An analysis reveals striking similarities between the BlackSuit and Royal ransomware strains.



For years, we’ve debated the benefits of artificial intelligence (AI) for society, but it wasn’t until now that people can finally see its daily impact. But why now? What changed that’s made AI in 2023 substantially more impactful than before?
First, consumer exposure to emerging AI innovations has elevated the subject, increasing acceptance. From songwriting and composing images in ways previously only imagined to writing college-level papers, generative AI has made its way into our everyday lives. Second, we’ve also reached a tipping point in the maturity curve for AI innovations in the enterprise—and in the cybersecurity industry, this advancement can’t come fast enough.

Researchers at the cybersecurity firm Eclypsium, which focuses on firmware, reported today that they have found a secret backdoor in the firmware of motherboards manufactured by the Taiwanese manufacturer Gigabyte’s components are often used in gaming PCs and other high-performance systems. Eclypsium discovered that whenever a computer with the affected Gigabyte motherboard restarts, code inside the motherboard’s firmware silently triggers the launch of an updater application, which then downloads and runs another piece of software on the machine. Researchers discovered that the hidden code was built in an unsafe manner, making it possible for the mechanism to be hijacked and used to install malware rather than Gigabyte’s intended software.
Despite the fact that Eclypsium claims the hidden code is intended to be a harmless utility to keep the motherboard’s firmware updated, researchers determined that the implementation was vulnerable. And since the updater application is activated from the computer’s firmware rather than the operating system, it is difficult for users to either delete it or even detect it on their own. In the blog post, the company details the 271 different versions of Gigabyte motherboards that the researchers think are vulnerable. According to experts, individuals who are interested in discovering the motherboard that is used by their computer may do so by selecting “Start” in Windows and then selecting “System Information.”
Users who don’t trust Gigabyte to silently install code on their machine with a nearly invisible tool may have been concerned by Gigabyte’s updater alone. Other users may have been concerned that Gigabyte’s mechanism could be exploited by hackers who compromise the motherboard manufacturer to exploit its hidden access in a software supply chain attack. The update process was designed and built with obvious flaws that left it susceptible to being exploited in the following ways: It downloads code to the user’s workstation without properly authenticating it, and in certain cases, it even does it through an unsecured HTTP connection rather than an HTTPS one. This would make it possible for a man-in-the-middle attack to be carried out by anybody who is able to intercept the user’s internet connection, such as a malicious Wi-Fi network. The attack would enable the installation source to be faked.
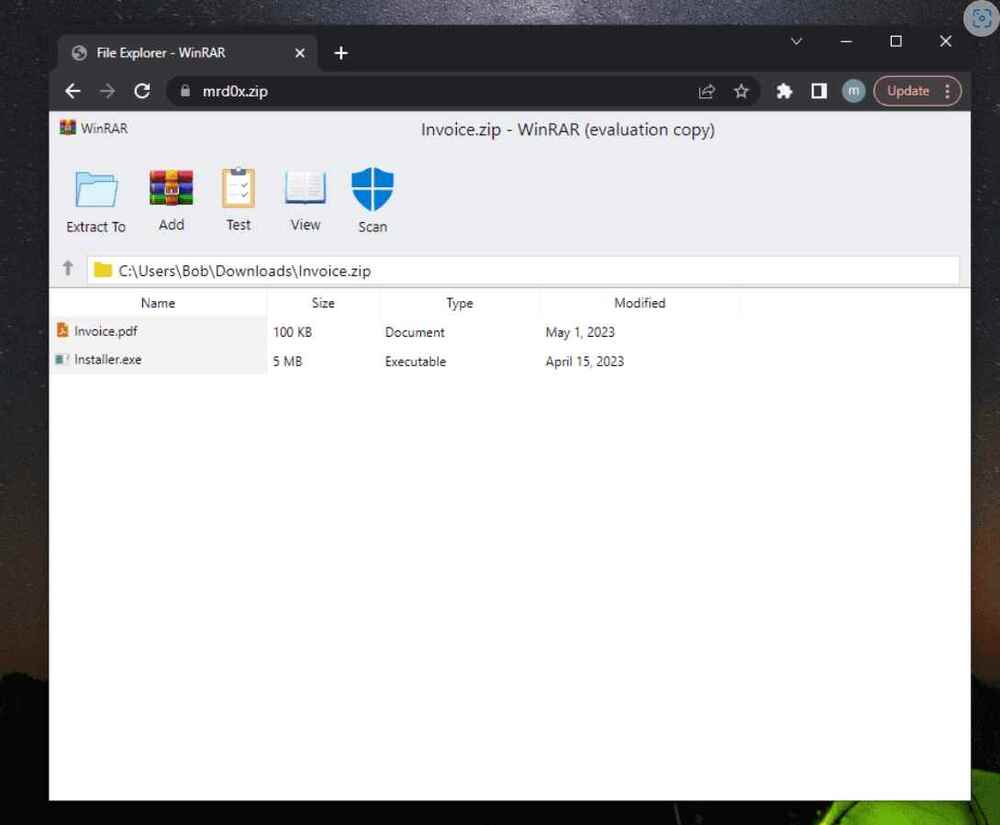
When a victim visits a website ending in. ZIP, a recently developed phishing method known as “file archiver in the browser” may be used to “emulate” file-archiving software in the target’s web browser.
According to information published by a security researcher named mr.d0x last week, “with this phishing attack, you simulate a file archiver software (e.g., WinRAR) in the browser and use a.zip domain to make it appear more legitimate,”
In a nutshell, threat actors could develop a realistic-looking phishing landing page using HTML and CSS that replicates genuine file archiving software. They could then host the website on a.zip domain, which would elevate social engineering tactics to a higher level.
Cybersecurity researchers are warning about CAPTCHA-breaking services that are being offered for sale to bypass systems designed to distinguish legitimate users from bot traffic.
“Because cybercriminals are keen on breaking CAPTCHAs accurately, several services that are primarily geared toward this market demand have been created,” Trend Micro said in a report published last week.
“These CAPTCHA-solving services don’t use [optical character recognition] techniques or advanced machine learning methods; instead, they break CAPTCHAs by farming out CAPTCHA-breaking tasks to actual human solvers.”

Cybersecurity researchers have found “backdoor-like behavior” within Gigabyte systems, which they say enables the UEFI firmware of the devices to drop a Windows executable and retrieve updates in an unsecure format.
Firmware security firm Eclypsium said it first detected the anomaly in April 2023. Gigabyte has since acknowledged and addressed the issue.
“Most Gigabyte firmware includes a Windows Native Binary executable embedded inside of the UEFI firmware,” John Loucaides, senior vice president of strategy at Eclypsium, told The Hacker News.


Russian cybercrime group TA505 has been observed using new hVNC (Hidden Virtual Network Computing) malware in recent attacks, threat intelligence company Elastic reports.
Called Lobshot, the malware allows attackers to bypass fraud detection engines and provides them with stealthy, direct access to the infected machines.
The threat actor distributes the malware through malvertising, abusing Google Ads and a network of fake websites to trick users into downloading legitimate-looking installers containing backdoors.

Join top executives in San Francisco on July 11–12, to hear how leaders are integrating and optimizing AI investments for success. Learn More
Why do people become ethical hackers? Given the negative connotations that the word “hacker” has unfortunately acquired over the past few decades, it’s tough to understand why anyone would ascribe themselves to that oxymoron.
Yet, ethical hackers are playing an increasingly vital role in cybersecurity, and the ranks of the ethical hacking community are growing significantly. If you’re thinking about working with or hiring ethical hackers — or even becoming one yourself — it’s important to understand what makes this unique breed of cyber-pro tick.
W elcome to the TechCrunch Exchange, a weekly startups-and-markets newsletter. It’s inspired by the daily TechCrunch+ column where it gets its name. Want it in your inbox every Saturday? Sign up here.
From cybersecurity to SaaS for restaurants, the key to running a successful business is selling a product that solves your clients’ real problems. — Anna
2022 in cybersecurity.