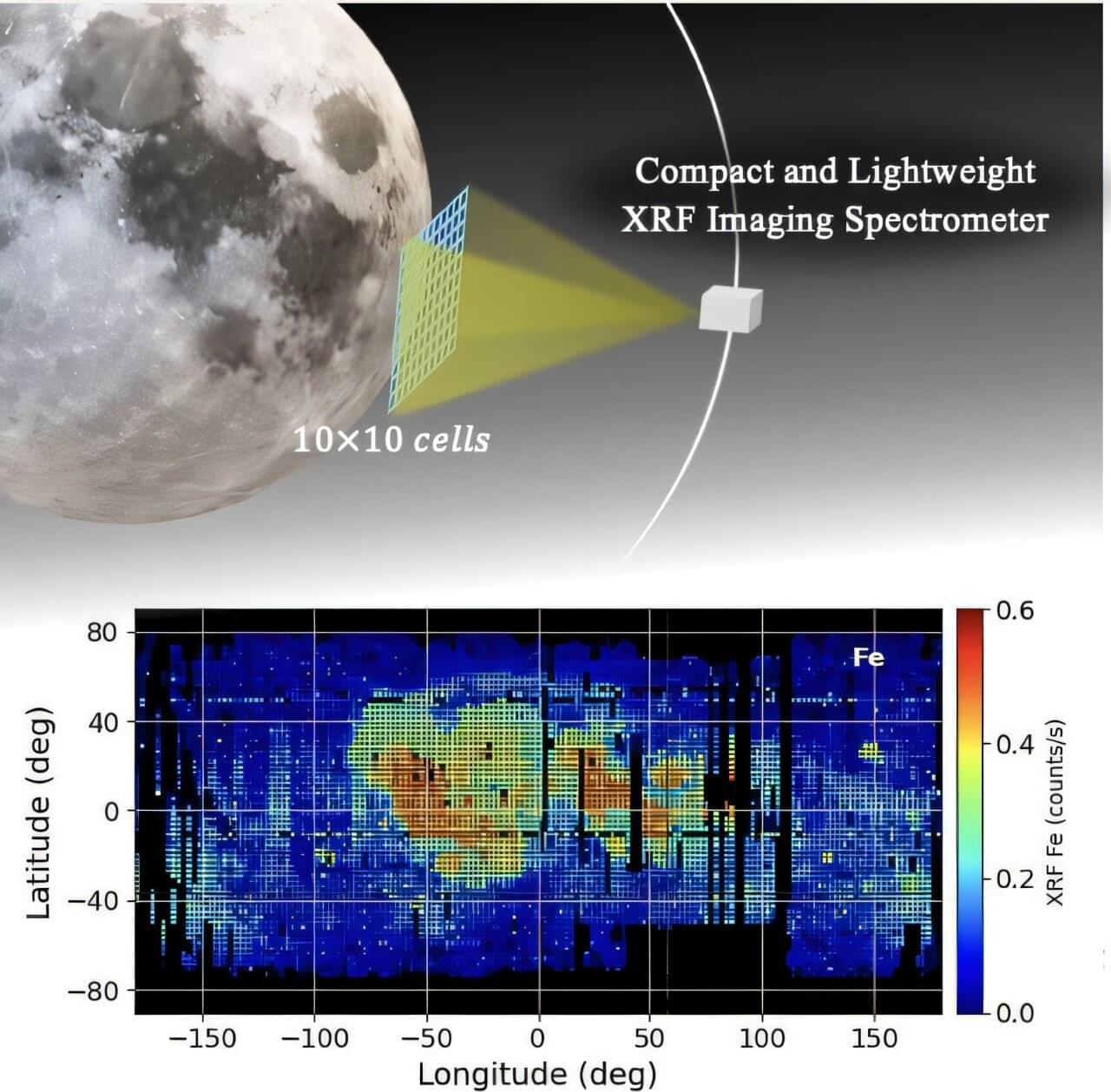
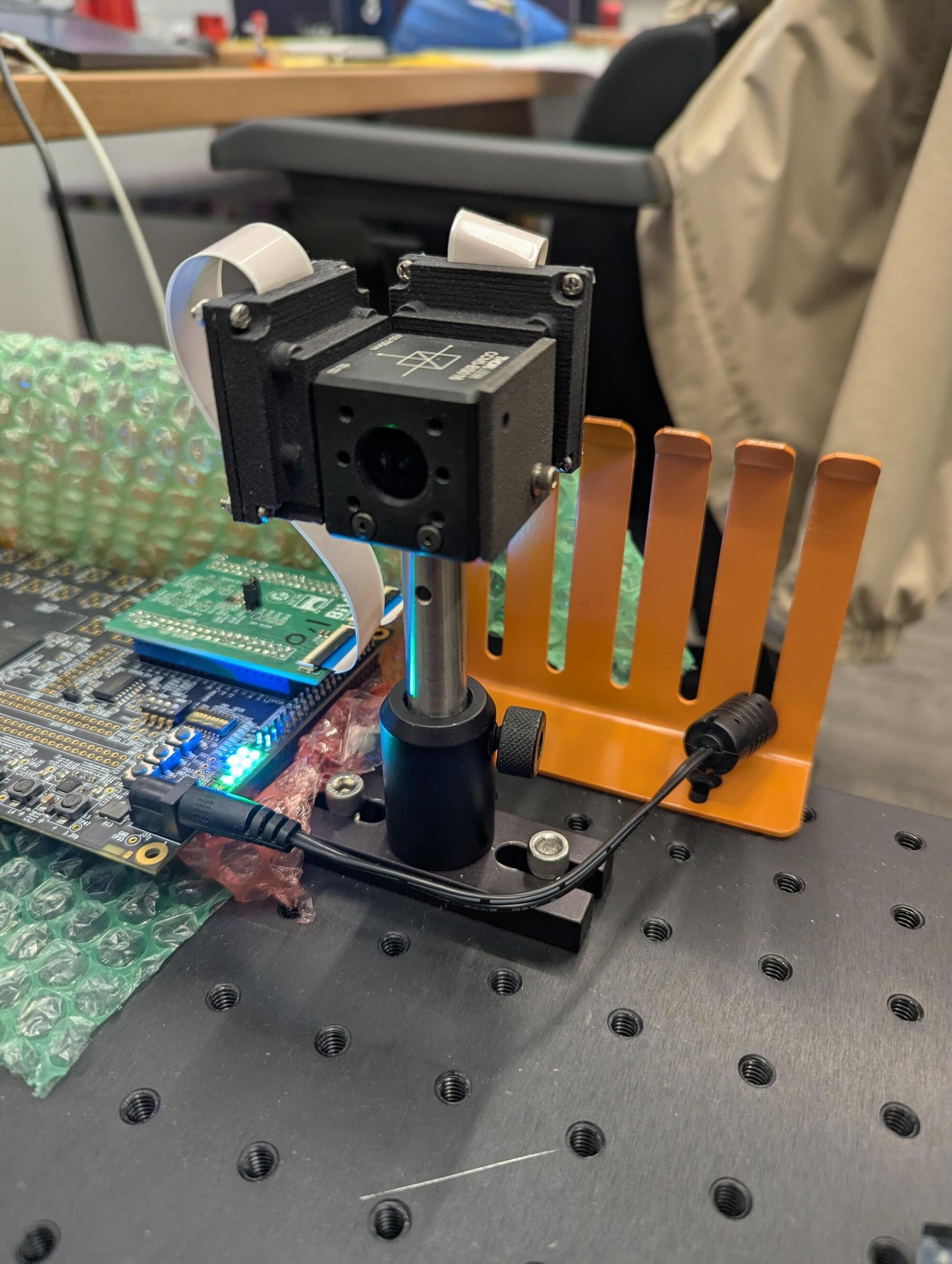
Researchers from Tokyo Metropolitan University have used simulations to show that a newly developed, compact X-ray telescope could be used to map the chemical composition of the entire lunar surface, a vital breakthrough for understanding its geological evolution. Detailed modeling of the detector and a realistic satellite mission show that two years would be enough to map five key elements, while an array of 5-by-5 detectors could improve resolution and get results faster.
The geological evolution of the moon remains a mystery to scientists. This reflects how challenging it is to get accurate information, such as a complete map of the geochemistry of the lunar surface. Since we cannot readily go and collect samples from anywhere, scientists use a technology known as X-ray fluorescence imaging, in which detectors directed at the moon are used to pick up X-rays released by specific elements when they are hit by solar rays.
While observations during the Apollo and Chandrayaan missions have successfully yielded partial maps, we are nowhere near a comprehensive map that might illuminate lunar geology. This is due to significant technical challenges, including a lack of sufficient illumination by solar rays during the lifetime of a mission and degradation of the detector. The illumination issue is particularly pronounced in polar regions, where solar X-rays are much weaker.