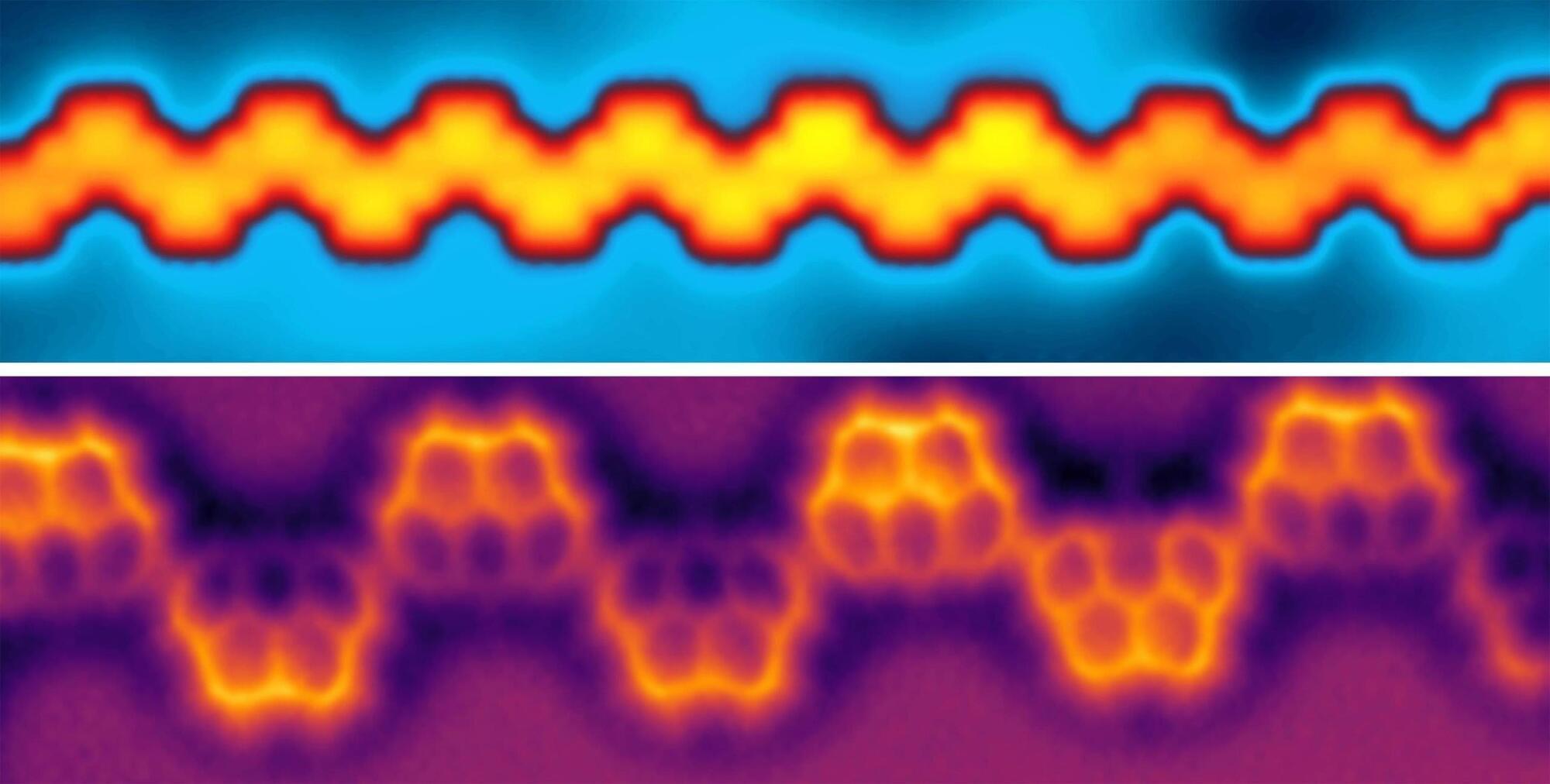
In a new paper in Nature, a team of researchers from JPMorganChase, Quantinuum, Argonne National Laboratory, Oak Ridge National Laboratory and The University of Texas at Austin describe a milestone in the field of quantum computing, with potential applications in cryptography, fairness and privacy.
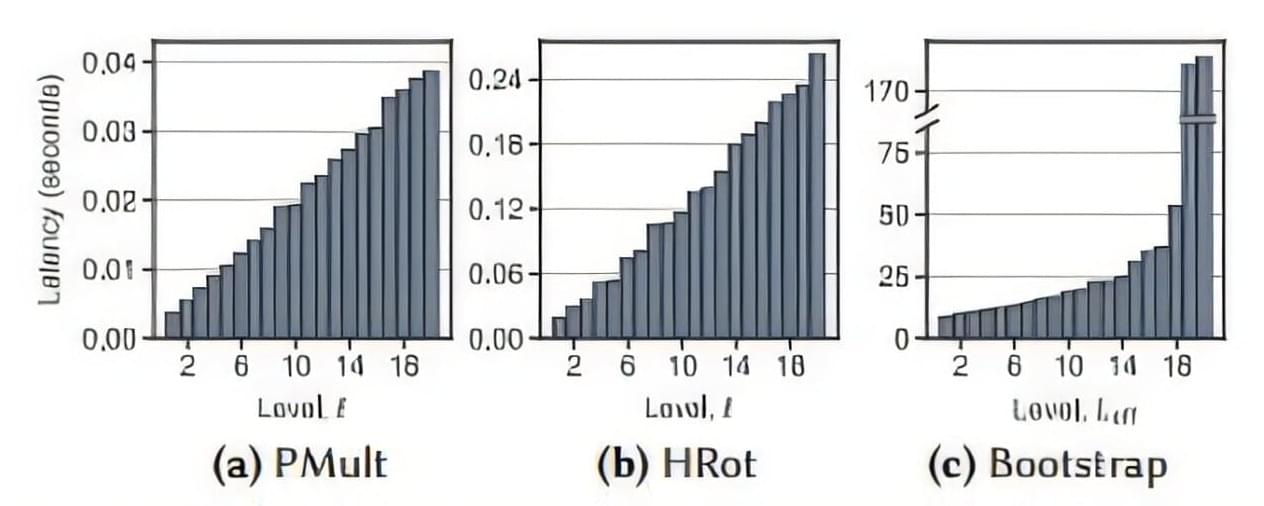
Using a 56-qubit quantum computer, they have for the first time experimentally demonstrated certified randomness, a way of generating random numbers from a quantum computer and then using a classical supercomputer to prove they are truly random and freshly generated. This could pave the way toward the use of quantum computers for a practical task unattainable through classical methods.
Scott Aaronson, Schlumberger Centennial Chair of Computer Science and director of the Quantum Information Center at UT Austin, invented the certified randomness protocol that was demonstrated. He and his former postdoctoral researcher, Shih-Han Hung, provided theoretical and analytical support to the experimentalists on this latest project.