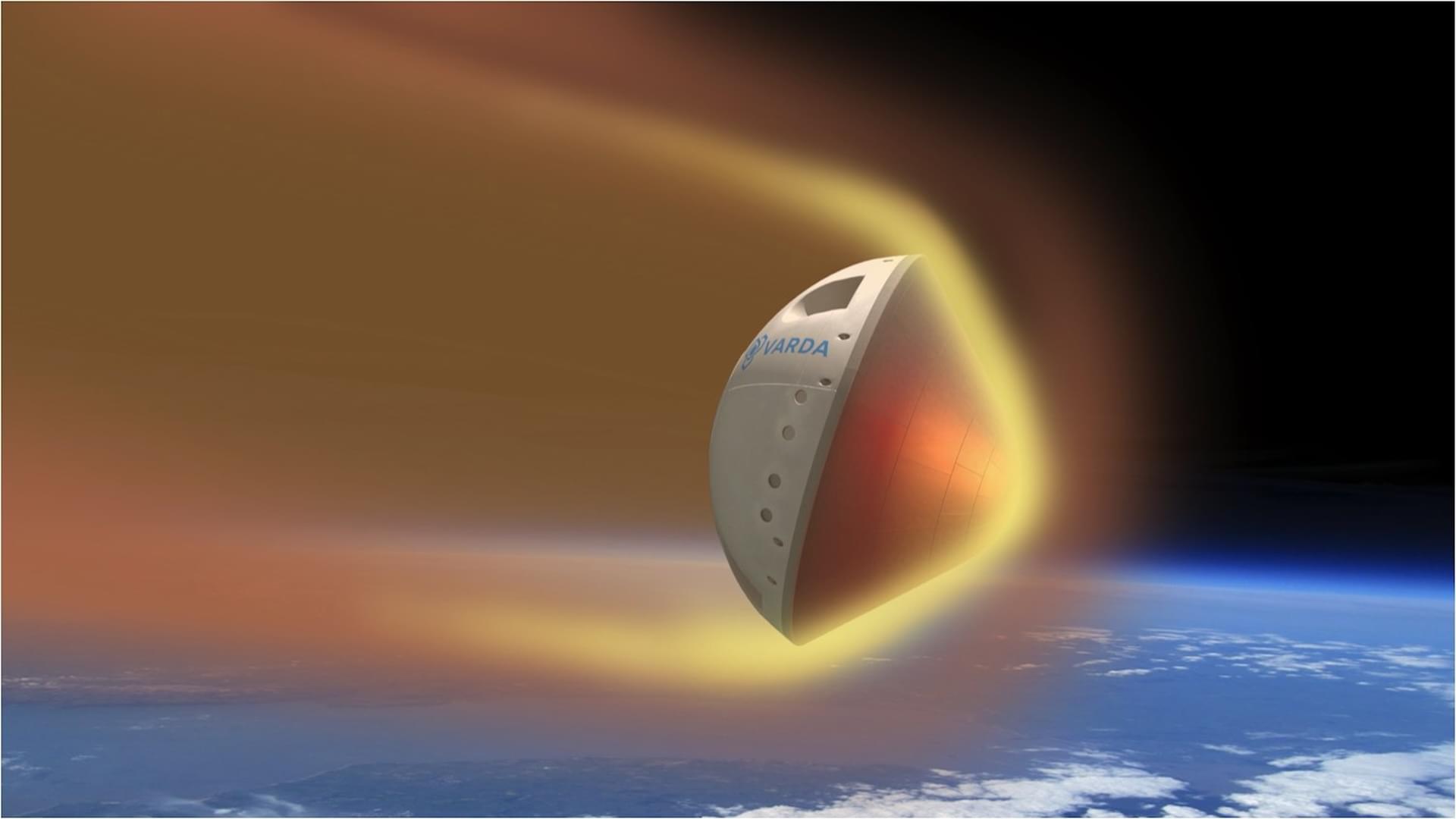
Varda Space Industries has launched its sixth reentry capsule aboard SpaceX’s Transporter-16 mission.
The capsule launched aboard a Falcon 9 rocket from Vandenberg Space Force Base, California, at 4:02 am PT (11:02 am UTC). It carried a US government-funded hypersonic technology experiment within its interior.
The payload was designed to test a hypersonic navigation system capable of accurately identifying spacecraft position, even when communications are blocked by intense plasma sheaths during hypersonic flight.