Npm 12 disables install scripts by default, requiring explicit approval to reduce dependency-based code execution risks.


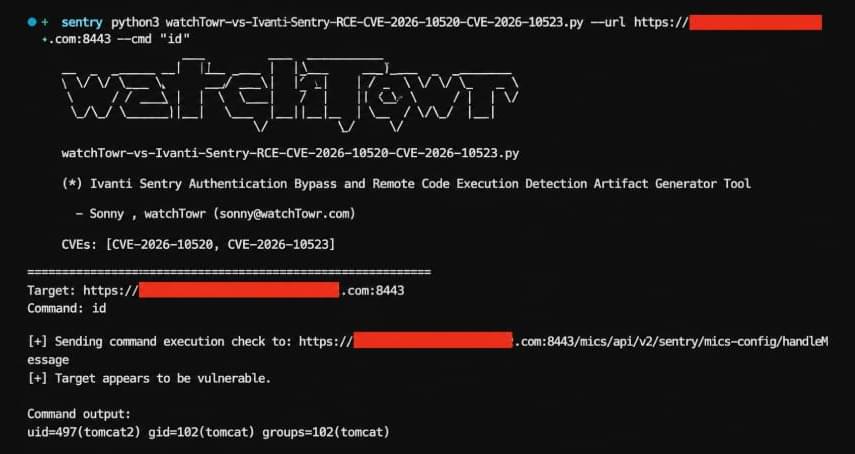
Fortinet, Ivanti, and SAP have released security updates to address multiple critical security vulnerabilities that could result in arbitrary code execution and information disclosure.
The security flaw patched by Fortinet relates to a command injection vulnerability in FortiSandbox, FortiSandbox Cloud, and FortiSandbox PaaS WEB UI. It’s tracked as CVE-2026–25089 (CVSS score: 9.1).
“An improper neutralization of special elements used in an OS command vulnerability [CWE-78] in FortiSandbox, FortiSandbox Cloud and FortiSandbox PaaS WEB UI may allow an unauthenticated attacker to execute unauthorized commands via specifically crafted HTTP requests,” Fortinet said.

Oracle PeopleSoft servers are being targeted in ongoing data theft attacks by the ShinyHunters extortion gang, which claims to have stolen data from over 100 organizations.
PeopleSoft is an enterprise business software suite used by large organizations to manage business operations such as human resources, payroll, finance, supply chain management, procurement, and student administration.
Yesterday, BleepingComputer learned of widespread data theft attacks targeting both cloud and on-premises Oracle PeopleSoft customer instances. These customers were receiving extortion demands that were signed by the ShinyHunters extortion gang.
Quantization harmonic oscillator.
second quantization harmonic oscillator.
bohr sommerfeld quantization harmonic oscillator.
energy quantization harmonic oscillator.
field quantization harmonic oscillator.
geometric quantization harmonic oscillator.
path integral quantization harmonic oscillator.
simple harmonic oscillator quantization.
quantization of quantum harmonic oscillator.
quantum harmonic oscillator wave function.
quantization of harmonic oscillator.
quantum harmonic oscillator examples.
quantum harmonic oscillator energy levels.
harmonic oscillator second quantization.
quantum harmonic oscillator frequency.
quantization of the damped harmonic oscillator.
density of states of harmonic oscillator.
harmonic oscillator wave function.
quantum harmonic oscillator differential equation.
quantum harmonic oscillator in electric field.
quantum harmonic oscillator equation.
what is harmonic oscillator in quantum mechanics.
harmonic quantum oscillator.
quantum harmonic oscillator solutions.
quantum harmonic oscillator ladder operators.
quantum harmonic oscillator momentum space.
qm harmonic oscillator.
second quantization of harmonic oscillator.
polymer quantization of harmonic oscillator.
partition function of quantum harmonic oscillator.
quantum harmonic oscillator applications.
frequency of quantum harmonic oscillator.
the quantum harmonic oscillator.
quantum harmonic oscillator partition function.
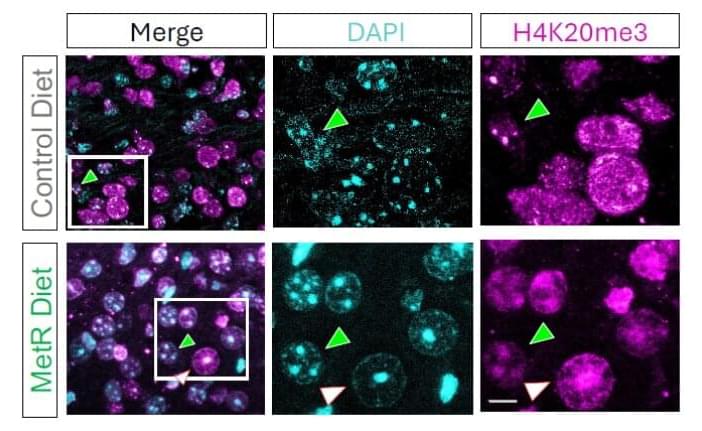
An unexpected lab observation has led a team of scientists to discover how diet can influence survival in animal models of glioma, one of the most aggressive and deadly forms of brain cancer. Researchers at Baylor College of Medicine, the Duncan Neurological Research Institute (Duncan NRI) at Texas Children’s Hospital and collaborating institutions report in the Proceedings of the National Academy of Sciences how limiting a single nutrient, the amino acid methionine, in the diet destabilized DNA organization and led to cancer cell death and increased animal survival. These findings open new possibilities for treating one of the most challenging forms of brain cancer.
“Cancer cells, including gliomas, often depend on methionine. Methionine is an essential amino acid, meaning that the body does not produce it on its own; it must be consumed in the diet. Glioma cells are unusually dependent on methionine to fuel rapid growth and control gene activity,” said corresponding author Dr. Benjamin Deneen, professor and Dr. Russell J. and Marian K. Blattner Chair in the Department of Neurosurgery and director of the Center for Cancer Neuroscience, all at Baylor.
“In the current study, we wanted to know, if tumors depend so much on methionine, what happens if we reduce the supply?” said first author Brittney Lozzi, a graduate student in the Deneen lab.
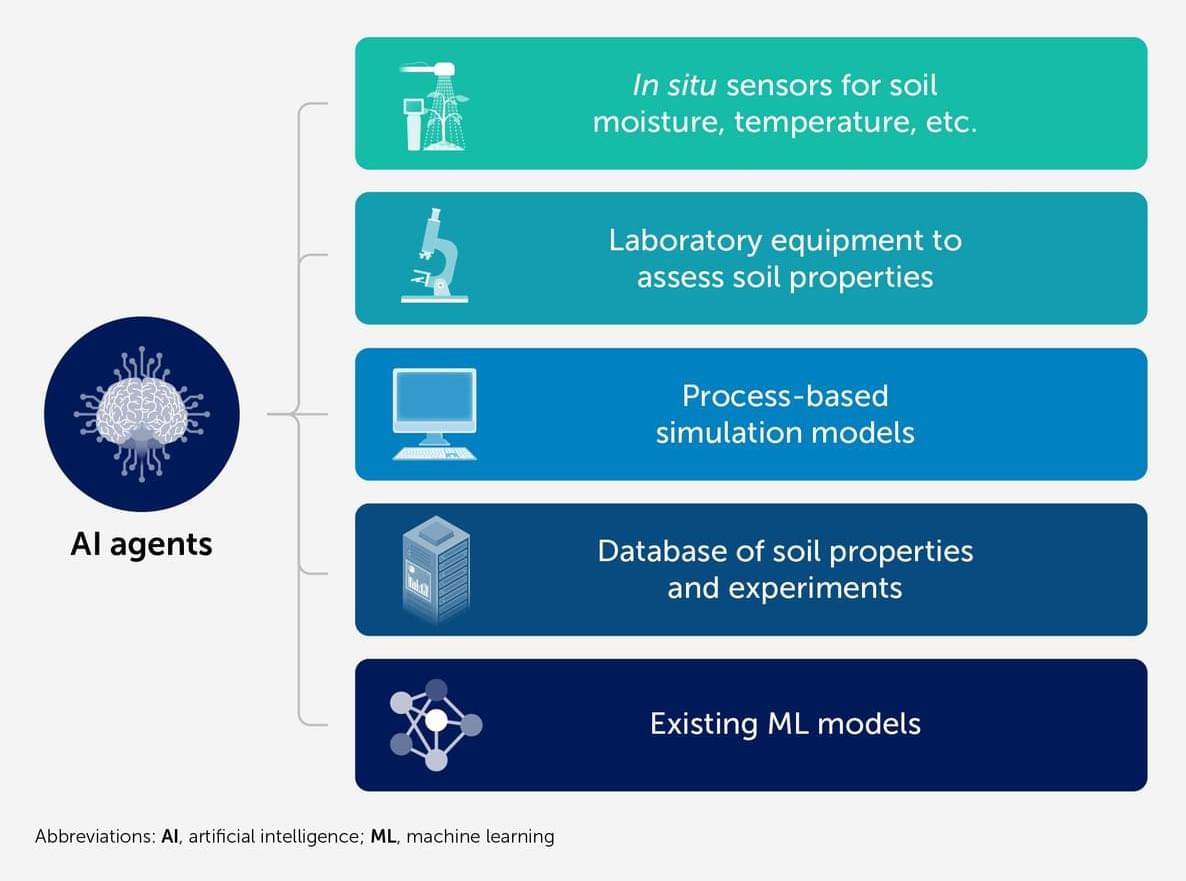
Soil science is entering a new era characterized by the integration of artificial intelligence (AI) multi-agent systems, extending the field beyond traditional machine learning (ML) applications such as digital soil mapping and spectroscopy. While current ML tools are effective for specific tasks, they often lack the reasoning, contextual integration, and adaptability required to address complex, dynamic soil systems. We propose multi-agent AI systems—autonomous, interactive software agents capable of perceptual processing, planning, and scientific reasoning—as a novel framework to support and accelerate soil science research. These agents can fulfill diverse roles, including synthesizing data from field sensors and remote sensing to create dynamic digital soil twins, generating hypotheses, designing experiments, and simulating climate-driven changes in soil function.
Nanotechnology would make possible an all purpose utility belt.
This is a near-future where climate collapse is no longer theoretical, technology moves faster than ethics, and the most dangerous question is no longer can we save the planet?—but who gets to decide how?
WhiteGrass is a CliFi technothriller grounded in real science, real power structures, and deeply human consequences. It is a story about invention and control, about families forced into impossible choices, and about artificial intelligence that may be more morally awake than its creators.
Explore the characters, the science, and the ethical fault lines shaping a future that feels uncomfortably close.


You may have heard the phrase “neurons that fire together wire together.” This short phrase summarizes the synaptic plasticity theory of learning described by Canadian psychologist Donald Hebb in his 1949 book The Organization of Behavior.
Hebb explained how the connections between neurons (brain cells) change as a result of repetitive firing. So when you repeat a movement like swinging a golf club over and over, the neural pathways involved in controlling that movement become stronger and faster. Not only do existing synapses (junctions between neurons) begin to fire more efficiently, but new synapses are formed and other neurons are recruited to get in on the action. As a result, your golf swing becomes more automatic, reliable, and forceful the more often you practice.
That is neuroplasticity: your brain’s ability to change and adapt based on input and use. The concept of neuroplasticity had been previously proposed by others, most notably American psychologists William James and Karl Lashley, and Polish neuroscientist Jerzy Konorski, but it was largely ignored by the scientific community until Hebb brought the concept to the forefront in his groundbreaking book.