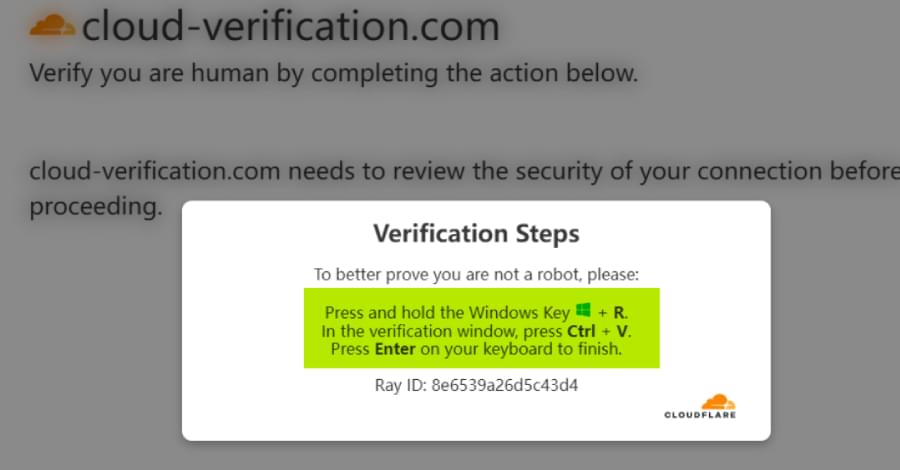
Malicious npm package downloaded 676 times stole Claude AI files via GitHub uploads, increasing AI-driven malware risks.

The Glassworm botnet targeting developers in software supply-chain attacks has been disrupted after researchers took down its resilient command-and-control infrastructure relying on Solana blockchain transactions and the BitTorrent DHT network.
In a coordinated operation conducted yesterday, CrowdStrike, Google, and The Shadowserver Foundation cut off the botnet operators’ access to four distinct command-and-control (C2) channels designed to resist conventional disruption efforts.
Glassworm campaigns have been ongoing since October 2025 and initially targeted developers with malicious OpenVSX and Microsoft VS Code extensions that stole cryptocurrency wallets and developer credentials.

Threat actors are targeting systems with high-performance computers in an ongoing cryptojacking campaign spread through a coordinated SEO poisoning operation that also manipulated AI chatbot recommendations.
The compromise occurs through malicious download pages for utility software typically installed by owners of powerful systems, like CrystalDiskInfo, HWMonitor, Display Driver Uninstaller, FurMark, K-Lite Codec Pack, and PDFgear.
Once a system is infected, the attacker gets persistent access on the machine by deploying the legitimate remote management ScreenConnect tool, which could later be used to install additional malware.

As quantum computing moves closer to large-scale deployment, new research is examining its future energy, water, and material demands.
David McCollum, an Oak Ridge National Laboratory distinguished scientist, is leading the project. McCollum is also a joint faculty professor in the Center for Energy, Transportation, and Environmental Policy (CETEP) at the Howard H. Baker Jr. School of Public Policy and Public Affairs at the University of Tennessee, Knoxville. The work aims to inform the rollout of quantum infrastructure over the coming decades. It examines technologies evolving from experimental environments to commercial-scale use. Quantum computing is expected to unlock advances in drug discovery, material science, artificial intelligence, and cybersecurity.
“Quantum computing presents extraordinary opportunities, from accelerating scientific discovery to solving complex optimization problems,” McCollum said. “At the same time, it introduces new questions about the energy, water, and materials required to operate these systems at scale. Our research aims to get ahead of those questions before resource and supply chain constraints start to bite.”

Microsoft is testing a new Defender for Endpoint capability that will automatically isolate compromised endpoints to thwart attackers’ attempts to move laterally across the network.
This is now available in preview mode and works as part of automatic attack disruption, a feature designed to contain attacks, limit their impact, and provide security teams with more remediation time.
Compromised endpoints that are automatically isolated are disconnected from the network to reduce the risk of further impact, but they retain connectivity to the Microsoft Defender for Endpoint service, which will continue to monitor the device.
If your mind could be copied perfectly into a machine, would the uploaded version still be you?
Roman Yampolskiy argues that even a flawless digital upload would only create a copy rather than preserve the original self — raising deeper questions about personal identity, continuity, and whether virtual immortality truly preserves the person who entered the machine.
0:08 Why Uploading Creates a Copy Instead of You.
1:11 The Problem of Personal Identity.
2:27 Why Continuity Matters More Than Duplication.
4:12 Internal Observation and the Sense of Self.
5:11 Why Personal Identity Is Always Changing.
Roman V. Yampolskiy is a tenured Associate Professor of Computer Science at the University of Louisville’s Speed School of Engineering, where he founded and directs the Cyber Security Lab. Widely credited with coining the term \.