NetSfere integrates cutting-edge ML-KEM encryption, providing a quantum-resistant communication platform that meets strict compliance and performance standards.



As quantum computing develops, scientists are working to identify tasks for which quantum computers have a clear advantage over classical computers. So far, researchers have only pinpointed a handful of these problems, but in a new paper published in Physical Review Letters, scientists at Los Alamos National Laboratory have added one more problem to this very short list.
“One of the central questions that faces quantum computing is what classes of problems they can most efficiently solve but classical computers cannot,” says Marco Cerezo, the Los Alamos team’s lead scientist. “At the moment, this is the Holy Grail of quantum computing, because you can count on two hands such problems. In this paper, we’ve just added another.”
Quantum computing harnesses the unique laws of quantum physics, such as superposition, entanglement and interference, which allow for information processing capabilities beyond those of classical devices. When fully realized, quantum computing promises to make advancements in cryptography, simulations of quantum systems and data analysis, among many other fields. But before this can happen, researchers still need to develop the foundational science of quantum computing.
In a global first, US scientists demonstrate quantum encryption in a live nuclear reactor using quantum key distribution approach.
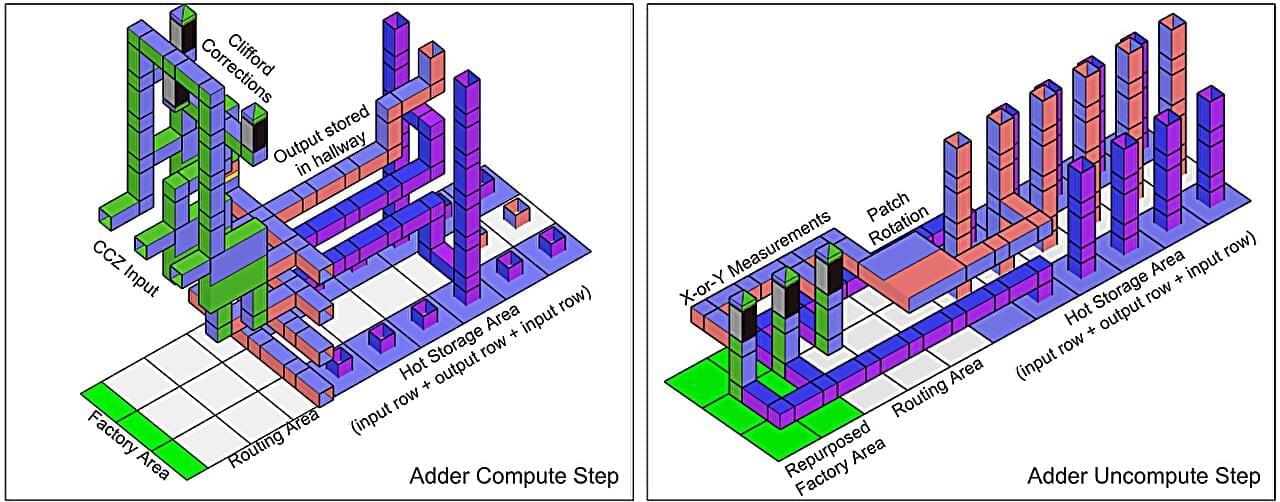
A team of researchers at AI Google Quantum AI, led by Craig Gidney, has outlined advances in quantum computer algorithms and error correction methods that could allow such computers to crack Rivest–Shamir–Adleman (RSA) encryption keys with far fewer resources than previously thought. The development, the team notes, suggests encryption experts need to begin work toward developing next-generation encryption techniques. The paper is published on the arXiv preprint server.
RSA is an encryption technique developed in the late 1970s that involves generating public and private keys; the former is used for encryption and the latter decryption. Current standards call for using a 2,048-bit encryption key. Over the past several years, research has suggested that quantum computers would one day be able to crack RSA encryption, but because quantum development has been slow, researchers believed that it would be many years before it came to pass.
Some in the field have accepted a theory that a quantum computer capable of cracking such codes in a reasonable amount of time would have to have at least 20 million qubits. In this new work, the team at Google suggests it could theoretically be done with as few as a million qubits—and it could be done in a week.

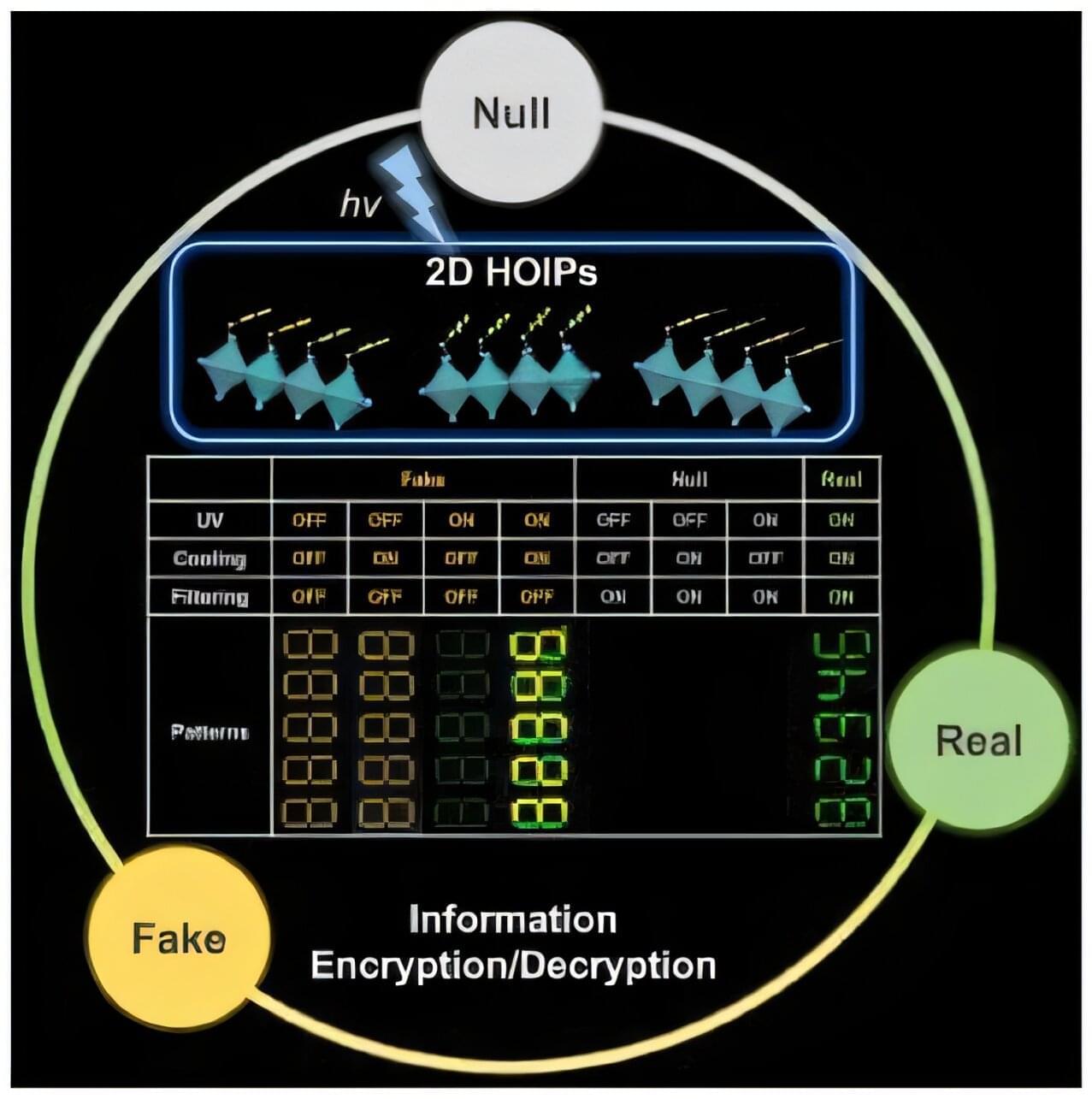
To guarantee high data security, encryption must be unbreakable while the data remains rapidly and easily readable. A novel strategy for optical encryption/decryption of information has now been introduced in the journal Angewandte Chemie by a Chinese research team. It is based on compounds with carefully modulated luminescent properties that change in response to external stimuli.
The compounds are hybrid two-dimensional organic-inorganic metal-halide perovskites, whose structure consists of inorganic layers formed from lead and iodide ions (linked PbI6 octahedra) with organic cations arranged between them. They are easy to produce, inexpensive, and printable, while demonstrating interesting optoelectronic properties.
A team led by Shenlong Jiang, Qun Zhang, and Yi Luo at the University of Science and Technology of China (Hefei) worked with three perovskites with only slight variations in their cations (phenethylammonium lead iodide perovskite (PEA)2PbI4 and its fluoridated (2-F-PEA)2PbI4 and brominated (4-Br-PEA)2PbI4 derivatives).
Monte Carlo methods, or Monte Carlo experiments, are a broad class of computational algorithms that rely on repeated random sampling to obtain numerical results. The underlying concept is to use randomness to solve problems that might be deterministic in principle. The name comes from the Monte Carlo Casino in Monaco, where the primary developer of the method, mathematician Stanisław Ulam, was inspired by his uncle’s gambling habits.
Monte Carlo methods are mainly used in three distinct problem classes: optimization, numerical integration, and generating draws from a probability distribution. They can also be used to model phenomena with significant uncertainty in inputs, such as calculating the risk of a nuclear power plant failure. Monte Carlo methods are often implemented using computer simulations, and they can provide approximate solutions to problems that are otherwise intractable or too complex to analyze mathematically.
Monte Carlo methods are widely used in various fields of science, engineering, and mathematics, such as physics, chemistry, biology, statistics, artificial intelligence, finance, and cryptography. They have also been applied to social sciences, such as sociology, psychology, and political science. Monte Carlo methods have been recognized as one of the most important and influential ideas of the 20th century, and they have enabled many scientific and technological breakthroughs.

Neuroscientists and materials scientists have created contact lenses that enable infrared vision in both humans and mice by converting infrared light into visible light. Unlike infrared night vision goggles, the contact lenses, described in the journal Cell, do not require a power source—and they enable the wearer to perceive multiple infrared wavelengths. Because they’re transparent, users can see both infrared and visible light simultaneously, though infrared vision was enhanced when participants had their eyes closed.
“Our research opens up the potential for noninvasive wearable devices to give people super-vision,” says senior author Tian Xue, a neuroscientist at the University of Science and Technology of China. “There are many potential applications right away for this material. For example, flickering infrared light could be used to transmit information in security, rescue, encryption or anti-counterfeiting settings.”
The contact lens technology uses nanoparticles that absorb infrared light and convert it into wavelengths that are visible to mammalian eyes (e.g., electromagnetic radiation in the 400–700 nm range). The nanoparticles specifically enable the detection of “near-infrared light,” which is infrared light in the 800‑1600 nm range, just beyond what humans can already see.

Physicists from Oxford have, for the first time, scaled quantum computing using distributed teleportation technology — and this could change everything. From «parallel universes» to Grover’s algorithm, from cryptography to molecular modeling — the world is entering an era where «impossible» problems
