:oooo.
Underwater quantum links are possible across 30 meters (100 feet) of turbulent water, scientists have shown. Such findings could help to one day secure quantum communications for submarines.
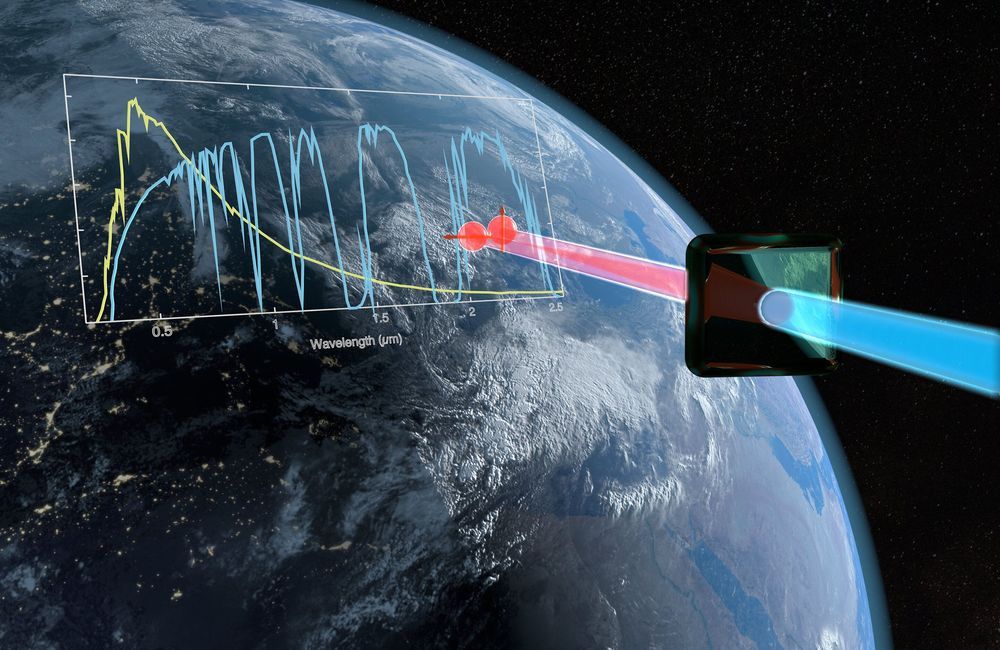
Quantum cryptography exploits the quantum properties of particles such as photons to help encrypt and decrypt messages in a theoretically unhackable way. Scientists worldwide are now endeavoring to develop satellite-based quantum communications networks for a global real-time quantum Internet.
In addition to beaming quantum communications signals across the air, through a vacuum, and within fiber optic cables, researchers have investigated establishing quantum communications links through water. Such work could lead to secure quantum communications between submarines and surface vessels, and with other subs, aircraft, or even satellites.