Today is Microsoft’s October 2025 Patch Tuesday, which includes security updates for 172 flaws, including six zero-day vulnerabilities. Get patching!


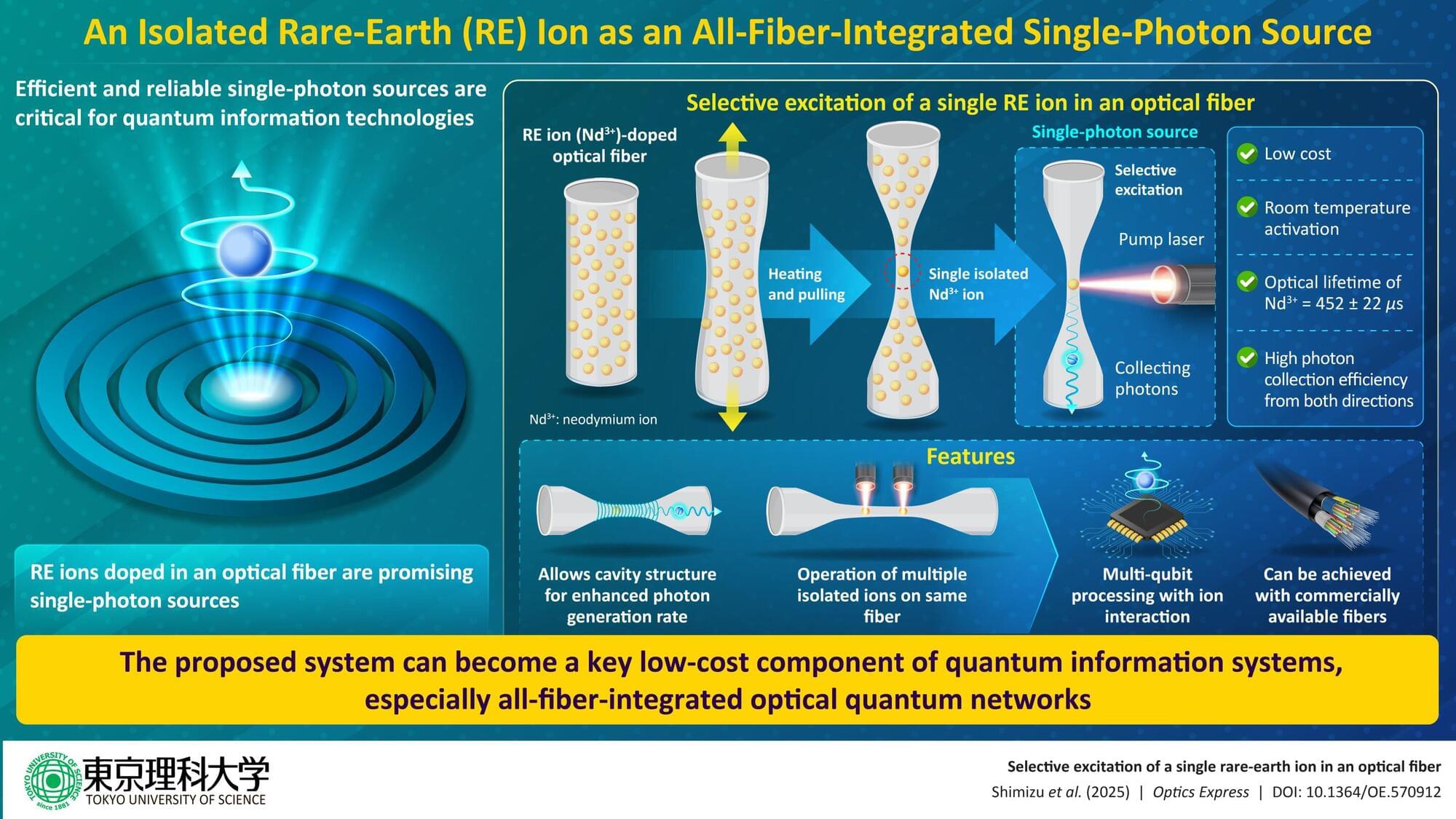
With the rise of quantum computers, the security of our existing communication systems is at risk. Quantum computers will be able to break many of the encryption methods used in current communication systems. To counter this, scientists are developing quantum communication systems, which utilize quantum mechanics to offer stronger security. A crucial building block of these systems is a single-photon source: a device that generates only one light particle at a time.
These photons, carrying quantum information, are then sent through optical fibers. For quantum communication systems to work, it is essential that single photons are injected into optical fibers with extremely low loss.
In conventional systems, single-photon emitters, like quantum dots and rare-earth (RE) element ions, are placed outside the fiber. These photons then must be guided to enter the fiber. However, not all photons make it into the fibers, causing high transmission loss. For practical quantum communication systems, it is necessary to achieve a high-coupling and channeling efficiency between the optical fiber and the emitter.

Around 200,000 Linux computer systems from American computer maker Framework were shipped with signed UEFI shell components that could be exploited to bypass Secure Boot protections.
An attacker could take advantage to load bootkits (e.g. BlackLotus, HybridPetya, and Bootkitty) that can evade OS-level security controls and persist across OS re-installs.
Powerful mm command.
A new side-channel attack called Pixnapping enables a malicious Android app with no permissions to extract sensitive data by stealing pixels displayed by applications or websites, and reconstructing them to derive the content.
The content may include sensitive private data like chat messages from secure communication apps like Signal, emails on Gmail, or two-factor authentication codes from Google Authenticator.
The attack, devised and demonstrated by a team of seven American university researchers, works on fully patched modern Android devices and can steal 2FA codes in less than 30 seconds.


A math theory powering computer image compression, an “invisibility cloak” or the science behind the James Webb Space Telescope are some achievements that could be honored when the Nobel physics prize is awarded Tuesday.
The award, to be announced at 11:45 am (0945 GMT) in Stockholm, is the second Nobel of the season, after the Medicine Prize was awarded on Monday to a US-Japanese trio for research into the human immune system.
Mary Brunkow and Fred Ramsdell, of the United States, and Japan’s Shimon Sakaguchi were recognized by the Nobel jury for identifying immunological “security guards”


As stated in Discord’s official statement addressing the breach, an “unauthorized party” compromised one of the platform’s third-party customer service providers, accessing information from a limited number of users who had contacted Discord’s Customer Support or Trust & Safety teams.
Due to this attack, the unnamed intruders obtained a number of government ID images, including driver’s licenses and passports, from some of the users who had appealed an age determination. In addition, the breach also resulted in the exposure of names, Discord usernames, emails, the last four digits of credit card numbers, purchase histories (if linked to the account), IP addresses, and messages with Discord’s customer service agents for some users.
The platform also clarified that more sensitive information, such as full credit card numbers or CVV codes, messages or activity on Discord outside of customer support interactions, and passwords or authentication data, was not impacted.