Microsoft details a new ClickFix variant abusing DNS nslookup commands to stage malware, enabling stealthy payload delivery and RAT deployment.

The Washington Hotel brand in Japan has announced that that its servers were compromised in a ransomware attack, exposing various business data.
The hospitality group has established an internal task force and engaged external cybersecurity experts to assess the impact of the intrusion, determine whether customer data was compromised, and coordinate recovery efforts.
Washington Hotel, a brand operating under Fujita Kanko Inc. (WHG Hotels), is a business-focused hospitality chain with 30 locations across Japan. WHG has 11,000 rooms over its properties and has nearly 5 million guests every year.

#Quantum #CyberSecurity
Quantum computing is not merely a frontier of innovation; it is a countdown. Q-Day is the pivotal moment when scalable quantum computers undermine the cryptographic underpinnings of our digital realm. It is approaching more rapidly than many comprehend.
For corporations and governmental entities reliant on outdated encryption methods, Q-Day will not herald a smooth transition; it may signify a digital catastrophe.
Comprehending Q-Day: The Quantum Reckoning
Q-Day arrives when quantum machines using Shor’s algorithm can dismantle public-key encryption within minutes—a task that classical supercomputers would require billions of years to accomplish.

Grocery store shoppers at many chains recently ran into an unwelcome surprise: empty shelves and delayed prescriptions. In early November, Ahold Delhaize USA was the victim of a cyberattack that significantly disrupted operations at more than 2,000 stores, including Hannaford, Food Lion and Stop and Shop. Specific details of the nature of the attack have not yet been publicly released.
Because the attack affected many digital systems, some stores were not able to accept credit/debit cards, while others had to shut down online ordering. Additionally, Hannaford’s website was offline for several days. Food supply issues have lasted several weeks in some cases, especially in the New England area, illustrating the impact cyberattacks have on people’s everyday lives.

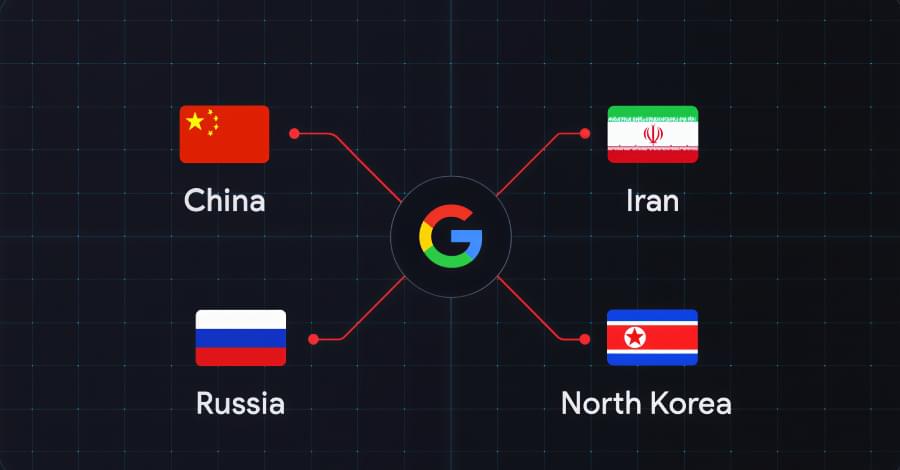


Cybersecurity researchers have discovered a malicious Google Chrome extension that’s designed to steal data associated with Meta Business Suite and Facebook Business Manager.
The extension, named CL Suite by @CLMasters (ID: jkphinfhmfkckkcnifhjiplhfoiefffl), is marketed as a way to scrape Meta Business Suite data, remove verification pop-ups, and generate two-factor authentication (2FA) codes. The extension has 33 users as of writing. It was first uploaded to the Chrome Web Store on March 1, 2025.
However, the browser add-on also exfiltrates TOTP codes for Facebook and Meta Business accounts, Business Manager contact lists, and analytics data to infrastructure controlled by the threat actor, Socket said.

