Non-invasive eye scans allow doctors a zoomed-in, three-dimensional look beneath the eye’s surface without causing discomfort or pain to the patient. Used routinely in clinics worldwide, the scans produce detailed views of individual layers of the eye’s interior to help diagnose conditions that threaten vision. But with that level of precision comes a flood of data—hundreds of images per scan that physicians have to review manually, a time-consuming process that is vulnerable to human error.
Now, researchers at Washington University School of Medicine in St. Louis, in collaboration with colleagues at the University of Washington in Seattle and Genentech, Inc., have developed an experimental artificial intelligence (AI) system that can speed the scan review process and help doctors spot subtle signs of eye disease sooner. The technology, called OCTCube-M, includes a family of three AI models that are designed to read and interpret 3D images of the eye’s retina as well as other types of eye scans.
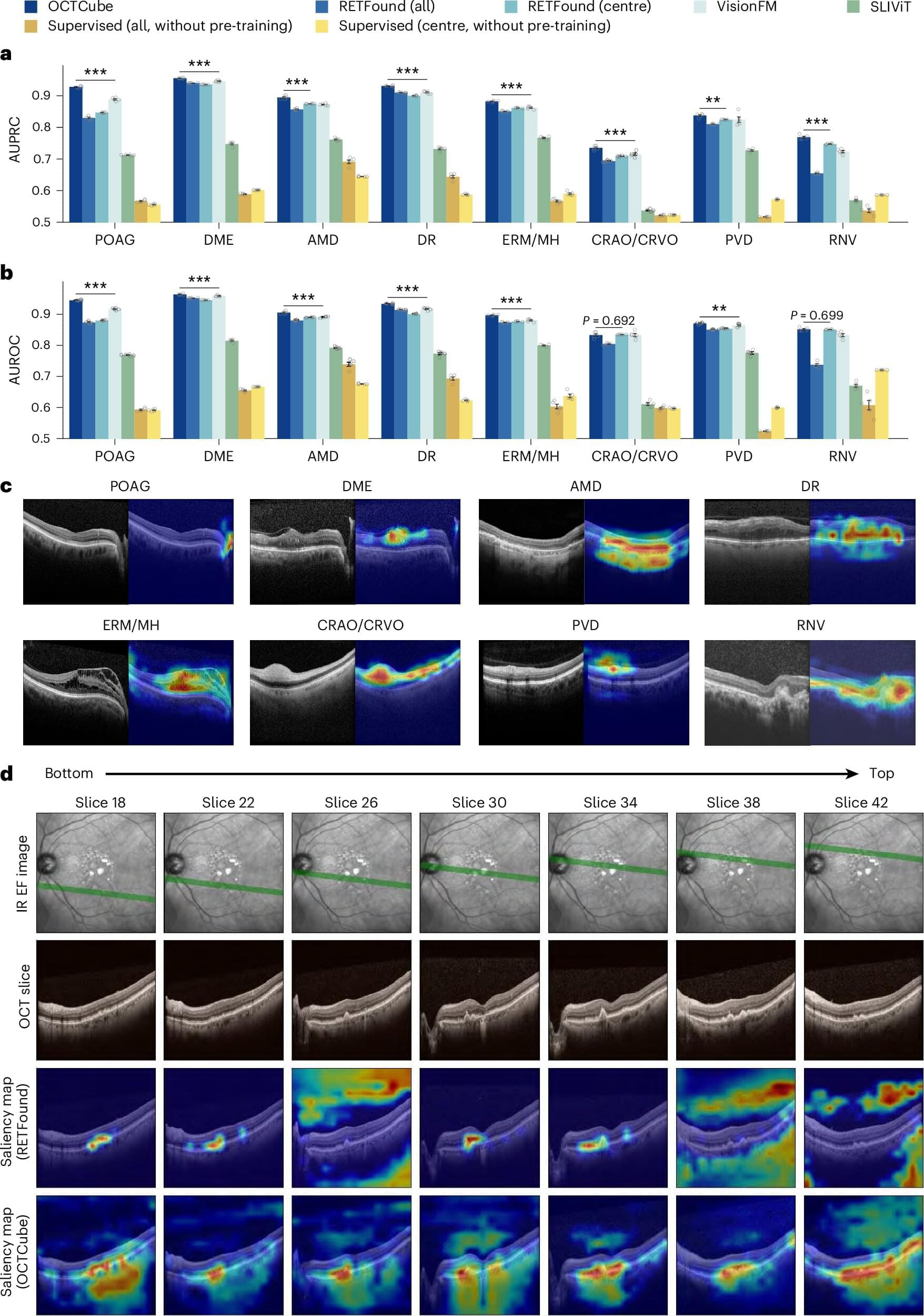
In a new study, the researchers found that, compared with older models, the new AI system more accurately identified eight different retinal diseases, including age-related macular degeneration, a common disease that damages the retina and is the leading cause of blindness in people over 50. It also was more accurate in its predictions of how fast a severe form of this condition, called geographic atrophy, would progress.