We look forward to collaborating closely with Proton International on these new centers and providing greater access to this lifesaving technology to patients in Texas and the Southeast.”
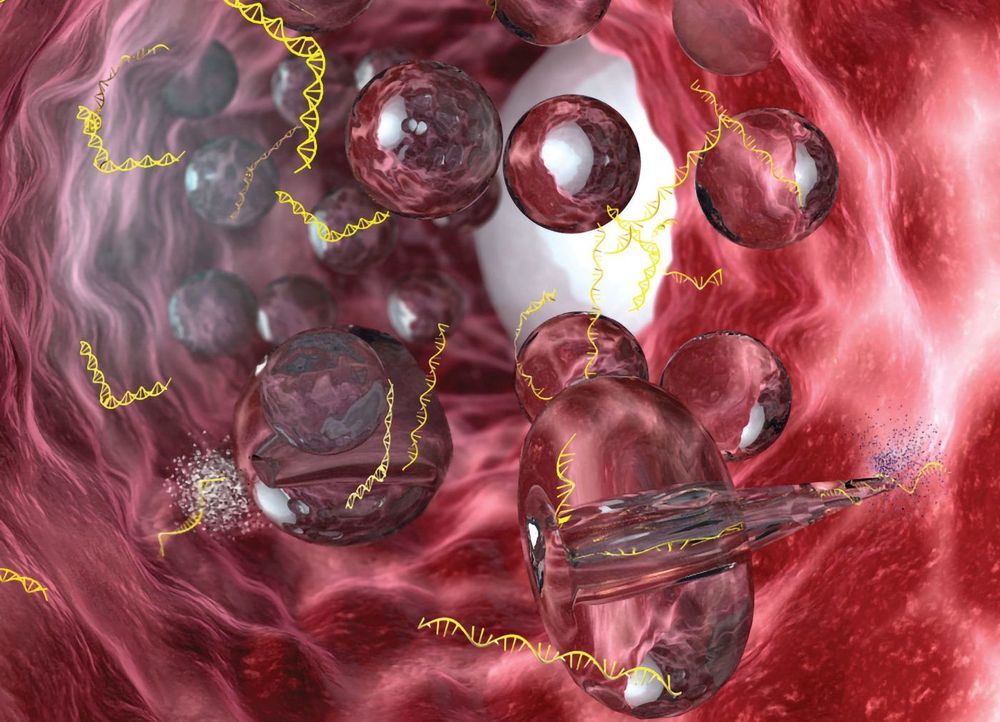
The new centers will feature the MEVION S250i Proton Therapy System® with HYPERSCAN® Pencil Beam Scanning (PBS). HYPERSCAN enables faster and sharper delivery of therapeutic radiation to tumors. The system’s leading-edge clinical capabilities, combined with its compact, affordable design, and industry-leading ramp-up time, has changed the landscape of proton therapy. Today, more cancer centers are considering providing compact proton therapy to their patients because of the technology Mevion has advanced.
One key difference between X-ray or photon radiation therapy and proton therapy is already known. It goes to the very core of why proton therapy is beneficial. It’s not that it kills cancer better; it’s that it damages normal cells less.
LITTLETON, Mass.—(BUSINESS WIRE)—Mevion Medical Systems and Proton International announced today that they have signed a two-system contract to bring Mevion’s compact proton therapy solution to new centers in locations to be announced in South Texas and the Southeast United States.
“PI specializes in providing custom single-room proton therapy solutions to our clinical providers, and this technology will be a powerful addition to their cancer treatment arsenal.”
The new centers will feature the MEVION S250i Proton Therapy System® with HYPERSCAN® Pencil Beam Scanning (PBS). HYPERSCAN enables faster and sharper delivery of therapeutic radiation to tumors. The system’s leading-edge clinical capabilities, combined with its compact, affordable design, and industry-leading ramp-up time, has changed the landscape of proton therapy. Today, more cancer centers are considering providing compact proton therapy to their patients because of the technology Mevion has advanced.