This giant 60-foot ‘Gundam’ robot has made its first test moves — look at the size of it! 😲 🤖.
Get the latest international news and world events from around the world.
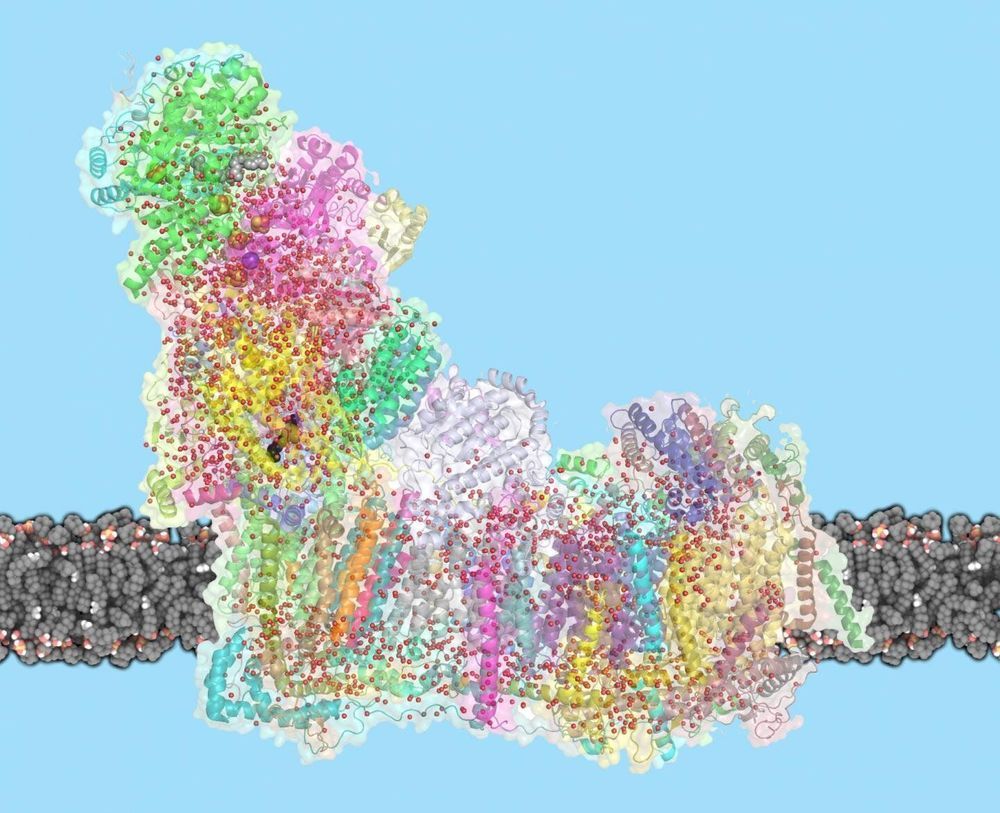
Mystery of giant proton pump solved
Mitochondria are the powerhouses of our cells, generating energy that supports life. A giant molecular proton pump, called complex I, is crucial: It sets in motion a chain of reactions, creating a proton gradient that powers the generation of ATP, the cell’s fuel. Despite complex I’s central role, the mechanism by which it transports protons across the membrane has so far been unknown. Now, Leonid Sazanov and his group at the Institute of Science and Technology Austria (IST Austria) have solved the mystery of how complex I works: Conformational changes in the protein combined with electrostatic waves move protons into the mitochondrial matrix. This is the result of a study published today in Science.
Complex I is the first enzyme in the respiratory chain, a series of protein complexes in the inner mitochondrial membrane. The respiratory chain is responsible for most of the cell’s energy production. In this chain, three membrane proteins set up a gradient of protons, moving them from the cell’s cytoplasm into the mitochondrial inner space, called the matrix. The energy for this process comes mostly from the electron transfer between NADH molecules, derived from the food we eat, and oxygen that we breathe. ATP synthase, the last protein in the chain, then uses this proton gradient to generate ATP.
Complex I is remarkable not only because of its central role in life, but also for its sheer size: with a molecular weight of 1 Megadalton, the eukaryotic complex I is one of the biggest membrane proteins. Its size also makes complex I hard to study. In 2016, Sazanov and his group were the first to solve the structure of mammalian complex I, following on their 2013 structure of a simpler bacterial enzyme. But the mechanism by which complex I moves protons across the membrane has remained controversial. “One idea was that a part of complex I works like a piston, to open and close channels through which protons travel”, explains Sazanov. “Another idea was that residues at the center of complex I act as a driver. It turns out that an even more unusual mechanism is at work.”
This is What Mars Colonies Could Be Like in 2035
As earth becomes less habitable due to the climate emergency, The Astroland Agency are working out how humans could colonize Mars by 2035. Before the pandemic, we spent time with them to learn how that would work.
About VICE:
The Definitive Guide To Enlightening Information. From every corner of the planet, our immersive, caustic, ground-breaking and often bizarre stories have changed the way people think about culture, crime, art, parties, fashion, protest, the internet and other subjects that don’t even have names yet. Browse the growing library and discover corners of the world you never knew existed. Welcome to VICE.
Connect with VICE:
Check out our full video catalog: http://bit.ly/VICE-Videos
Videos, daily editorial and more: http://vice.com
More videos from the VICE network: https://www.fb.com/vicevideo
Like VICE on Facebook: http://fb.com/vice
Follow VICE on Twitter: http://twitter.com/vice
Follow us on Instagram: http://instagram.com/vice
The VICE YouTube Network:
VICE: https://www.youtube.com/VICE
MUNCHIES: https://www.youtube.com/MUNCHIES
VICE News: https://www.youtube.com/VICENews
VICELAND: https://www.youtube.com/VICELANDTV
Broadly: https://www.youtube.com/Broadly
Noisey: https://www.youtube.com/Noisey
Motherboard: https://www.youtube.com/MotherboardTV
VICE Sports: https://www.youtube.com/NOC
i-D: https://www.youtube.com/iDmagazine
Waypoint: https://www.youtube.com/Waypoint
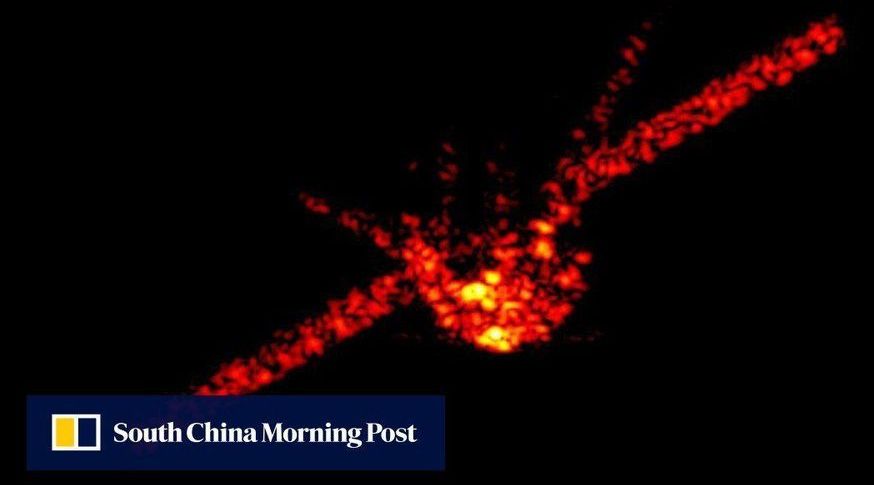

Scientists achieve higher precision weak force measurement between protons, neutrons
O,.o.
Through a one-of-a-kind experiment at the Department of Energy’s Oak Ridge National Laboratory, nuclear physicists have precisely measured the weak interaction between protons and neutrons. The result quantifies the weak force theory as predicted by the Standard Model of Particle Physics.
The team’s weak force observation, detailed in Physical Review Letters, was measured through a precision experiment called n3He, or n-helium-3, that ran at ORNL’s Spallation Neutron Source, or SNS. Their finding yielded the smallest uncertainty of any comparable weak force measurement in the nucleus of an atom to date, which establishes an important benchmark.
The Standard Model describes the basic building blocks of matter in the universe and fundamental forces acting between them. Calculating and measuring the weak force between protons and neutrons is an extremely difficult task.
Ripjar, founded by GCHQ alums, raises $36.8M for AI that detects financial crime
Financial crime as a wider category of cybercrime continues to be one of the most potent of online threats, covering nefarious activities as diverse as fraud, money laundering and funding terrorism. Today, one of the startups that has been building data intelligence solutions to help combat that is announcing a fundraise to continue fueling its growth.
Ripjar, a U.K. company founded by five data scientists who previously worked together in British intelligence at the Government Communications Headquarters (GCHQ, the U.K.’s equivalent of the NSA), has raised $36.8 million (£28 million) in a Series B, money that it plans to use to continue expanding the scope of its AI platform — which it calls Labyrinth — and scaling the business.
Labyrinth, as Ripjar describes it, works with both structured and unstructured data, using natural language processing and an API-based platform that lets organizations incorporate any data source they would like to analyse and monitor for activity. It automatically and in real time checks these against other data sources like sanctions lists, politically exposed persons (PEPs) lists and transaction alerts.

Mind-reading device uses AI to turn brainwaves into audible speech
People’s brainwaves have been converted into speech using electrodes on the brain. The method could one day help people speak who have lost the ability.
By Chelsea Whyte.
Electrodes on the brain have been used to translate brainwaves into words spoken by a computer – which could be useful in the future to help people who have lost the ability to speak.
When you speak, your brain sends signals from the motor cortex to the muscles in your jaw, lips and larynx to coordinate their movement and produce a sound.


China attacked Indian satellite communications: US Report
“Computer network attack against Indian satellite communications in 2017” is one among a slew of counter-space activities carried out by China since 2007, listed in a new report by US-based China Aerospace Studies Institute (CASI), which provides China’s space narrative among other things.
Isro, while conceding that cyber-attacks are a constant threat, maintains that its systems has not been compromised so far.
The 142-page report notes that between 2012 and 2018, China carried out multiple cyber-attacks, but elaborates on the result only in one case.