This website uses a security service to protect against malicious bots. This page is displayed while the website verifies you are not a bot.
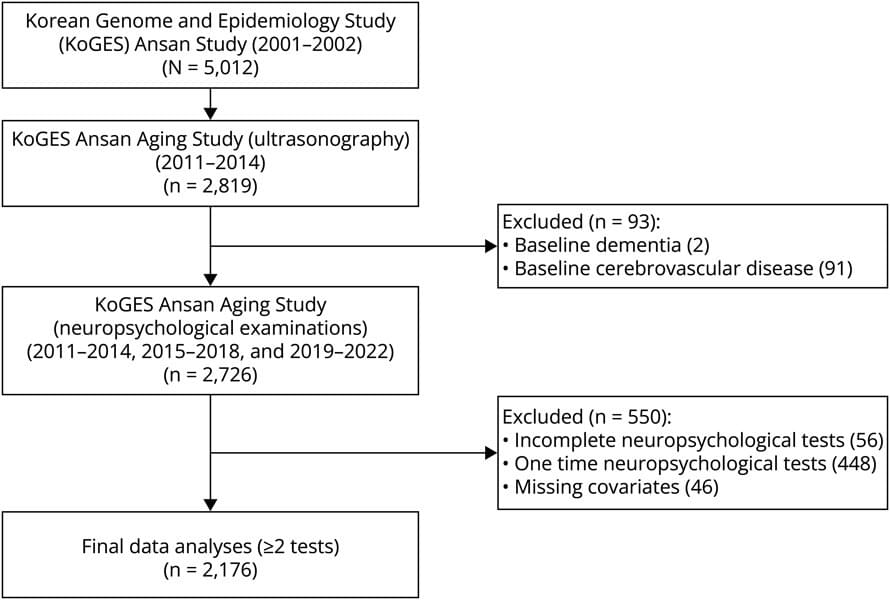
In this large cohort study, carotid plaque status at baseline was independently associated with in cognitive function decline, especially in nonverbal memory and executive functioning over 8-year follow-up period in the general population.
This website uses a security service to protect against malicious bots. This page is displayed while the website verifies you are not a bot.

Google overhauls its Android and Chrome vulnerability rewards programs, offering bounties of up to $1.5 million for the most difficult exploits while scaling back payouts for flaws that artificial intelligence (AI) has made easier to find.
The top reward of $1.5 million is reserved for zero-click Pixel Titan M2 security chip full-chain exploits with persistence, the most technically demanding attack scenario in the program, while the same exploits, but without persistence, are also eligible for up to $750,000.
On the Google Chrome side, full-chain browser process exploits on up-to-date operating systems and hardware now come with rewards of up to $250,000, plus an additional $250,128 bonus for successfully exploiting MiraclePtr-protected memory allocations.
Our second video just won a Webby’s People’s Voice Award! → http://bit.ly/3OVCA1i.
Way more thoughts, our curated newsletter, and free books (until we run out) → https://80000hours.org/iabied/
If we build something vastly smarter than us, with goals we don’t share and without knowing how to control it, we lose. That’s the core claim in the book, and I don’t think it’s all that controversial. The real question is whether that’s where we’re headed.
If this matters to you, subscribe to AI in Context. We’re working through it too.
Correction: at 14:18 I say \.
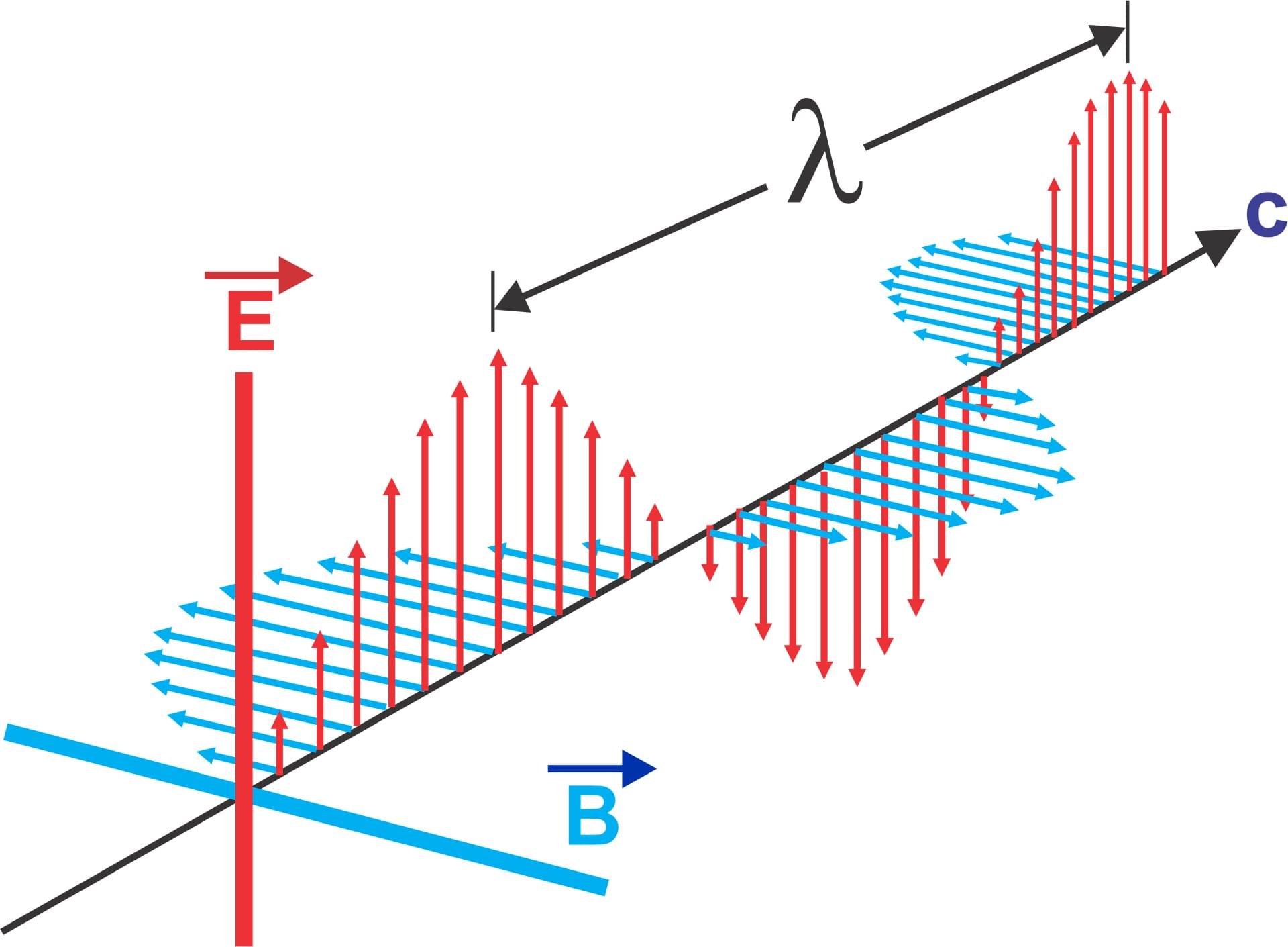
Wireless communication is about to get stronger, clearer, and more secure, thanks to a new idea from UBC Okanagan researchers. Dr. Anas Chaaban and his team in the School of Engineering are exploring a method to improve the way stacked intelligent surfaces (SIS) can process electromagnetic waves more efficiently.
SIS is an emerging alternative to conventional wireless hardware, Dr. Chaaban says, as layers of specially engineered materials are used to directly manipulate electromagnetic waves.
“Electromagnetic waves travel through special surfaces that consist of several elements. These elements mimic neurons in a computerized neural network,” Dr. Chaaban says. “As the waves move through the surface, each element changes them slightly. When the waves come out, they are captured by antennas that send the signals to digital processors for further analysis.”

Microsoft has fixed a known issue causing newly introduced Windows security warnings to display incorrectly when opening Remote Desktop (.rdp) files.
This known issue affects all supported Windows versions, including Windows 11 (KB5083768 & KB5083769), Windows 10 (KB5082200), and Windows Server (KB5082063), on devices with multiple monitors and different display scaling settings.
Microsoft addressed the bug in the optional KB5083631 preview cumulative update for Windows 11, released on Thursday, along with 34 other changes.

An exploit has been published for a local privilege escalation vulnerability dubbed “Copy Fail” that impacts Linux kernels released since 2017, allowing an unprivileged local attacker to gain root permissions.
The vulnerability is tracked as CVE-2026–31431 and was discovered by the offensive security company Theori, using its AI-driven pentesting platform Xint Code after scaning the Linux crypto/ sybsystem for about an hour.
Theori reported the finding to the Linux kernel security team on March 23, and patches became available within a week. Technical details and a proof-of-concept exploit for the flaw emerged publicly yesterday.