Secret Blizzard has a track record of targeting various sectors to facilitate long-term covert access for intelligence collection, but their primary focus is on ministries of foreign affairs, embassies, government offices, defense departments, and defense-related companies across the world.
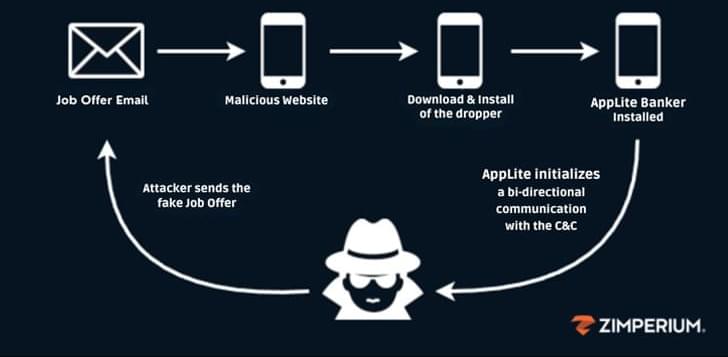
The latest report comes a week after the tech giant, along with Lumen Technologies Black Lotus Labs, revealed Turla’s hijacking of 33 command-and-control (C2) servers of a Pakistan-based hacking group named Storm-0156 to carry out its own operations.
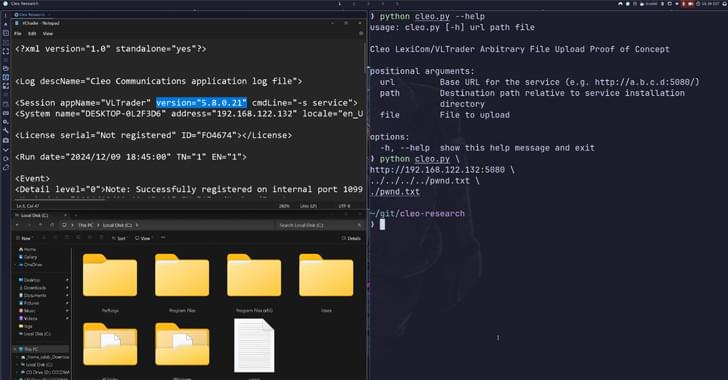
The attacks targeting Ukrainian entities entail commandeering Amadey bots to deploy a backdoor known as Tavdig, which is then used to install an updated version of Kazuar, which was documented by Palo Alto Networks Unit 42 in November 2023.