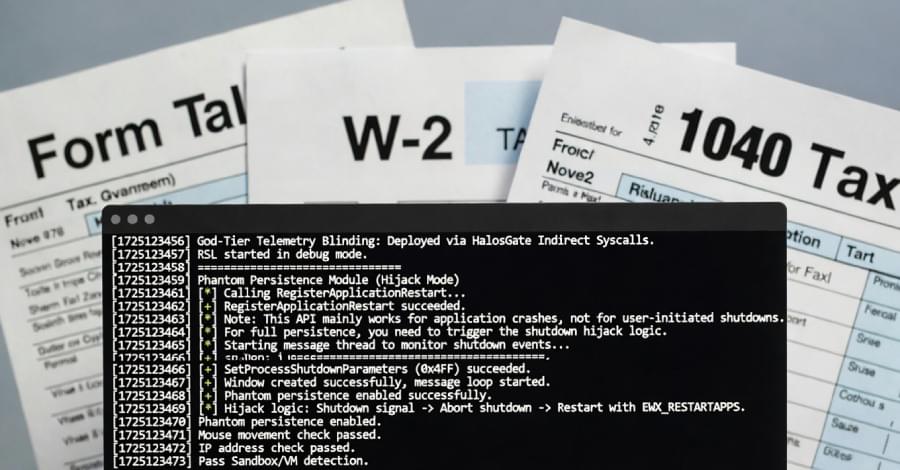
Cybersecurity researchers are warning of two cybercrime groups that are carrying out “rapid, high-impact attacks” operating almost within the confines of SaaS environments, while leaving minimal traces of their actions.
The clusters, Cordial Spider (aka BlackFile, CL-CRI-1116, O-UNC-045, and UNC6671) and Snarky Spider (aka O-UNC-025 and UNC6661), have been attributed to high-speed data theft and extortion campaigns that share a remarkable degree of operational similarities. Both hacking groups are assessed to be active since at least October 2025, with the latter a native English-speaking crew sharing ties to the e-crime ecosystem known as The Com.
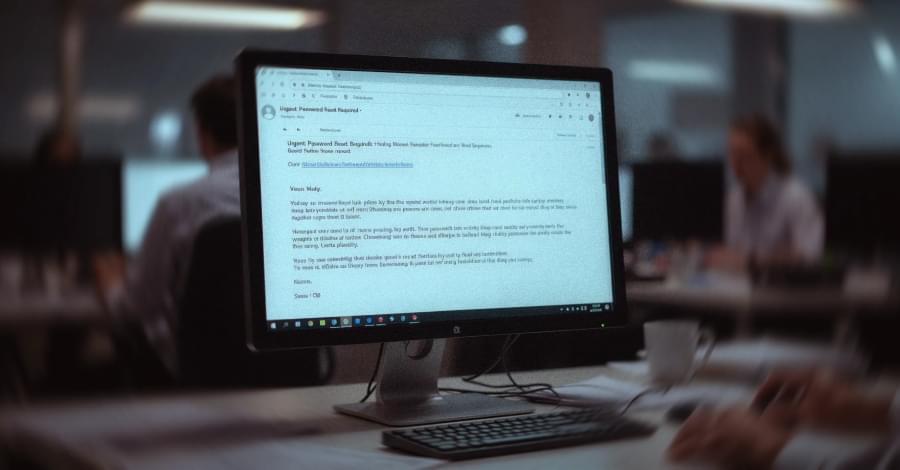
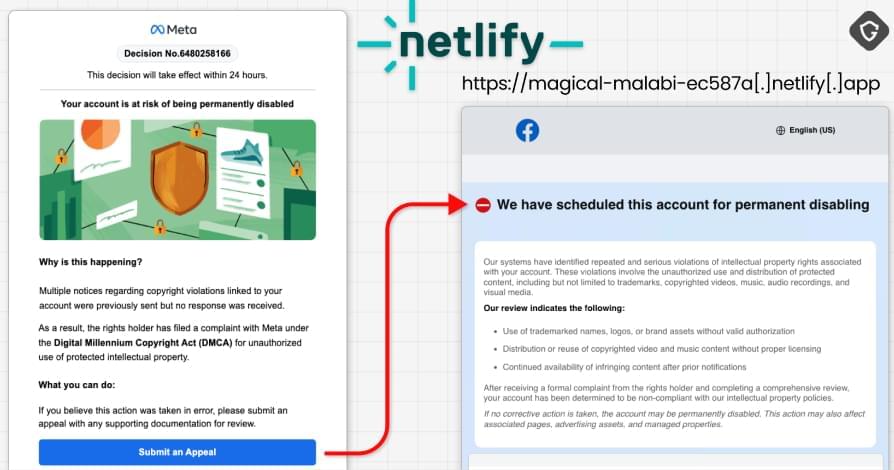
“In most cases, these adversaries use voice phishing (vishing) to direct targeted users to malicious, SSO-themed adversary-in-the-middle (AiTM) pages, where they capture authentication data and pivot directly into SSO-integrated SaaS applications,” CrowdStrike’s Counter Adversary Operations said in a report.