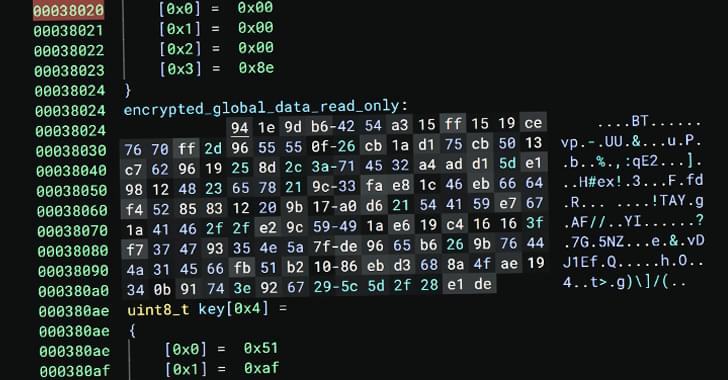
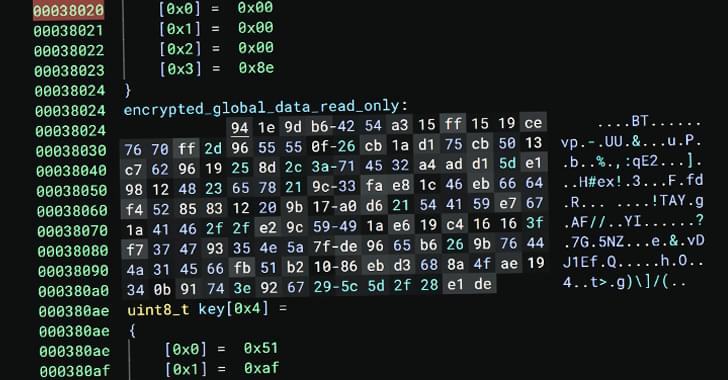
Auto-Color Linux malware targets governments and universities, using stealth tactics and encryption to evade detection and maintain persistence.

Scientists in Switzerland have developed a new method to improve internet security against quantum computing attacks, using quantum-resistant encryption and a new type of hardware.
Maybe it’s a life hack or a liability, or a little of both. A surprising result in a new MIT study may suggest that people and animals alike share an inherent propensity to keep updating their approach to a task even when they have already learned how they should approach it, and even if the deviations sometimes lead to unnecessary error.
The behavior of “exploring” when one could just be “exploiting” could make sense for at least two reasons, says Mriganka Sur, senior author of the study published Feb. 18 in Current Biology. Just because a task’s rules seem set one moment doesn’t mean they’ll stay that way in this uncertain world, so altering behavior from the optimal condition every so often could help reveal needed adjustments. Moreover, trying new things when you already know what you like is a way of finding out whether there might be something even better out there than the good thing you’ve got going on right now.
“If the goal is to maximize reward, you should never deviate once you have found the perfect solution, yet you keep exploring,” says Sur, the Paul and Lilah Newton Professor in The Picower Institute for Learning and Memory and the Department of Brain and Cognitive Sciences at MIT. “Why? It’s like food. We all like certain foods, but we still keep trying different foods because you never know, there might be something you could discover.”

An Android malware app called SpyLend has been downloaded over 100,000 times from Google Play, where it masqueraded as a financial tool but became a predatory loan app for those in India.
The app falls under a group of malicious Android applications called “SpyLoan,” which pretend to be legitimate financial tools or loan services but instead steal data from devices for use in predatory lending.
These apps lure users with promises of quick and easy loans, often requiring little documentation and offering attractive terms. However, upon installation, they request excessive permissions, allowing the apps to steal personal data such as contacts, call logs, SMS messages, photos, and device location.
Please see my latest Forbes article on the need to get ready for the Quantum Era. Thanks!
By Chuck Brooks, Forbes Contributor. Global Thought Leader in Cybersecurity and Emerging Tech.
“We are on the emerging pathway to the new era of quantum computing. We must now prepare for the exponential benefits and risks of quantum technologies.”
https://search.app/SbiN8RJWMdDx39ac8
#quantum #quantumcomputing #tech #cybersecurity #artificialintelligence

Not everyone is willing to passively accept the future AI companies are shaping.
In an aggressive response to AI companies like OpenAI, independent developers have created “tarpits” — malicious software designed to trap and confuse AI scrapers for months on end.
The goal? To make AI companies pay a higher price for their relentless data collection and, perhaps, to slow the rapid commercialization of AI-driven content generation.
Inspired by cybersecurity tactics originally used against spam, these digital snares lure AI crawlers into endless loops of fake data, slowing their operations and potentially corrupting their training models. One such tool, Nepenthes, forces scrapers into a maze of gibberish, while another, Iocaine, aims to poison AI models outright.
While critics argue that these efforts may have limited long-term impact—since AI companies are developing countermeasures—supporters see tarpits as a symbolic act of resistance against AI’s unchecked expansion.
With growing concerns over AI scraping depleting valuable online content and replacing human-created work with algorithm-generated material, these digital weapons offer a way for website owners to fight back.
