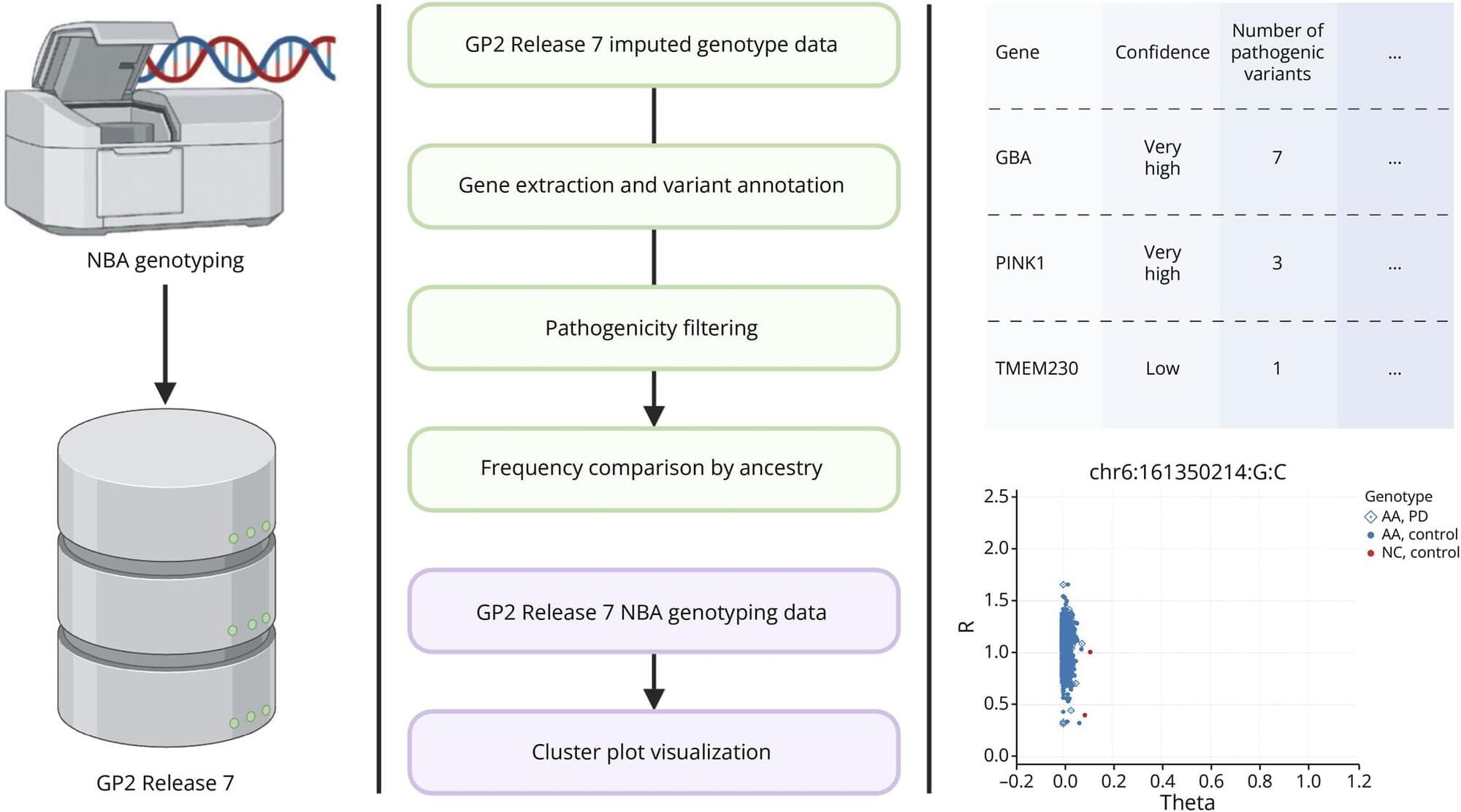
Parkinson disease pathogenic variants: cross-ancestry analysis and microarray data validation.
This website uses a security service to protect against malicious bots. This page is displayed while the website verifies you are not a bot.

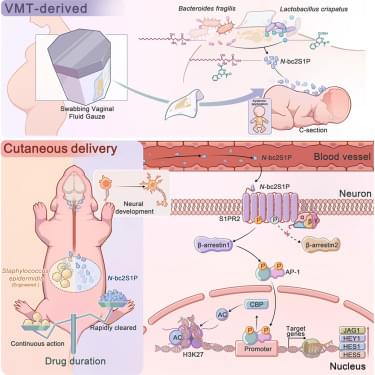
“Vaginal microbiota transfer ameliorates cesarean-associated neurodevelopmental deficits in mice via microbial N-bc2S1P synthesis on neonatal skin” http://spkl.io/6184A4yYI
CellHostandMicrobe.
This website uses a security service to protect against malicious bots. This page is displayed while the website verifies you are not a bot.
Scientists have found a way to boost terahertz technology using particles thousands of times smaller than a grain of sand. Research published in Scientific Reports by Loughborough University’s Emergent Photonics Research Center shows how a sparse layer of nanoparticles can make materials that produce terahertz radiation more efficient.
Terahertz radiation sits between microwaves and infrared on the electromagnetic spectrum and has a range of potential uses. It can “see” through materials like clothing or plastic and detect chemical fingerprints, with applications in security screening, medical imaging, materials testing, and wireless communications.
But existing devices are limited by how efficiently they can generate terahertz waves.
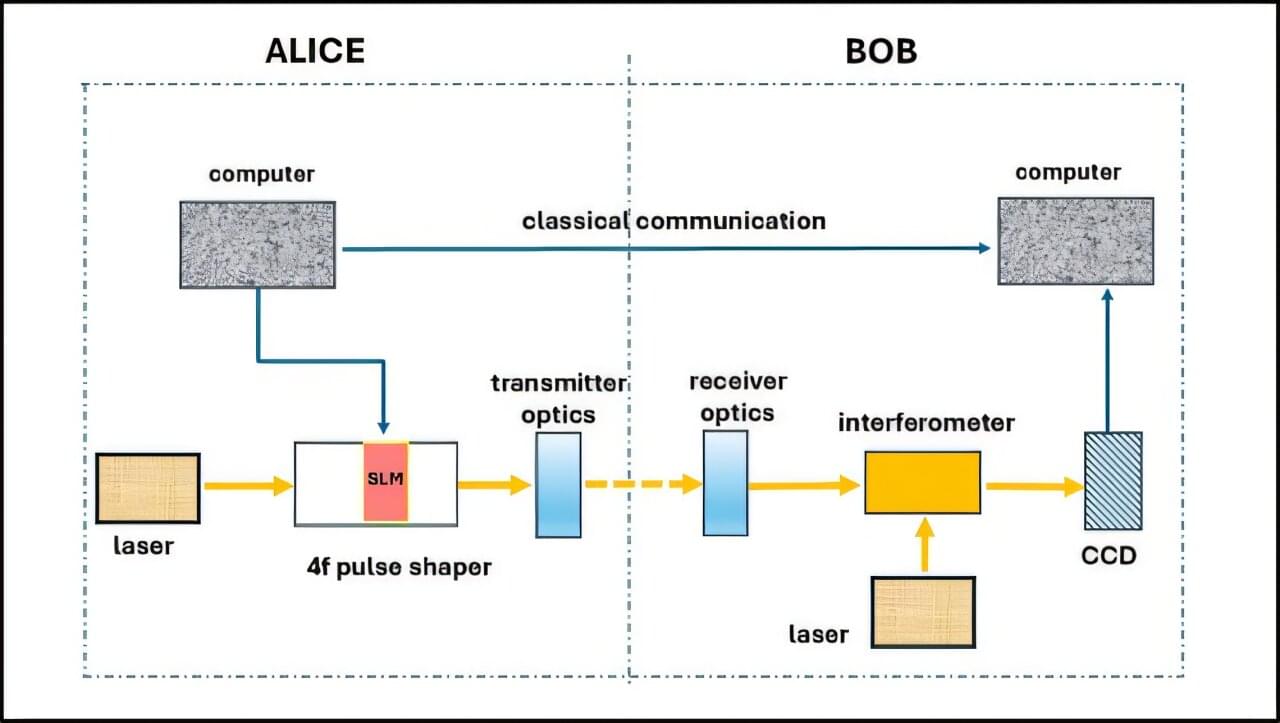
Researchers at Ben-Gurion University of the Negev have developed a new approach to secure optical communication that hides information in the physical structure of light, making it difficult for unauthorized parties to intercept or decode. The study addresses a growing challenge: advances in quantum computing are expected to weaken many of today’s encryption methods. While most security solutions rely on complex mathematical algorithms, this research adds protection earlier in the process—during the transmission of the signal itself.
The research was led by Dr. Judith Kupferman and Prof. Shlomi Arnon from the School of Electrical and Computer Engineering at Ben-Gurion University of the Negev. The findings were published in Optical and Quantum Electronics.
The researchers propose a communication method based on specially shaped light pulses, known as spatiotemporal optical vortices. These light beams are designed so that their key features are not visible in standard measurements.
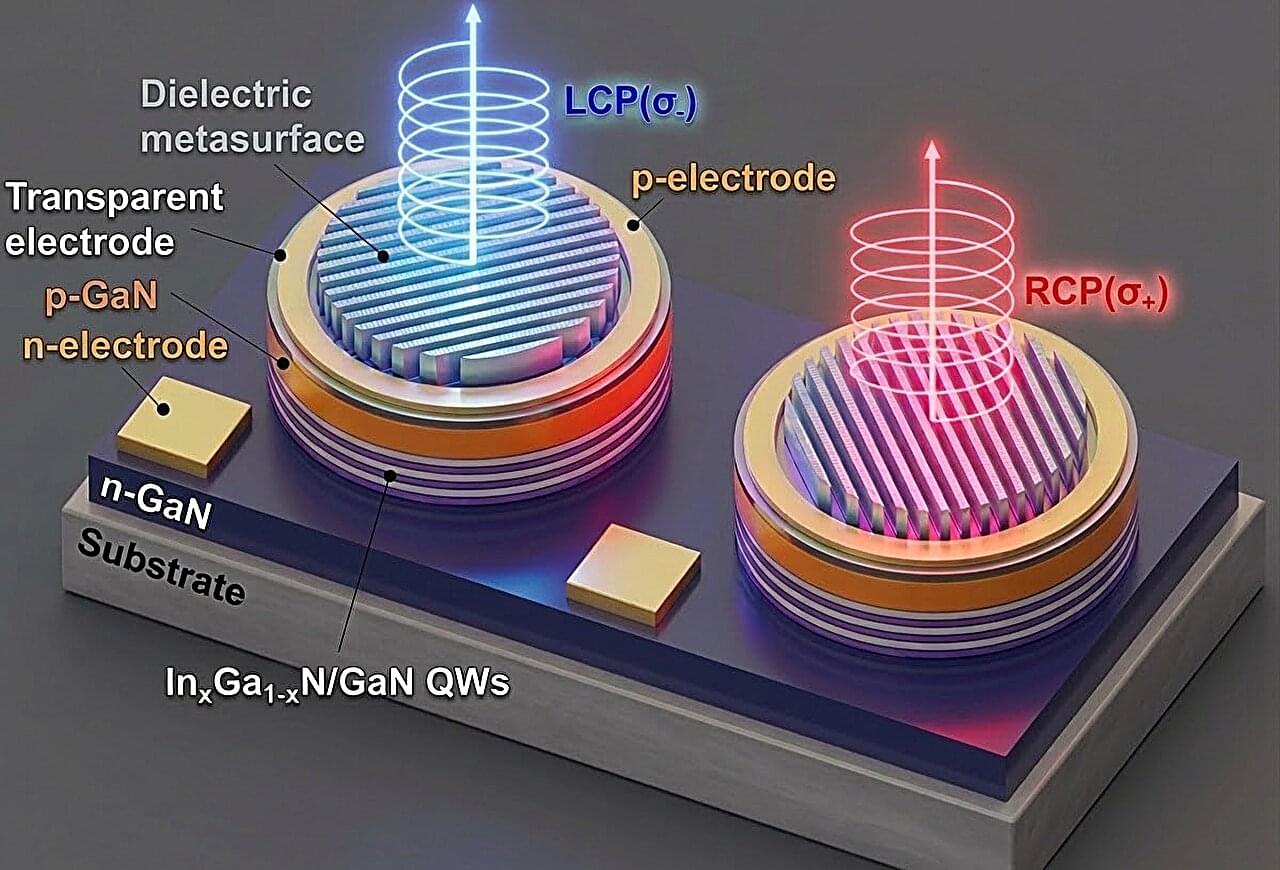
Researchers at The University of Osaka, in collaboration with ULVAC, Inc. and Ritsumeikan University, have developed a new LED structure that generates circularly polarized light from a single chip. By combining a semipolar InGaN light-emitting structure with a stripe-shaped silicon nitride metasurface, the team created a compact light source that reduces energy-conversion loss and operates at room temperature.
This advancement could help bring ultra-compact, durable light sources closer to practical use in AR/VR, 3D displays, quantum communication, and optical security. The work is published in the journal Optical Materials Express.
Circularly polarized light is useful for a wide range of next-generation technologies. However, previous circularly polarized LEDs have struggled to combine high polarization, high efficiency, durability, and scalable manufacturing. In many previous designs, only one circular polarization component can be extracted from unpolarized light, placing a theoretical limit of 50% on conversion efficiency.

A recently disclosed critical security flaw impacting nginx-ui, an open-source, web-based Nginx management tool, has come under active exploitation in the wild.
The vulnerability in question is CVE-2026–33032 (CVSS score: 9.8), an authentication bypass vulnerability that enables threat actors to seize control of the Nginx service. It has been codenamed MCPwn by Pluto Security.
“The nginx-ui MCP (Model Context Protocol) integration exposes two HTTP endpoints: /mcp and /mcp_message,” according to an advisory released by nginx-ui maintainers last month. “While /mcp requires both IP whitelisting and authentication (AuthRequired middleware), the /mcp_message endpoint only applies IP whitelisting — and the default IP whitelist is empty, which the middleware treats as ‘allow all.’”
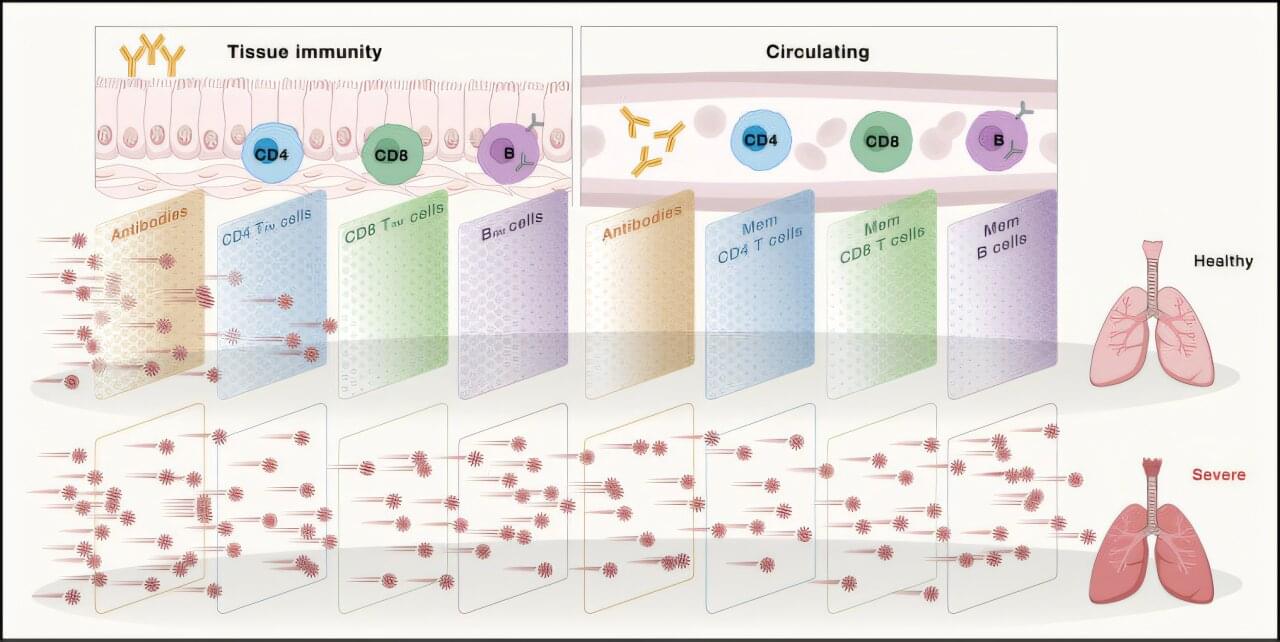
The average human has about 1.8 trillion immune cells. These cells patrol the body for bacteria, viruses, cancers, and other threats. Vaccines enhance this security system by teaching our immune cells to target specific pathogens. According to the World Health Organization, vaccine-induced immunity saves about six lives every minute. But how long does this protective immune “memory” last?
According to Shane Crotty, Ph.D., Professor and Chief Scientific Officer at La Jolla Institute for Immunology (LJI), we still have much to learn about immune memory.
“There are actually not many studies of human immune memory due to vaccines,” says Crotty. “Scientists traditionally don’t track immune memory past one year after vaccination—or even six months after vaccination—and that’s a bit of a problem.”
