Divice recipe for making spiking artificial neurons.
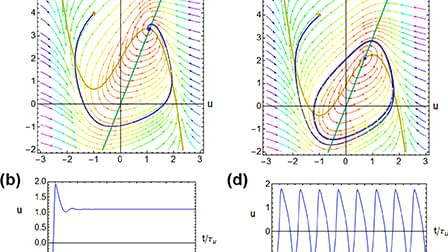
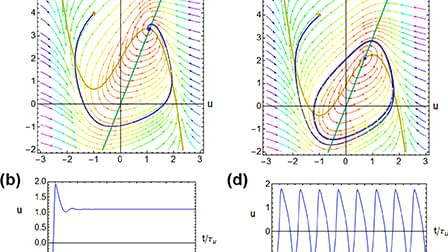
Neurons, which are made of biological tissue, exhibit cognitive properties that can be replicated in various material substrates. To create brain-inspired computational artificial systems, we can construct microscopic electronic neurons that mimic natural systems. In this paper, we discuss the essential material and device properties needed for a spiking neuron, which can be characterized using impedance spectroscopy and small perturbation equivalent circuit elements. We find that the minimal neuron system requires a capacitor, a chemical inductor, and a negative resistance. These components can be integrated naturally in the physical response of the device, instead of built from separate circuit elements. We identify the structural conditions for smooth oscillations that depend on certain dynamics of a conducting system with internal state variables. These state variables can be of diverse physical nature, such as properties of fluids, electronic solids, or ionic organic materials, implying that functional neurons can be built in various ways. We highlight the importance of detecting the Hopf bifurcation, a critical point in achieving spiking behavior, through spectral features of the impedance. To this end, we provide a systematic method of analysis in terms of the critical characteristic frequencies that can be obtained from impedance methods. Thus, we propose a methodology to quantify the physical and material properties of devices to produce the dynamic properties of neurons necessary for specific sensory-cognitive tasks. By replicating the essential properties of biological neurons in electronic systems, it may be possible to create brain-inspired computational systems with enhanced capabilities in information processing, pattern recognition, and learning. Additionally, understanding the physical and material properties of neurons can contribute to our knowledge of how biological neurons function and interact in complex neural networks. Overall, this paper presents a novel approach toward building brain-inspired artificial systems and provides insight into the important material and device considerations for achieving spiking behavior in electronic neurons.