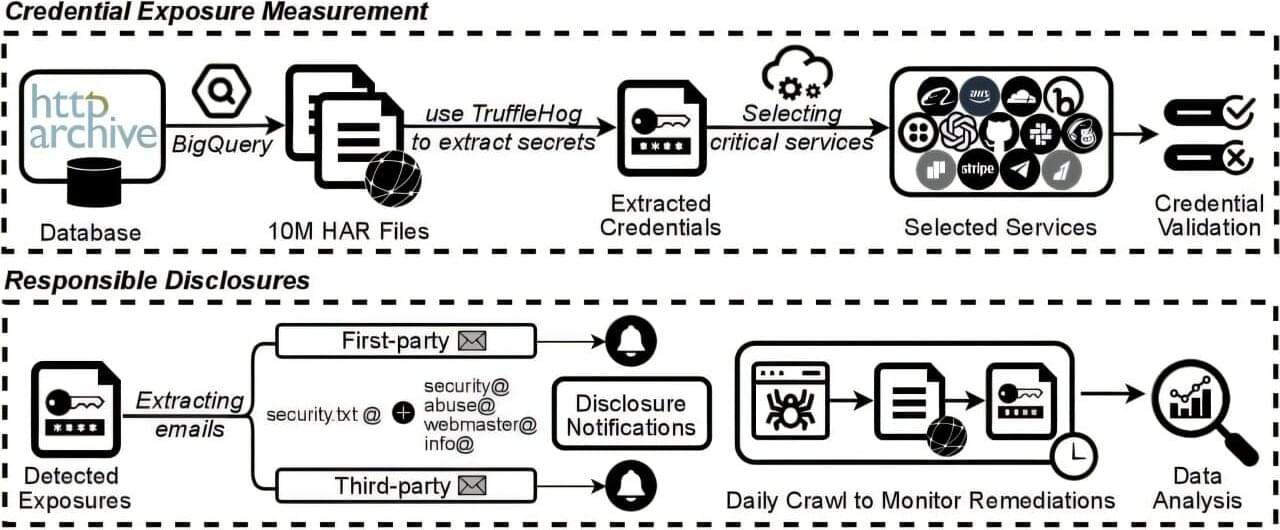
Researchers have discovered a major security leak hiding in plain sight on the internet that could expose the personal data and financial records of millions of people. In a paper published on the arXiv preprint server, Nurullah Demir of Stanford University and colleagues analyzed 10 million websites to see how often API (application programming interfaces) credentials are exposed. These are digital keys or tokens that enable different software programs to communicate and are often used to process bank payments and access cloud storage.
The team used a huge database called the HTTP Archive, which tracks how millions of real websites work. They looked at live, running versions of sites to monitor how data is processed as pages load.
By examining the websites while they were active, the researchers identified API credentials that appear only when a user visits a site. These credentials are specific strings of text that a website uses to identify itself to services like banks or cloud providers.