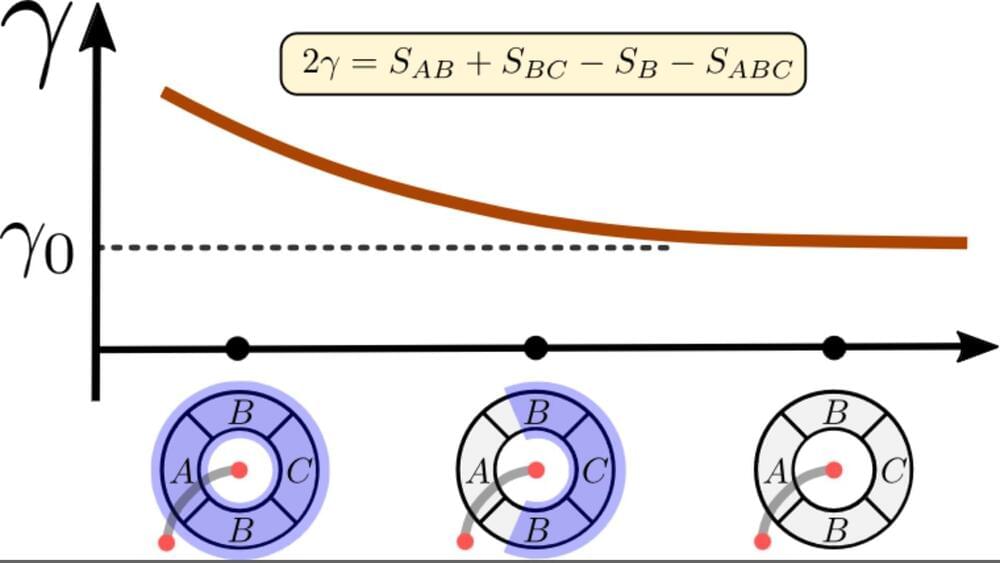
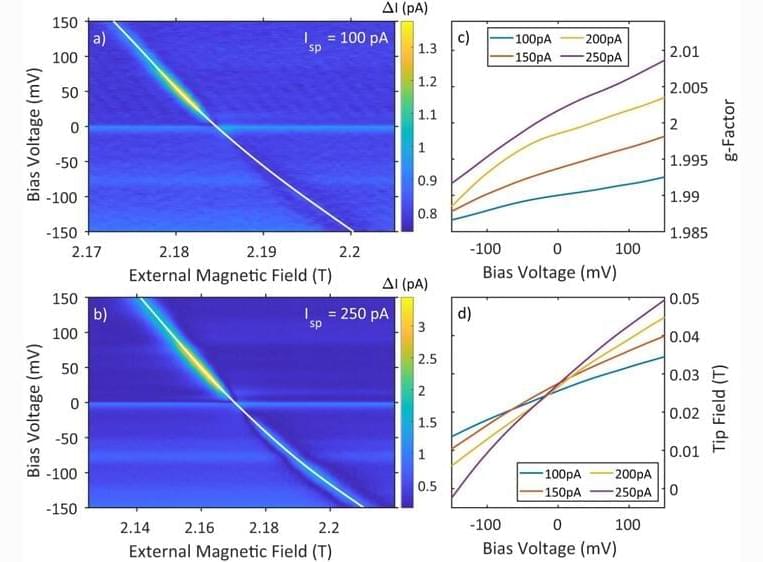
In a new study, scientists from the US and Taiwan have theoretically demonstrated the existence of a universal lower bound on topological entanglement entropy, which is always non-negative. The findings are published in the journal Physical Review Letters.
Quantum systems are bizarre and follow their own rules, with quantum states telling us everything we know about that system. Topological entanglement entropy (TEE) is a measure that provides insights into emergent non-local phenomena and entanglement in quantum systems with topological properties.
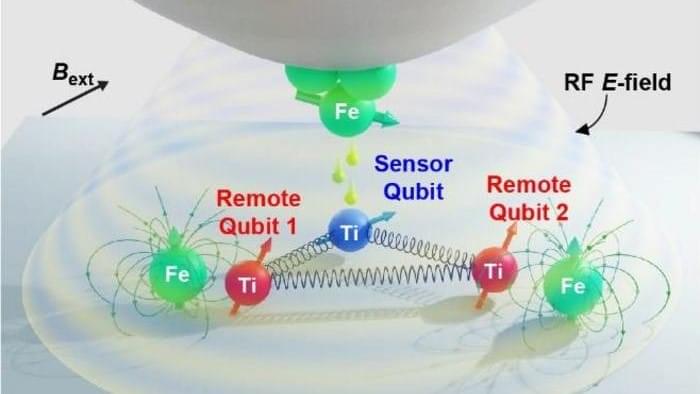
Given the fundamental role of quantum entanglement in quantum computing and various information applications, understanding TEE becomes essential for gaining insights into the behavior of quantum systems.