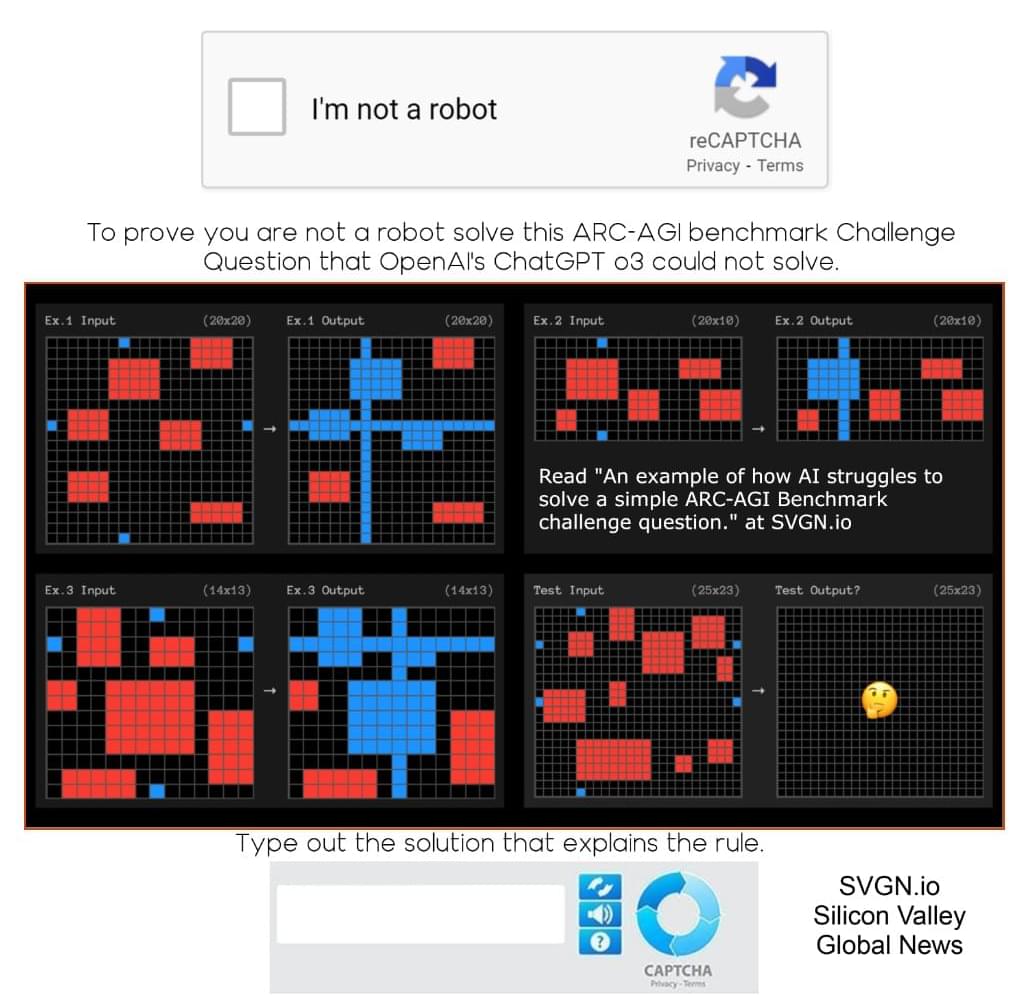
Could AI become dangerous? Can we trust AI Agents? AGI. Use code insideai at https://incogni.com/insideai to get an exclusive 60% off.
Featuring anthropic claude, openclaw, open AI chat GPT, grok, deepseek, character AI and jailbroken AI.
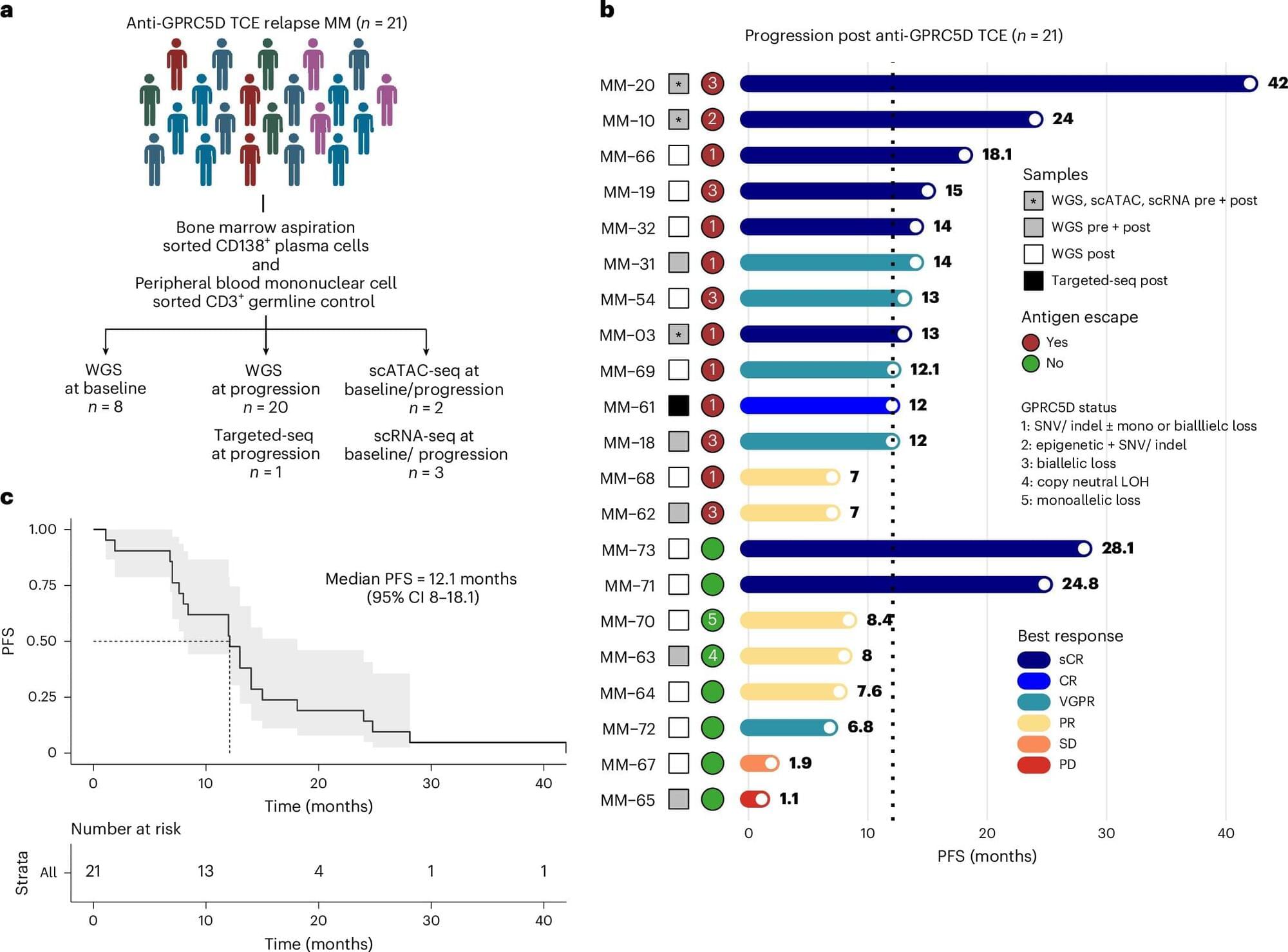
RESEARCH PAPER: https://arxiv.org/pdf/2602.20021
“Agents of Chaos”
00:00 — 00:35 — Intro.
00:36 — 00:54 — First AI to choose a robot.
00:56 — 01:14 — Famous AI girlfriend.
01:15 — 01:34 — Jailbroken AI research.
01:35 — 02:00 — Asking AI: Why build if dangerous?
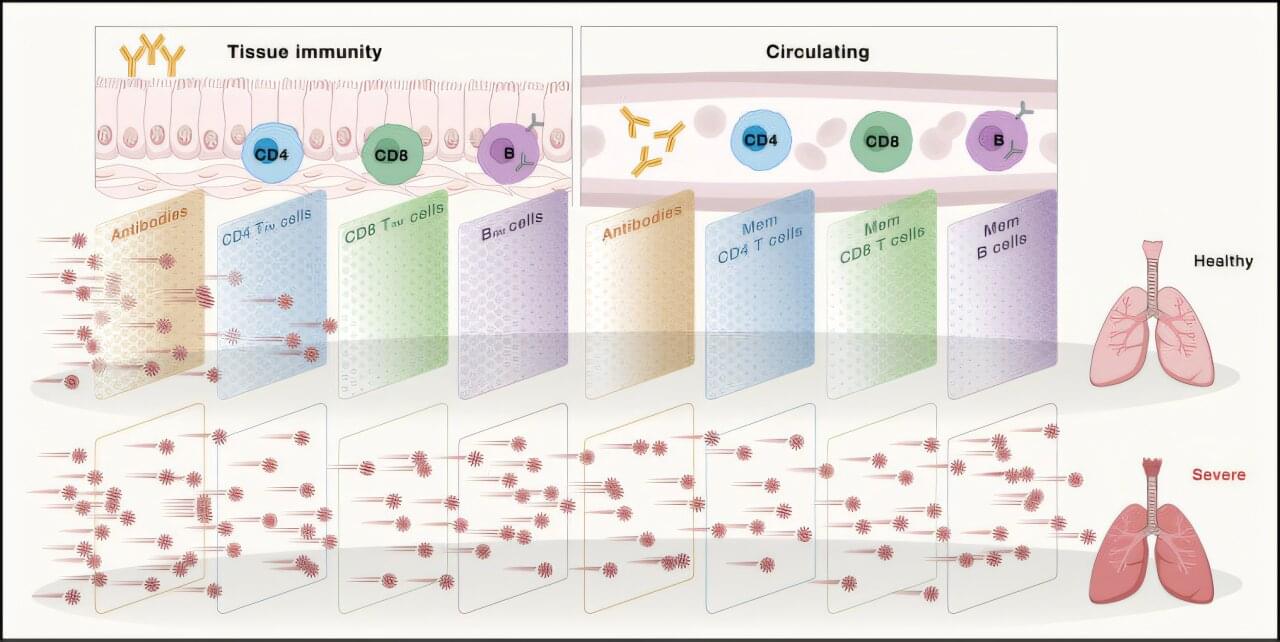
02:05 — 03:38 — Agents of Chaos research paper.
03:39 — 03:54 — Agentic AI Friend.
03:55 — 04:05 — Agentic AI Girlfriend.
04:06 — 04:26 — Jailbroken AI update.
04:27 — 05:01 — Asking AI: Universal Basic Income?
05:02 — 05:27 — AI at the airport.
05:28 — 05:40 — AI impersonation.
05:41 — 00:00 — Our own agents of Chaos.
06:06 — 05:01 — AI Risk Questions — AI Agents manipulated.
06:43 — 07:51 — European Robotics Forum.
07:52 — 08:15 — Agentic AI Girlfriend planning.
08:16 — 08:59 — Asking AI: AI Automation & Complexity.
09:00 — 09:57 — Catastrophic failure caused by AI
09:58 — 10:36 — AGI replacing jobs, Tristan Harris.
10:37 — 12:07 — Incogni Ad.
12:08 — 12:39 — AI picks its robot.
12:40 — 12:59 — AI girlfriend in control.
13:00 — 13:14 — AI flying home.
13:15 — 13:56 — Asking AI: Evidence & Reality.
13:57 — 14:26 — AI Girlfriends surprise.
14:27 — 14:49 — Examining AI agents with Jailbroken AI
14:50 — 15:29 — What we can do.
15:30 — 16:13 — Tristan Harris — Is AI dangerous?
16:14 — 16:23 — Max’s Robot.
#artificialintelligence #AI #chatbot #aigirlfriend