Google expands Android developer verification globally after September rollout, adding authentication and delays to sideloading to deter malware.



Cisco has suffered a cyberattack after threat actors used stolen credentials from the recent Trivy supply chain attack to breach its internal development environment and steal source code belonging to the company and its customers.
A source, who asked to remain anonymous, told BleepingComputer that Cisco’s Unified Intelligence Center, CSIRT, and EOC teams contained the breach involving a malicious “GitHub Action plugin” from the recent Trivy compromise.
The attackers used the malicious GitHub Action to steal credentials and data from the company’s build and development environment, impacting dozens of devices, including some developer and lab workstations.

Axios 1.14.1 and 0.30.4 injected malicious [email protected] after npm compromise on March 31, 2026, deploying cross-platform RAT malware.

Despite this reality, an excessive number of organizations, notably small and mid-sized businesses (SMBs), lack designated leadership in this crucial domain.
#cybersecurity #business #ciso #tech
By Chuck Brooks.
Cybersecurity is no longer an IT concern; it has become a fundamental business requirement. Viability, survivability, and ultimately commercial success are dependent on securing the devices and network for any business in the evolving digital era.

TeamPCP hackers compromised the Telnyx package on the Python Package Index today, uploading malicious versions that deliver credential-stealing malware hidden inside a WAV file.
The supply-chain attack was observed by application security firms Aikido, Socket, and Endor Labs, and was attributed to TeamPCP based on the same exfiltration pattern and RSA key seen in previous incidents caused by the same actor.
TeamPCP is responsible for multiple recent supply-chain (e.g., Aqua Security’s Trivy vulnerability scanner, the open-source Python library LiteLLM) and wiper attacks targeting Iranian systems.

A large-scale campaign is targeting developers on GitHub with fake Visual Studio Code (VS Code) security alerts posted in the Discussions section of various projects, to trick users into downloading malware.
The spammy posts are crafted as vulnerability advisories and use realistic titles like “Severe Vulnerability — Immediate Update Required,” often including fake CVE IDs and urgent language.
In many cases, the threat actor impersonates real code maintainers or researchers for a false sense of legitimacy.

Quantum computing promises to transform our world in rapid, radical and revolutionary ways: solving in seconds problems that would take classical computers years, accelerating the discovery of new medicines, creating sustainable materials, optimizing complex systems, and strengthening cybersecurity. It does so using qubits, the quantum counterparts of classical bits, which can occupy multiple states simultaneously and enable a fundamentally new kind of computation.
For example, imagine 1,000 trucks need to arrive at 10,000 different locations, each, in different parts of the country. A traditional computation model would examine each of the 10 million possible routes one by one to evaluate their efficacy, but a quantum model would be able to evaluate all those millions of different routes instantaneously.
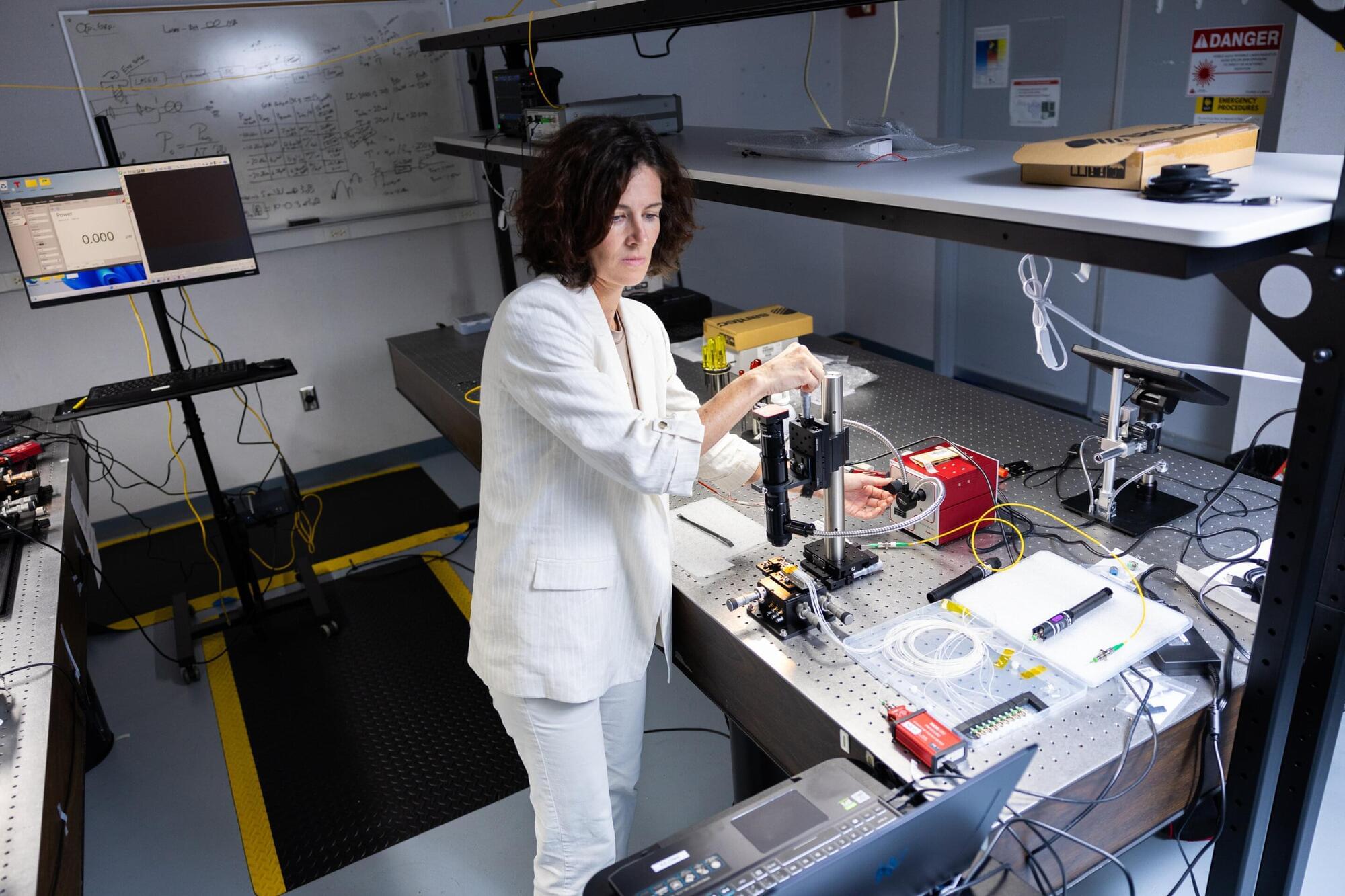
At the same time, quantum sensing is opening new frontiers in precision measurement, enabling technologies such as ultra-sensitive medical imaging and navigation systems that can detect minute changes in gravity or magnetic fields, capabilities that could allow doctors to identify diseases earlier or help vehicles navigate without GPS. UCF researchers believe the science of light, photonics, may hold the key to unlocking quantum computing’s true potential.

Threat actors are targeting TikTok for Business accounts in a phishing campaign that prevents security bots from analyzing malicious pages.
TikTok Business accounts may be targeted due to their high potential for abuse in malvertising campaigns, ad fraud, and the distribution of malicious content.
Browser threat detection and response company Push Security links the campaign to one documented last year, which targeted Google Ad Manager accounts.

A new info-stealing malware called Torg Grabber is stealing sensitive data from 850 browser extensions, more than 700 of them for cryptocurrency wallets.
Initial access is obtained through the ClickFix technique by hijacking the clipboard and tricking the user into executing a malicious PowerShell command.
According to researchers at cybersecurity company Gen Digital, Torg Grabber is actively developed, with 334 unique samples compiled in three months (between December 2025 and February 2026) and new command-and-control (C2) servers registered every week.