Outdated BIOS firmware in Illumina iSeq 100 allows attackers to disable devices or install malware, threatening critical genetic research and vaccine.


In a groundbreaking development poised to reshape the landscape of quantum computing, D-Wave Systems has announced their latest innovation: the Advantage2 quantum processor. As the industry grapples with an ever-increasing demand for computational power, this announcement signals a pivotal moment in the quest to harness the full potential of quantum technology.
Game-Changing Technology The Advantage2 processor boasts a staggering 7,000 qubits, significantly surpassing its predecessors and setting a new benchmark for quantum performance. This advancement is expected to enhance quantum annealing processes, thereby accelerating solutions for complex optimization problems that classical computers struggle to handle efficiently.
Pioneering Quantum Real-World Applications D-Wave is focusing on addressing real-world challenges across various sectors, including logistics, pharmaceuticals, and cybersecurity. By providing unparalleled computing speed, the Advantage2 aims to facilitate breakthroughs in drug discovery and materials design, and to optimize intricate supply chain networks with unprecedented efficiency.


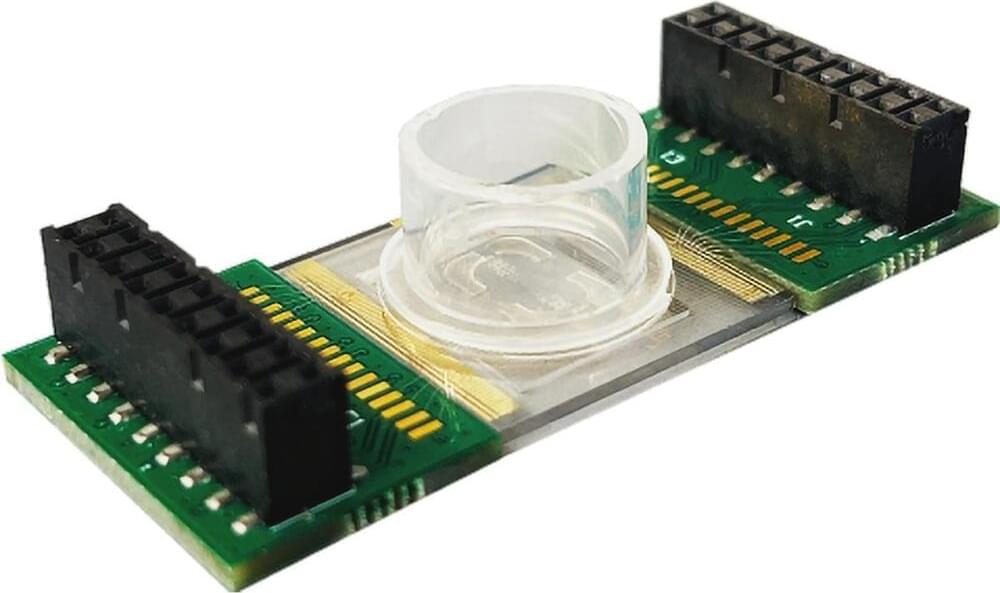
Researchers at the University of Massachusetts Amherst have developed an innovative technology inspired by the synchronization mechanism of WWI fighter aircraft, which coordinated machine gun fire with propeller movement. This breakthrough allows precise, real-time control of the pH in a cell’s environment to influence its behavior. Detailed in Nano Letters, the study opens exciting possibilities for developing new cancer and heart disease therapies and advancing the field of tissue engineering.
“Every cell is responsive to pH,” explains Jinglei Ping, associate professor of mechanical and industrial engineering at UMass Amherst and corresponding author of the study. “The behavior and functions of cells are impacted heavily by pH. Some cells lose viability when the pH has a certain level and for some cells, the pH can change their physiological properties.” Previous work has demonstrated that changes of pH as small as 0.1 pH units can have physiologically significant effects on cells.

The U.S. Department of Health and Human Services (HHS) has proposed updates to the Health Insurance Portability and Accountability Act of 1996 (HIPAA) to secure patients’ health data following a surge in massive healthcare data leaks.
These stricter cybersecurity rules, proposed by the HHS’ Office for Civil Rights (OCR) and expected to be published as a final rule within 60 days, would require healthcare organizations to encrypt protected health information (PHI), implement multifactor authentication, and segment their networks to make it harder for attackers to move laterally through them.
“In recent years, there has been an alarming growth in the number of breaches affecting 500 or more individuals reported to the Department, the overall number of individuals affected by such breaches, and the rampant escalation of cyberattacks using hacking and ransomware,” the HHS’ proposal says.

At the end of a year when Texas employees were among those targeted by hackers, the state has awarded a multi-million-dollar contract to a company that works with entities to increase technological efficiency and offer cybersecurity protection. Science Applications International Corporation (SAIC) announced Dec. 18 that it was awarded a $170.9 million contract from the Texas Department of Information Resources (DIR) to provide cybersecurity services in protection of state networks.
SAIC, which is headquartered in Reston, Va., and has been providing security services to California, Colorado and Virginia for years, also has worked with the Air Force in deploying “a cloud-based command and control capability” to air defense sectors with the North American Aerospace Defense Command (NORAD), according to information technology news website StateScoop. It employs about 24,000 people.

2024: A year when AI, quantum computing, and cybersecurity converged to redefine our digital landscape. For those navigating these complex technological frontiers, clarity became the most critical currency.
Inside Cyber, Key moments that resonated with our community:
• Cybersecurity Trends for 2025 Diving deep into the evolving threat landscape and strategic priorities.
• AI, 5G, and Quantum: Innovation and Cybersecurity Risks Exploring the intersection of emerging technologies and security challenges https://lnkd.in/ex3ktwuF
• PCI DSS v4.0 Compliance Strategies Practical guidance for adapting to critical security standards https://lnkd.in/eK_mviZd.
Inside Cyber, Looking ahead to 2025, the convergence of AI, quantum computing, and cybersecurity will demand unprecedented collaboration, education, and strategic thinking. Our collective challenge is transforming potential vulnerabilities into opportunities for innovation and security.
Grateful to Georgetown University, our growing professional network, and the organizations committed to understanding and shaping our technological future.