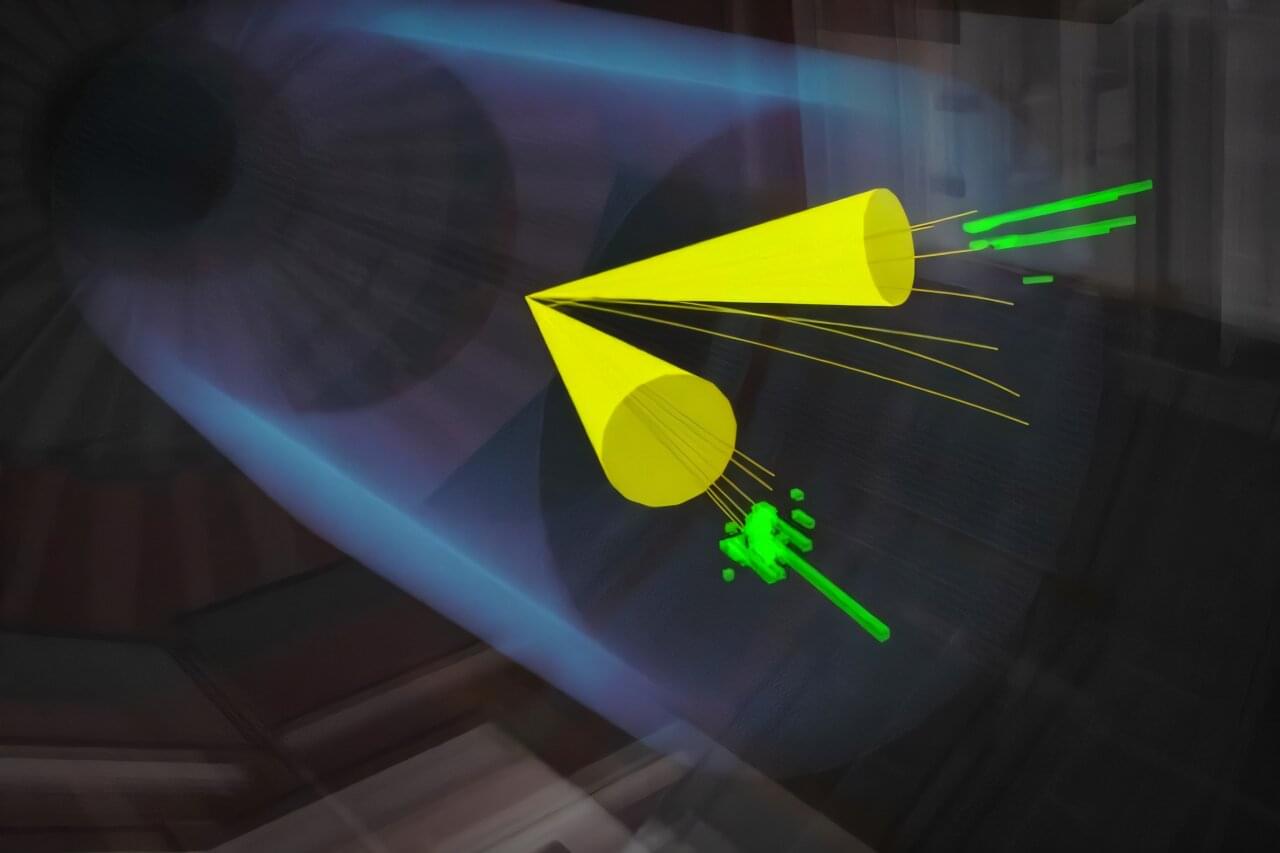
Studying and designing novel materials is a central application of quantum mechanics. Chemists, materials scientists, and physicists focus on subtle interactions in quantum materials and to uncover them they rely on sophisticated computational and experimental techniques. Computer simulations that connect microscopic quantum interactions to measurable material properties complement experimental data to connect structure to function—but classical computers can struggle to simulate those properties. Fortunately, scientists today have a new tool in their toolbox: quantum computers.
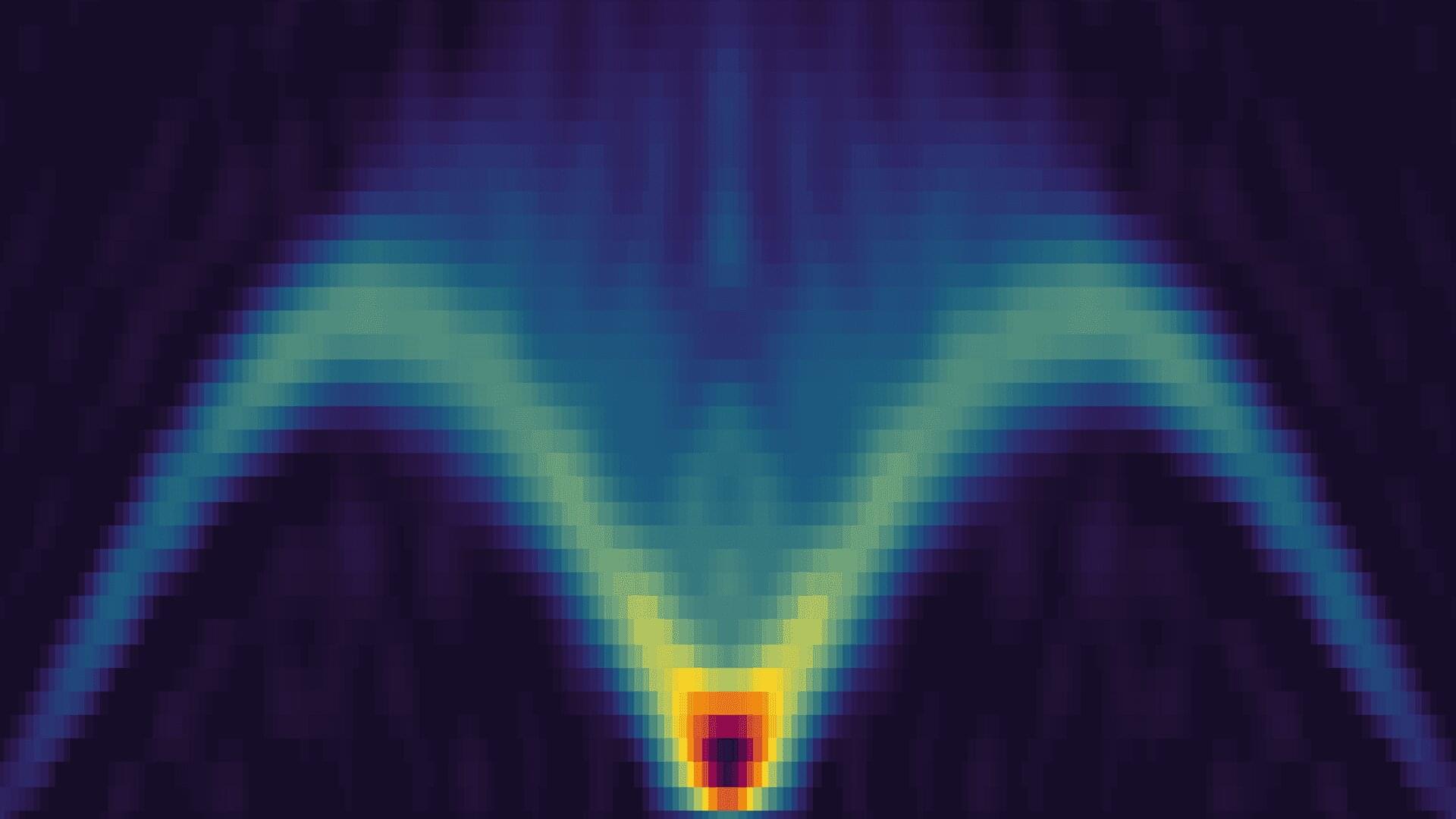
In new preprint, a team of researchers from Oak Ridge National Lab’s (ORNL’s) Quantum Science Center (QSC), Purdue University, Los Alamos Laboratory, the University of Illinois at Urbana-Champaign, the University of Tennessee, and IBM used quantum simulation to compute the energy-momentum spectrum of a well-studied magnetic material, KCuF3, showing strong agreement with the spectra measured via neutron scattering. The research is published on the arXiv preprint server.
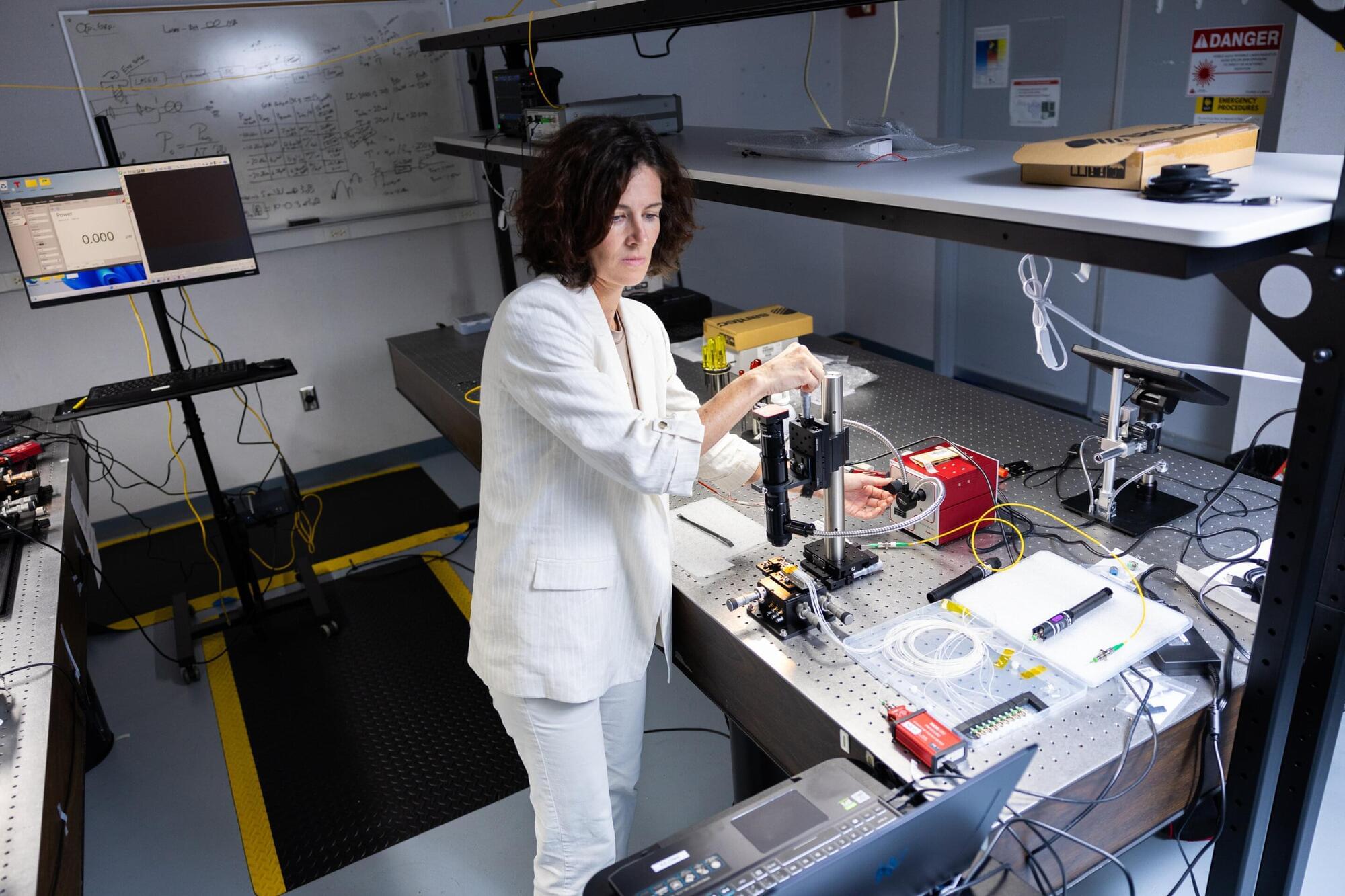
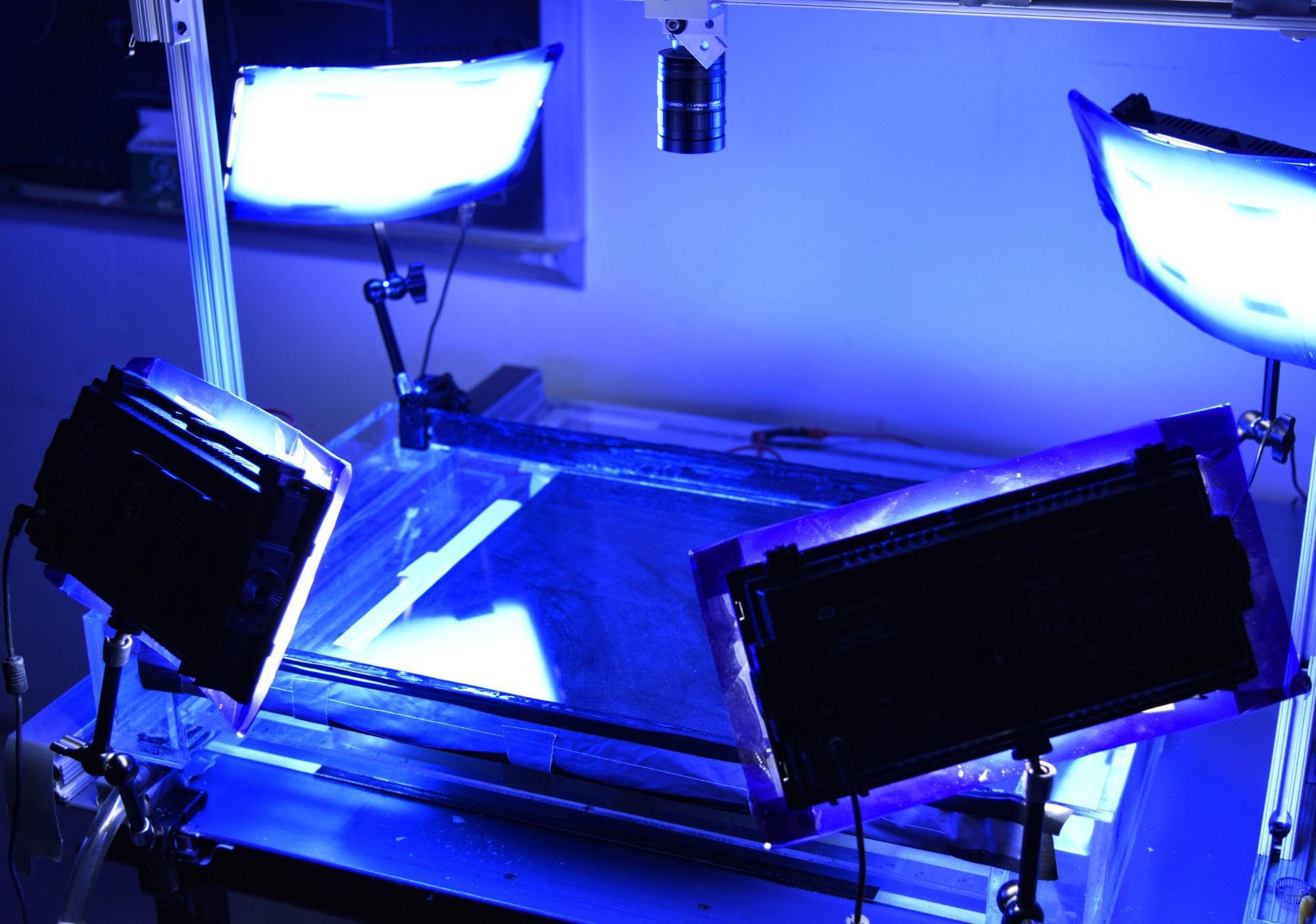
The quantum simulations employed the IBM Quantum Heron processor, while the experimental data was acquired from neutron sources at the Spallation Neutron Source (SNS) at ORNL and at the Rutherford Appleton Laboratory in the United Kingdom. This work serves as another realization of Richard Feynman’s vision: the use of a well-controlled, programmable quantum system to simulate the properties of a quantum system of interest.