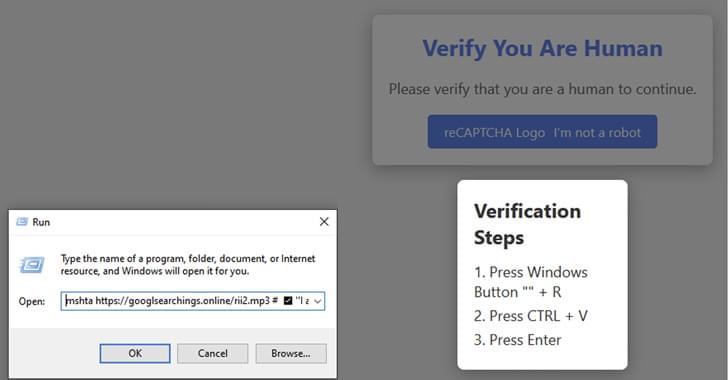
Cybersecurity researchers are calling attention to a new malware campaign that leverages fake CAPTCHA verification checks to deliver the infamous Lumma information stealer.
“The campaign is global, with Netskope Threat Labs tracking victims targeted in Argentina, Colombia, the United States, the Philippines, and other countries around the world,” Leandro Fróes, senior threat research engineer at Netskope Threat Labs, said in a report shared with The Hacker News.
“The campaign also spans multiple industries, including healthcare, banking, and marketing, with the telecom industry having the highest number of organizations targeted.”