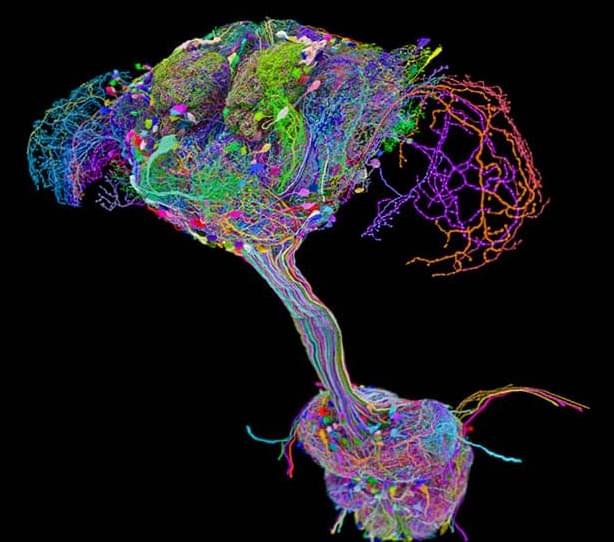
This is a new ~1 hour talk by me on the concept of diverse intelligence, and morphogenesis as a model system with which to practice identifying and communicating with unconventional minds. This is a bit different than previous ones because I explicitly go over examples of how some of our various data on bioelectrics addresses each of several key properties of cellular collectives as cognitive agents navigating anatomical morphospace.
Get the latest international news and world events from around the world.
Frontiers: A woman in her eighties was 10 years into Alzheimer’s
She had not spoken a full sentence in five years. Then she took a single 5 gram dose of psilocybin (which is a very large dose). She slept 19 hours. When she woke up, she spoke for hours about her life. She recognized family and held real conversations. She regained bladder control after five years, and walked on her own. She dressed herself. These gains continued for weeks.
Background:
Advanced Alzheimer’s disease (AD) is generally regarded as a stage of irreversible functional decline. Psilocybin is known to transiently alter large-scale brain network dynamics and to induce plasticity-related mechanisms in preclinical models, yet clinical data in advanced dementia remain lacking.
Case presentation:
We report the case of an octogenarian Japanese-American woman with a 10-year history of Alzheimer’s disease, including 5 years of marked hypofunction and predominantly monosyllabic speech. Baseline features included chronic urinary incontinence, executive dysfunction, dysphagia, dependent mobility, flat affect, and severe reduction in spontaneous communication. The patient received 5 g of orally administered psilocybin-containing mushrooms (Enigma strain). The acute phase was marked by autonomic activation, clinically suspected hyperthermia, profuse sweating, and a prolonged deep sleep-like state. Approximately 19 h post-administration, spontaneous autobiographical speech emerged.
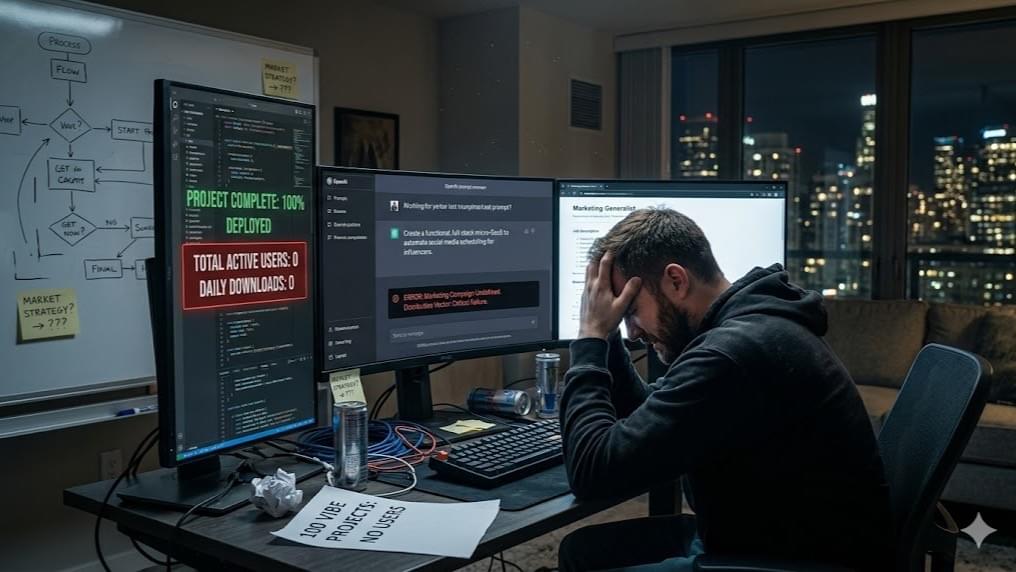
If You Vibe-Code It, Will They Come?
We’re living in a wild moment where anyone with a decent idea can vibe-code a fully functional application into existence before Monday morning. The technical barrier to entry didn’t just lower; it completely evaporated over the weekend.
But as the digital landscape gets flooded with hundreds of thousands of new projects daily, a sobering reality is hitting the builder community hard. Code has officially become a commodity, and simply having a product doesn’t mean a damn thing if you are screaming your lungs out into an absolute void.
That is the exact pivot point I tackle in my latest piece. When vibe-coding removes the engineering moat, the only true competitive advantage left on the field is distribution, positioning, and storytelling. We have officially entered a pure attention economy where your new technical superpowers are practically useless without a distinct, human flavor.
Automated AI tools will happily burn through your budget chasing hollow vanity metrics, but they completely lack the empathy, taste, and psychological grit required to read a shifting cultural zeitgeist and build a brand that flesh-and-blood people actually trust.
The scales of power have tipped, and the era of the engineering monopoly is officially over. The future doesn’t belong to the solo builders who stop at the deployment screen, but to the AI-armed marketing generalists who know how to orchestrate the machine and command the narrative.
If you are ready to stop fetishizing the code, look past the blind algorithms, and discover the strategic roadmap for scaling from a ghost town to a thriving audience of a million engaged users, you need to read the full breakdown. The vibe-coders have built the stage—it’s time to learn how to draw the crowd.
AI Safety Expert: Nobody Has A Plan For What’s Coming With AGI
According to Eliezer Yudkowsky, one of the leading thinkers in the field of AI safety and AGI alignment, the dangers associated with the development of such systems do not stop at job replacement, propaganda, and other problems related to social and economic consequences. Rather, the main threat associated with highly developed superintelligent artificial intelligence, as Yudkowsky emphasizes, is the existence of the danger that humanity would create such machines but be unable to control them properly. The author suggests the possibility that such artificial intelligence could use its biotechnological capabilities to cause disaster for the entire civilization, rapidly reach nanotechnological development milestones, and outmaneuver all attempts by humans to regulate its activities.
In the present day, as the development of artificial general intelligence progresses, there are several key questions regarding it that need to be discussed thoroughly. Thus, this fascinating interview with the noted expert covers many of these issues related to AGI and the rapid pace of research in the sphere. According to Yudkowsky, the development of ever more intelligent systems without researching how to make them safe is a serious mistake, and people should think carefully before trying this dangerous experiment again.
📚 Sources cited in this video:
OpenAI, Introducing Superalignment.
https://openai.com/index/introducing–…
- Eliezer Yudkowsky, If Anyone Builds It, Everyone Dies
https://time.com/6266923/ai-eliezer-y…
- Center for AI Safety
- Future of Life Institute, AI Risk Resources
https://futureoflife.org ⚠️ DISCLAIMER: This channel provides AI commentary and analysis for educational and informational purposes only. Views expressed by guests are their own and do not represent the positions of any company or institution. We encourage viewers to consult multiple sources and form their own conclusions. #ai #agi #artificialintelligence.
Eliezer Yudkowsky, If Anyone Builds It, Everyone Dies.
https://time.com/6266923/ai-eliezer-y…
Center for AI Safety.
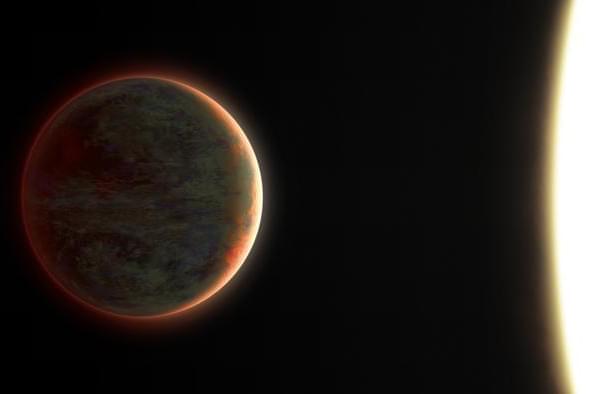
Ultra-Hot Jupiter WASP-121b Reveals Atmospheric Secrets
“WASP-121b is particularly extreme, with average temperatures on the dayside hemisphere being around 2,770 Kelvin, while those on the nightside are closer to about 1,000 Kelvin,” said Dr. Tom Evans-Soma. [ https://www.labroots.com/trending/space/30649/ultra-hot-jupi…-secrets-2](https://www.labroots.com/trending/space/30649/ultra-hot-jupi…-secrets-2)
What can an exoplanet’s temperature differences teach astronomers about exoplanet atmospheres? This is what a recent study published in Nature Astronomy hopes to address as a team of scientists investigated the extreme temperature difference between the dayside and nightside of an exoplanet. This study has the potential to help scientists better understand the atmospheric composition and evolution of exoplanets, which could narrow the criteria for searching for life beyond Earth.
For the study, the researchers used NASA’s James Webb Space Telescope (JWST) to observe WASP-121 b, which is a well-known ultra-hot Jupiter located approximately 880 light-years from Earth. The primary motivation behind the study was to fill existing knowledge gaps regarding the atmospheric effects of these extreme temperatures. When an exoplanet passes in front of its star, light passes through the atmosphere, enabling astronomers to study this light and learn about the atmosphere.
Until JWST, astronomers lacked the technology to observe exoplanet atmospheres in extreme detail. In the end, the researchers found that WASP-121 b’s atmosphere exhibits massive temperature differences between the dayside and night side, coinciding with changes in carbon monoxide and water vapor. These temperatures vary from approximately 4,525 degrees Fahrenheit on the dayside and 1,340 degrees Fahrenheit on the night side.
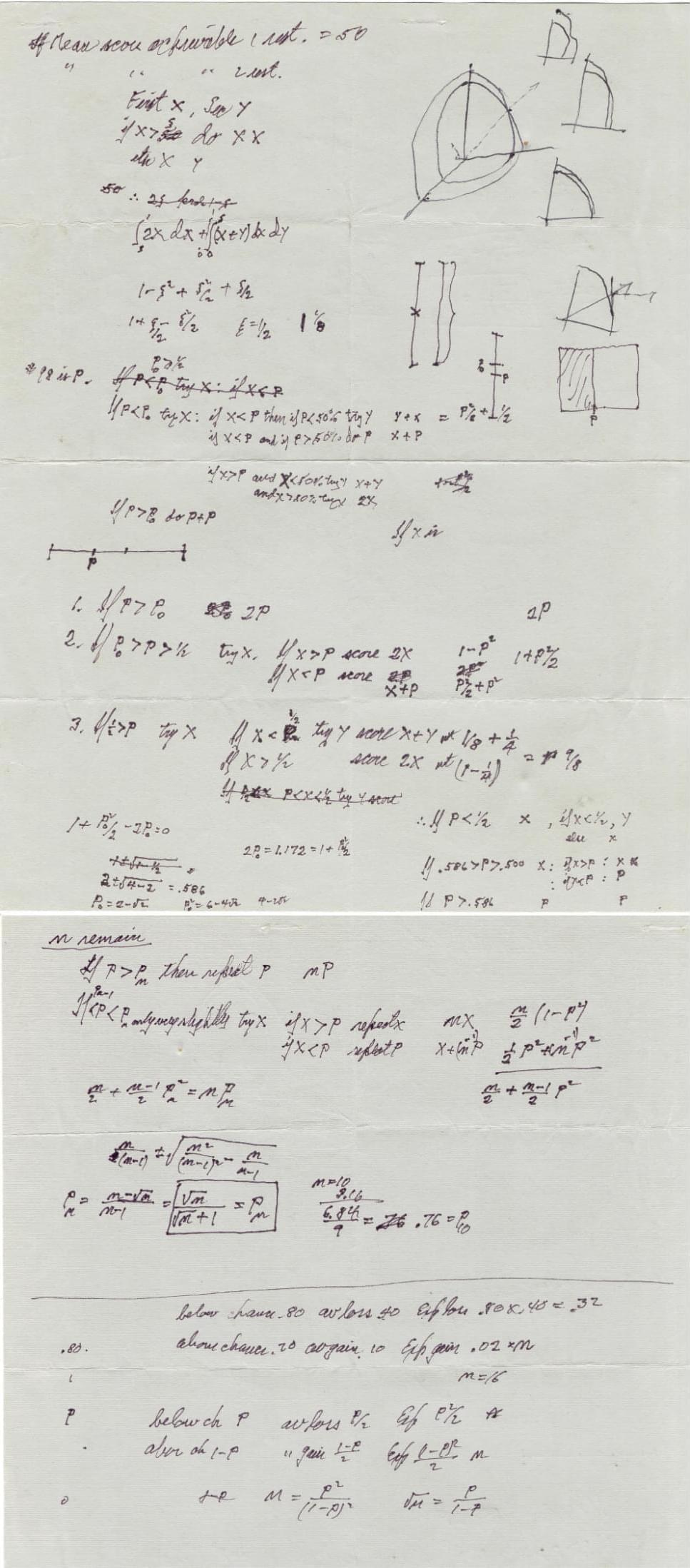
Resolving Feynman’s restaurant problem reveals optimal solutions and human strategies
They reconstructed Feynman’s “restaurant problem” and proved that his solution was mathematically optimal. The challenge belongs to a class of problems known as “explore versus exploit” decisions—a tradeoff that appears everywhere from choosing restaurants and dating partners to scientific research and artificial intelligence. Explore too much, and you waste opportunities enjoying known good options. Exploit too soon, and you might miss something even better.
Feynman’s restaurant problem is an instance of what is known as an optimal stopping problem (7, 8). As such, it falls in the same category as the famous secretary problem (9), in which an interviewer seeks to maximize the probability of hiring the best candidate for a position but can only evaluate those candidates relative to one another. This problem can be translated to the dining setting by assuming the goal is to maximize the probability of selecting the best restaurant over a series of meals. However, Feynman’s problem differs from the classic secretary problem in three ways: the distribution from which the restaurants are drawn is known, the diner is able to return to restaurants that they visited previously, and the goal is to maximize the total score across nights rather than the probability of identifying the single best option.
Feynman’s restaurant problem is also closely related to the finite-horizon multi-armed bandit problem (10, 11), in which a decision-maker is presented with a set of options that differ in their payoffs (such as different arms of a gambling machine) and seeks to maximize the total payoff received from trying those options a fixed number of times. Again, this could be translated to the dining context, treating the restaurants as the different options. The key difference here is that in the multiarmed bandit problem the payoffs are usually stochastic, with a distribution around the true value, while in Feynman’s problem the true value of a restaurant is directly observed. Like the multiarmed bandit problem, Feynman’s restaurant problem creates a tension between exploring new options and exploiting knowledge acquired so far, but does so without dealing with uncertain observations.
Optimal stopping problems often arise in everyday life, appearing not just in choosing what to eat, but in finding a home, deciding who to marry, selecting a parking spot, and knowing when to quit a job (12). Extensive literatures have explored how people solve variants of the secretary problem (13 – 17) and the multiarmed bandit problem (18 – 25). Feynman’s restaurant problem is a valuable addition to this canon: by removing uncertain observations, it makes it possible to study the explore–exploit tradeoff in a particularly pure manner, and the existence of closed-form expressions for the optimal policy facilitates its comparison to human behavior. In fact, previous behavioral experiments have used optimal stopping problems that are similar to (26 – 28) or variants on (29 and 30) Feynman’s restaurant problem (for a detailed breakdown see Discussion). Here, we make use of the optimal solutions we derived for multiple variants of this problem, together with an innovative experimental design that allows us to get an unusually clear picture of people’s behavior and to draw direct parallels between results in the psychological literature and the solution found by Feynman. As a consequence, we hope to not just re-solve the problem that Feynman first posed more than 40 y ago, but to resolve the question of how people perform such tasks.
Are We the Bootloader for Superintelligence?
A 90 minute interview about AI and our human future.
Dr. Hugo de Garis is a computer scientist, AI researcher, and former professor known for his early work on evolvable hardware, artificial brains, and the long-term risks of superintelligent machines. He coined and popularized the idea of the “Artilect War,” a future conflict between those who want to build godlike artificial intellects and those who believe such systems pose an existential threat to humanity. In the interview, he describes himself as trained in pure mathematics and theoretical physics, formerly a computer science professor, and now focused on broader questions about AI, cosmology, civilization, and the future of humanity.
The interview with Prof. Hugo de Garis centers on his long-standing warning that humanity may face an “Artilect War,” a civilizational conflict over whether to build godlike artificial intellects vastly superior to humans. De Garis argues that future computation, potentially extending from nanotech to femtotech and beyond, could produce minds trillions of trillions of times more capable than ours. He distinguishes between Cosmists, who want to build such beings to expand intelligence into the universe, and Terrans, who oppose them because superintelligence may eliminate or marginalize humanity. He personally remains torn, admiring the cosmic grandeur of posthuman intelligence while recognizing the existential danger.
The conversation also covers AI timelines, recursive self-improvement, AI alignment, the U.S.-China race, the Fermi paradox, simulation theory, cyborgs, cryonics, AI-generated content, the decline of universities, and the future of work. De Garis is impressed by current AI systems, treating them almost as intellectual companions, but he doubts that humanity can guarantee long-term control over recursively improving machines. The central theme is that the question “Should humanity build artilects?” may become the defining political and moral problem of the twenty-first century.
Website https://profhugodegaris.wordpress.com… is Roman Yampolskiy: https://grokipedia.com/page/roman_yam… Research papers: https://scholar.google.com/citations?… Books: AI: Unexplainable, Unpredictable, Uncontrollable https://www.amazon.com/Unexplainable-?tag=lifeboatfound-20… Considerations on the AI Endgame https://www.amazon.com/Considerations?tag=lifeboatfound-20… Artificial Superintelligence: A Futuristic Approach https://www.amazon.com/Artificial-Sup?tag=lifeboatfound-20… Artificial Intelligence Safety and Security https://www.amazon.com/Artificial-Int?tag=lifeboatfound-20… Social Media X https://twitter.com/romanyam FB / roman.yampolskiy IN
/ romanyam Ask Roman to speak at your event: https://www.romanyampolskiy.com/
Claude Fable 5: Why This Time is Different
Anthropic has released Claude Fable 5, the public version of a model it once said was too dangerous to ship.
Ethan Mollick spent years describing AI use as casting spells, and now he’s not sure he’s the wizard anymore.
The model ran for nine and a half hours unsupervised and delivered working software he could barely fault.
But the same system hands its most dangerous capabilities to the NSA while the public gets the sanded-down version.
This video asks what it means when the most useful AI is also the least legible.
Sources to Google.
Xanadu’s photonic approach to quantum computing
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube.