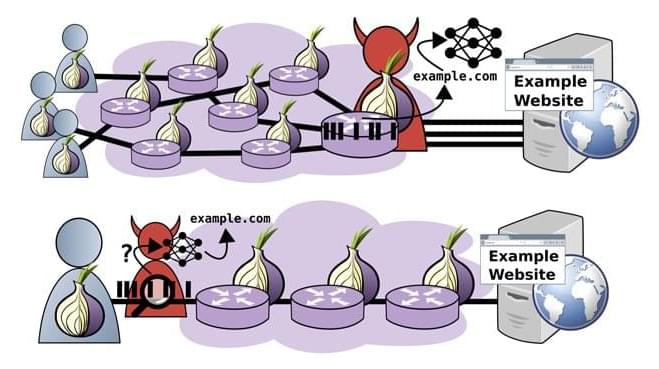
Researchers demonstrate a new fingerprinting attack on encrypted traffic using the Tor web browser.
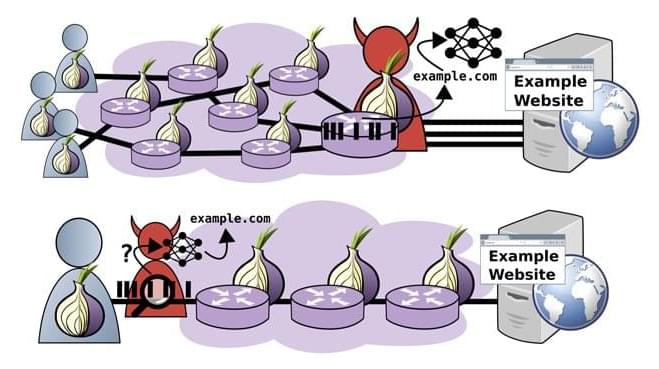
At the conference, Science History Institute postdoctoral researcher Megan Piorko presented a curious manuscript belonging to English alchemists John Dee (1527–1608) and his son Arthur Dee (1579–1651). In the pre-modern world, alchemy was a means to understand nature through ancient secret knowledge and chemical experiment.
Within Dee’s alchemical manuscript was a cipher table, followed by encrypted ciphertext under the heading “Hermeticae Philosophiae medulla”—or Marrow of the Hermetic Philosophy. The table would end up being a valuable tool in decrypting the cipher, but could only be interpreted correctly once the hidden “key” was found.
It was during post-conference drinks in a dimly lit bar that Megan decided to investigate the mysterious alchemical cipher—with the help of her colleague, University of Graz postdoctoral researcher Sarah Lang.

There’s a lot of excitement at the intersection of artificial intelligence and health care. AI has already been used to improve disease treatment and detection, discover promising new drugs, identify links between genes and diseases, and more.
By analyzing large datasets and finding patterns, virtually any new algorithm has the potential to help patients — AI researchers just need access to the right data to train and test those algorithms. Hospitals, understandably, are hesitant to share sensitive patient information with research teams. When they do share data, it’s difficult to verify that researchers are only using the data they need and deleting it after they’re done.
Secure AI Labs (SAIL) is addressing those problems with a technology that lets AI algorithms run on encrypted datasets that never leave the data owner’s system. Health care organizations can control how their datasets are used, while researchers can protect the confidentiality of their models and search queries. Neither party needs to see the data or the model to collaborate.

Traditional networks are unable to keep up with the demands of modern computing, such as cutting-edge computation and bandwidth-demanding services like video analytics and cybersecurity. In recent years, there has been a major shift in the focus of network research towards software-defined networks (SDN) and network function virtualization (NFV), two concepts that could overcome the limitations of traditional networking. SDN is an approach to network architecture that allows the network to be controlled using software applications, whereas NFV seeks to move functions like firewalls and encryption to virtual servers. SDN and NFV can help enterprises perform more efficiently and reduce costs. Needless to say, a combination of the two would be far more powerful than either one alone.

Traditional networks are unable to keep up with the demands of modern computing, such as cutting-edge computation and bandwidth-demanding services like video analytics and cybersecurity. In recent years, there has been a major shift in the focus of network research towards software-defined networks (SDN) and network function virtualization (NFV), two concepts that could overcome the limitations of traditional networking. SDN is an approach to network architecture that allows the network to be controlled using software applications, whereas NFV seeks to move functions like firewalls and encryption to virtual servers. SDN and NFV can help enterprises perform more efficiently and reduce costs. Needless to say, a combination of the two would be far more powerful than either one alone.
In a recent study published in IEEE Transactions on Cloud Computing, researchers from Korea now propose such a combined SDN/NFV network architecture that seeks to introduce additional computational functions to existing network functions. “We expect our SDN/NFV-based infrastructure to be considered for the future 6G network. Once 6G is commercialized, the resource management technique of the network and computing core can be applied to AR/VR or holographic services,” says Prof. Jeongho Kwak of Daegu Gyeongbuk Institute of Science and Technology (DGIST), Korea, who was an integral part of the study.
The new network architecture aims to create a holistic framework that can fine-tune processing resources that use different (heterogeneous) processors for different tasks and optimize networking. The unified framework will support dynamic service chaining, which allows a single network connection to be used for many connected services like firewalls and intrusion protection; and code offloading, which involves shifting intensive computational tasks to a resource-rich remote server.

Long distance quantum communication over 600 km of fiber unlocked!
Toshiba in partnership with the Japanese Tohoku University Hospital have achieved a new milestone on the road towards the quantum internet — the research team encrypted the human genome and sent it over a quantum-secure connection over 600 km of fiber.

A blockchain-based initiative from the United States Air Force will employ Constellation’s Hypergraph Network to provide data security with the Department of Defense’s commercial partners.
In a Thursday announcement, Constellation said it had been working with Kinnami Software Corporation to develop an end-to-end data security solution using blockchain encryption and distributed data management for the United States Transportation Command, Air Mobility Command’s 618th Air Operations Center, and a Civil Reserve Air Fleet partner. According to the platform, its goal is to securely exchange data with commercial partners on missions involving the operations of aircraft and ships under contract to the Department of Defense, or DoD.
The United States Transportation Command, or USTRANSCOM, allows authorities — including those in the 618th — to coordinate missions using available resources from both the military and private sector. Constellation Network’s solution may have the potential to improve the existing cybersecurity and general effectiveness.
The goal is to pre-empt the fall of traditional cryptography likely to follow the quantum revolution.
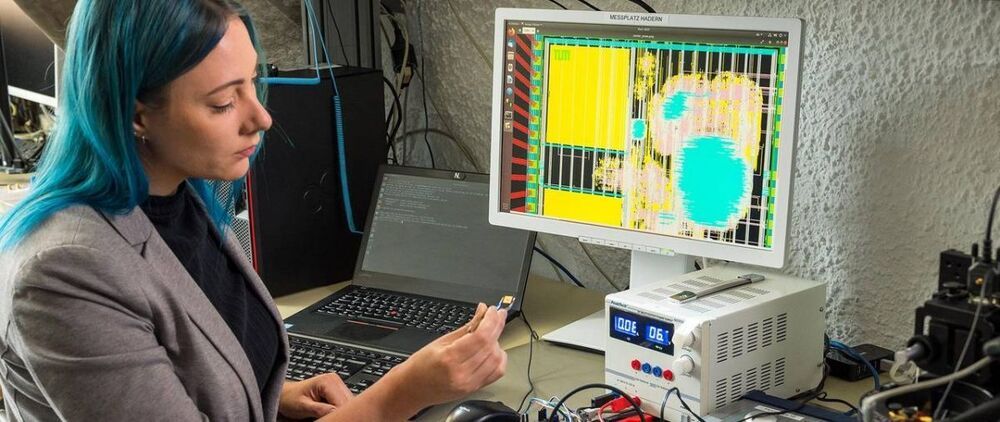
A research team with the Technical University of Munich (TUM) have designed a quantum cryptography chip aimed at the security demands of the quantum computing revolution. The RISC-V chip, which was already sent to manufacturing according to the researchers’ design, aims to be a working proof of concept for protecting systems against quantum computing-based attacks, which are generally considered to be one of the most important security frontiers of the future. Alongside the RISC-V based hardware implementation (which includes ASIC and FPGA structures), the researchers also developed 29 additional instructions for the architecture that enable the required workloads to be correctly processed on-chip.
Traditional cryptography is generally based on both the sender and receiver holding the same “unlock” key for any given encrypted data. These keys (which may include letters, digits, and special characters) have increased in length as time passes, accompanying increases in hardware performance available in the general computing sphere. The idea is to thwart brute-force attacks that would simply try out enough character combinations that would allow them to eventually reach the correct answer that unlocks the encrypted messages’ contents. Given a big enough size of the security key (and also depending on the encryption protocol used), it’s virtually impossible for current hardware — even with the extreme parallelization enabled by the most recent GPUs — to try out enough combinations in a short enough timeframe to make the effort worthwhile.

‘Some forms of encryption used today can be broken by future large-scale quantum computers, which drives a search for alternatives’
“Some forms of encryption used today can be broken by future large-scale quantum computers, which also drives a search for alternatives,” Ling said.
In a canned statement, the NUS said AWS will gain access to the university’s National Quantum-Safe Network, a vendor-neutral platform for developing technology and integrating some of it into local fiber networks.
“The understanding that we are using quantum communications technology to support experiments using existing fiber is correct,” AWS ASEAN managing director Tan Lee Chew told The Register.