Researchers from the Department of Electrical and Computer Engineering in the Faculty of Engineering at the University of Hong Kong (HKU) and the Centre for Advanced Semiconductors and Integrated Circuits (CASIC) have achieved a major breakthrough in cryogenic electronics. The team has developed a programmable neuromorphic hardware platform that operates near absolute zero, providing a potential solution for scaling up quantum computers and enabling deep-space exploration. The discovery was published in Nature Communications in an article titled “Cryogenic neuromorphic circuits using gate-controlled negative differential resistance in silicon carbide.”
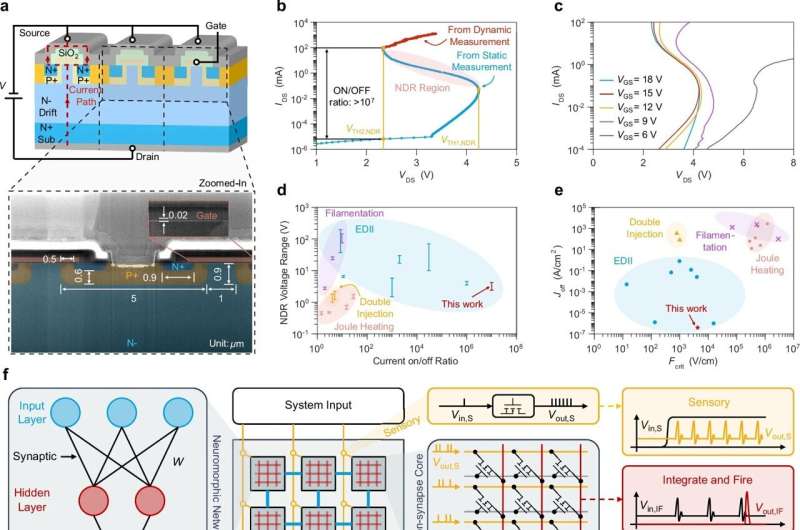
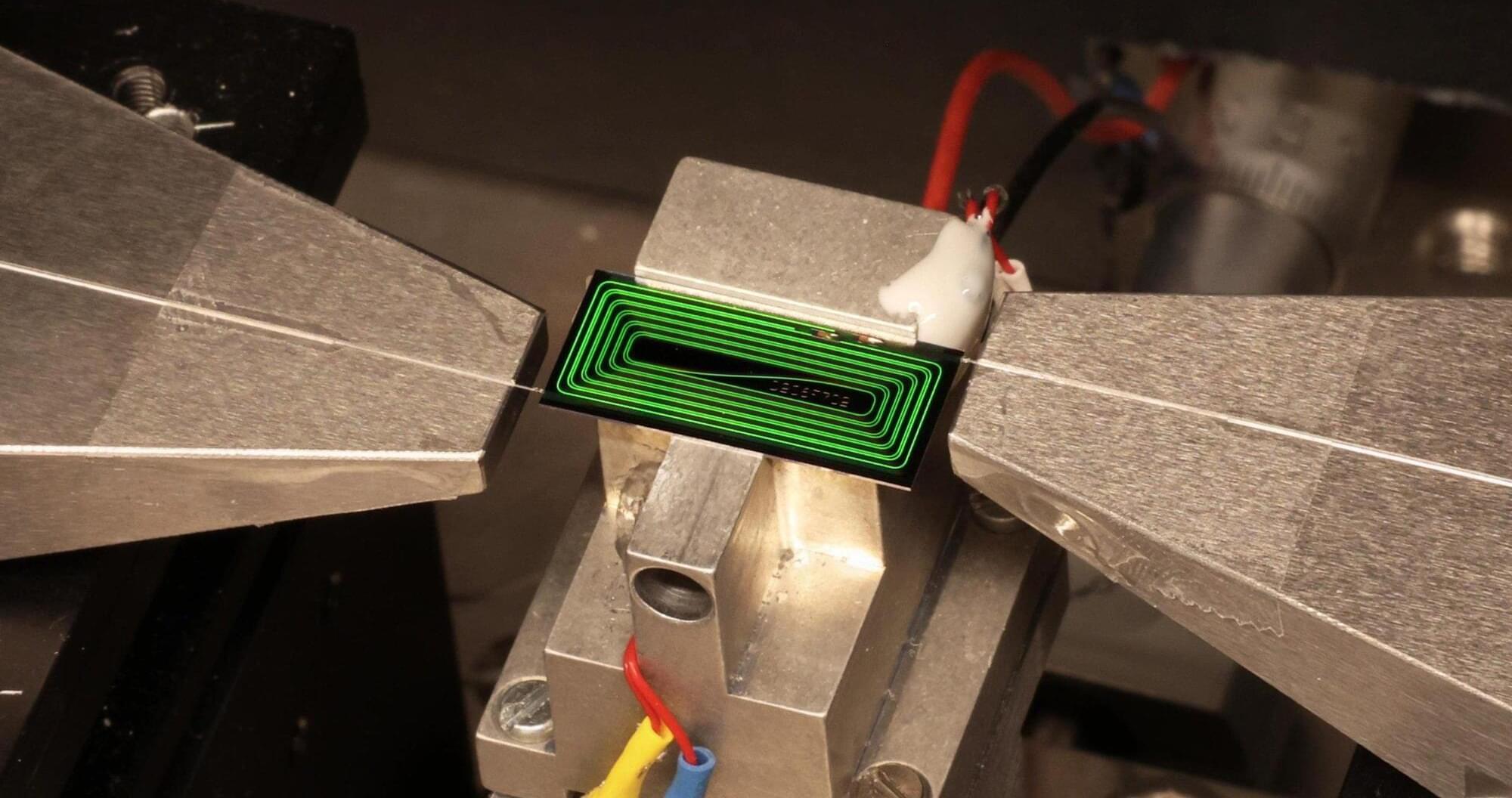
Led by Professor Yuhao Zhang and Ph.D. student Xin Yang, the team discovered an innovative way to generate and control negative differential resistance (NDR) in industry-standard silicon carbide (SiC) MOSFETs. For the first time, they demonstrated that a single transistor can mimic the energy-efficient “spiking” behavior of biological neurons at temperatures as low as 10 mK.
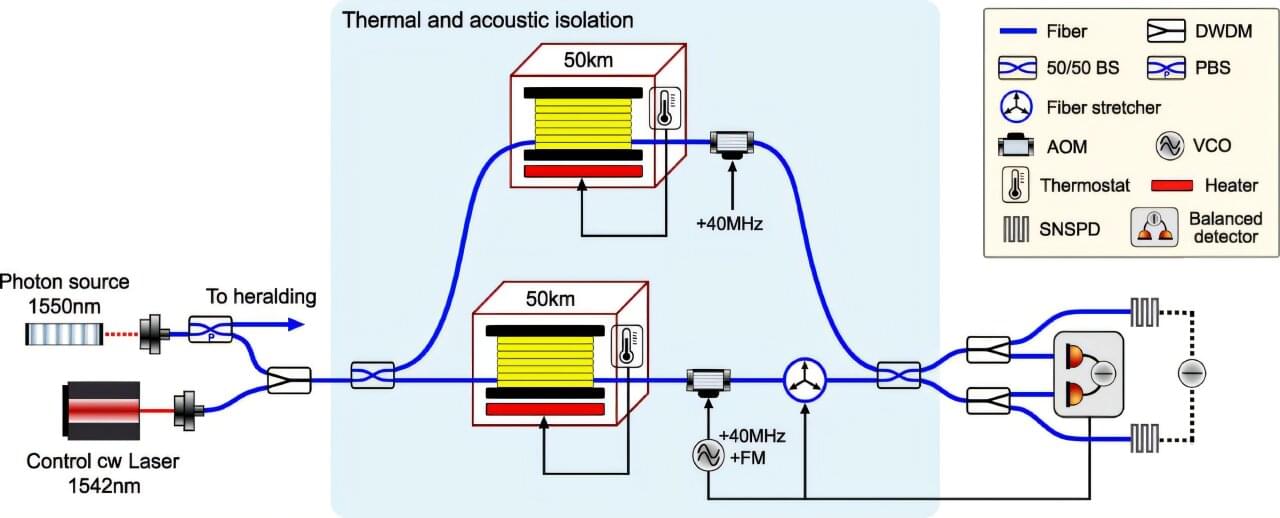
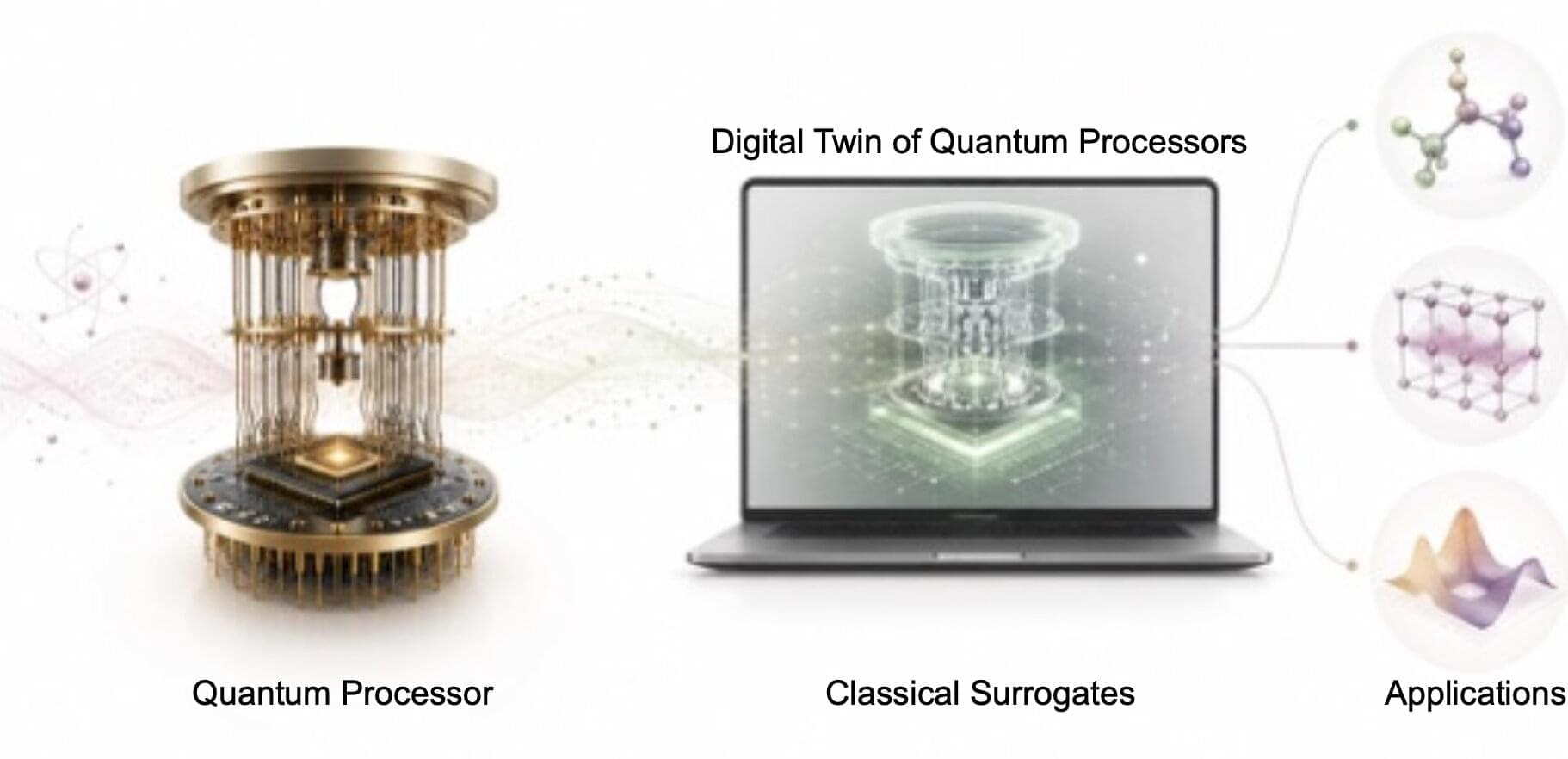
Modern quantum computers rely on complex electronics to control qubits, which are extremely sensitive and must be maintained at millikelvin temperatures. Current silicon-based controllers generate excessive heat and consume high levels of power, forcing them to be placed far from the qubits. This separation creates a wiring bottleneck that limits the scalability and performance of quantum systems.