It’s often the case that a dynamical system’s constituents move orders of magnitude more quickly than the collective motion that interests researchers. That disparity in scale frustrates modelers. So many computationally intensive time steps are needed to reach the final state that the computation becomes infeasible. Now Filippo Bigi of the Swiss Federal Institute of Technology in Lausanne (EPFL) and his colleagues have extended and tested an approach that uses a machine-learning model to extend the time steps in an atomic-scale simulation by an order of magnitude or more while obeying physical constraints [1]. Their method is general and could be applied to planetary systems, molecular machines, and other dynamical systems.
The EPFL researchers’ starting point was a formulation of classical mechanics that describes the evolution of a system in terms of the positions and momenta of its constituents and an energy term, the Hamiltonian. In general, these and other equations of classical mechanics satisfy fundamental geometric constraints. What’s more, approximate solutions of those equations can be made to satisfy the same constraints. Bigi and his colleagues realized that machine learning could leapfrog over many time steps while also respecting those same geometric constraints.
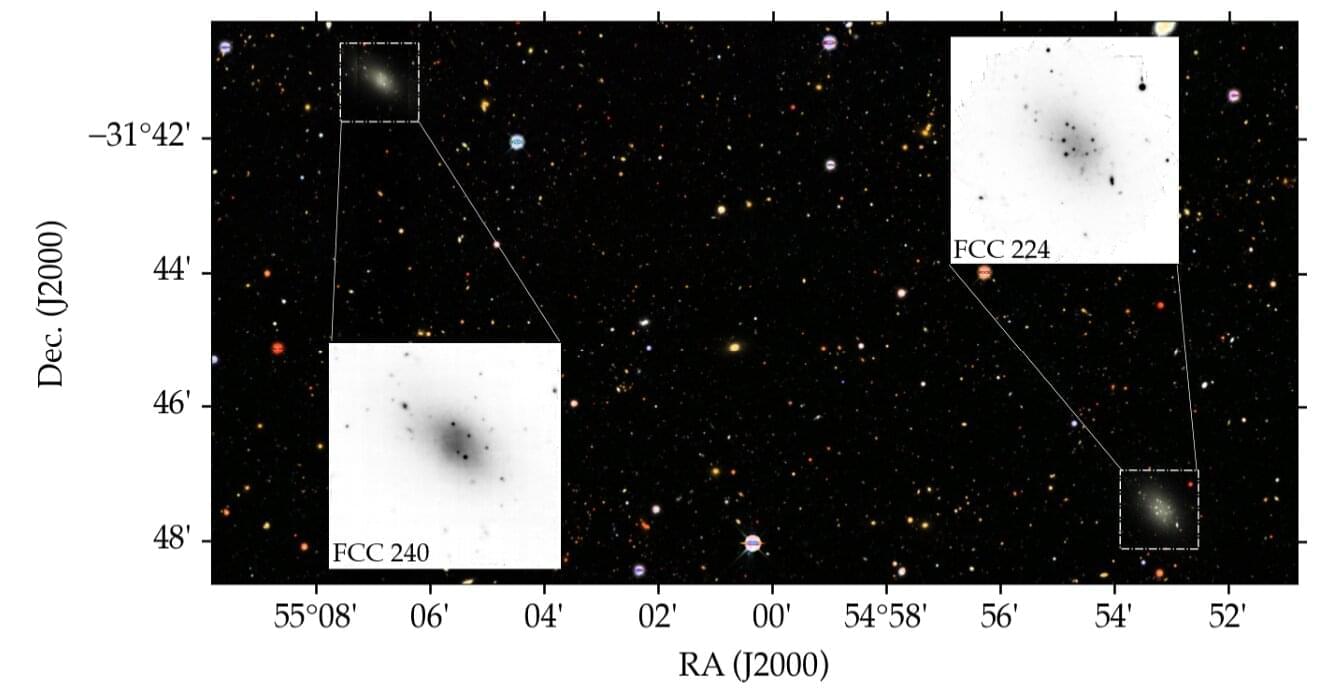
The researchers tested their approach on several systems, including the three-body problem of celestial dynamics and the transition of germanium telluride to a glassy state. Their simulations reproduced trusted benchmarks but with time steps ten or so times longer. Currently, enforcing the physical constraints undoes most of the computational advantage of the longer time steps. However, the team is optimistic that it can find more computationally efficient implementations.