A DIY hacker equipped with a Flipper Zero and old security camera managed to build a Mobile Infrared Trasmitter to bypass red lights.
Category: security – Page 90
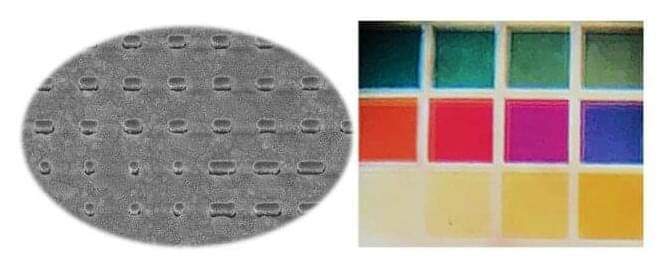
Chromo-encryption method uses color to encode information
In a new approach to security that unites technology and art, EPFL researchers have combined silver nanostructures with polarized light to yield a range of brilliant colors, which can be used to encode messages.
Cryptography is something of a new field for Olivier Martin, who has been studying the optics of nanostructures for many years as head of the Nanophotonics and Metrology Lab EPFL’s School of Engineering. But after developing some new silver nanostructures in collaboration with the Center of MicroNanoTechnology, Martin and Ph.D. student Hsiang-Chu Wang noticed that these nanostructures reacted to polarized light in an unexpected way, which just happened to be perfect for encoding information.
They found that when polarized light was shone through the nanostructures from certain directions, a range of vivid and easily-identifiable colors was reflected back. These different colors could be assigned numbers, which could then be used to represent letters using the electronic communication standard code ASCII (American Standard Code for Information Interchange). To encode a secret message, the researchers applied a quaternary code using the digits 0, 1, 2 and 3 (as opposed to the more commonly used binary code 0 and 1). The result was a series of four-digit strings composed of different color combinations that could be used to spell out a message, and the method of chromo-encryption was born.

Catastrophic Contagion, a high-level pandemic exercise in 2022
The Johns Hopkins Center for Health Security, in partnership with WHO and the Bill & Melinda Gates Foundation, conducted Catastrophic Contagion, a pandemic tabletop exercise at the Grand Challenges Annual Meeting in Brussels, Belgium, on October 23, 2022.
The extraordinary group of participants consisted of 10 current and former Health Ministers and senior public health officials from Senegal, Rwanda, Nigeria, Angola, Liberia, Singapore, India, Germany, as well as Bill Gates, co-chair of the Bill & Melinda Gates Foundation.
The exercise simulated a series of WHO emergency health advisory board meetings addressing a fictional pandemic set in the near future. Participants grappled with how to respond to an epidemic located in one part of the world that then spread rapidly, becoming a pandemic with a higher fatality rate than COVID-19 and disproportionately affecting children and young people.

Tile Adds Undetectable Anti-Theft Mode to Tracking Devices, With $1 Million Fine If Used for Stalking
AirTag competitor Tile today announced a new Anti-Theft Mode for Tile tracking devices, which is designed to make Tile accessories undetectable by the anti-stalking Scan and Secure feature.
Scan and Secure is a security measure that Tile implemented in order to allow iPhone and Android users to scan for and detect nearby Tile devices to keep them from being used for stalking purposes. Unfortunately, Scan and Secure undermines the anti-theft capabilities of the Tile because a stolen device’s Tile can be located and removed, something also possible with similar security features added for AirTags.
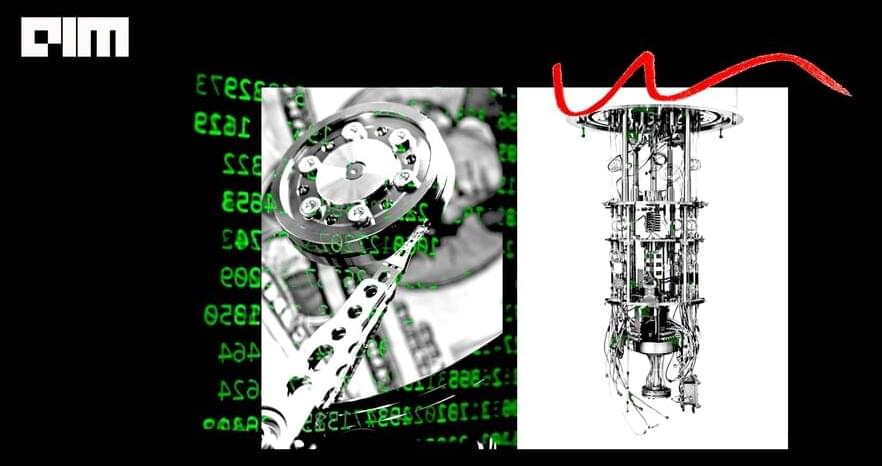
6 Quantum Algorithms That Will Change Computing Forever
Here is a list of some of the most popular quantum algorithms highlighting the significant impact quantum can have on the classical world:
Shor’s Algorithm
Our entire data security systems are based on the assumption that factoring integers with a thousand or more digits is practically impossible. That was until Peter Shor in 1995 proposed that quantum mechanics allows factorisation to be performed in polynomial time, rather than exponential time achieved using classical algorithms.

Dynatrace strengthens observability intelligence with AutomationEngine, Grail updates
Check out all the on-demand sessions from the Intelligent Security Summit here.
Massachusetts-headquartered Dynatrace, which provides an intelligence layer to monitor and optimize application development, performance and security, today announced key updates for its core platform, including a new AutomationEngine that enables teams to streamline monitoring and other activity across a variety of workflows.
Developers, security specialists, operations personnel and even business users can tap into the platform. The company made the announcement at its annual cloud observability conference in Las Vegas.

Hackers start using Havoc post-exploitation framework in attacks
Security researchers are seeing threat actors switching to a new and open-source command and control (C2) framework known as Havoc as an alternative to paid options such as Cobalt Strike and Brute Ratel.
Among its most interesting capabilities, Havoc is cross-platform and it bypasses Microsoft Defender on up-to-date Windows 11 devices using sleep obfuscation, return address stack spoofing, and indirect syscalls.
Like other exploitation kits, Havoc includes a wide variety of modules allowing pen testers (and hackers) to perform various tasks on exploited devices, including executing commands, managing processes, downloading additional payloads, manipulating Windows tokens, and executing shellcode.

Jasper targets enterprise to expand generative AI beyond generic AI
Check out all the on-demand sessions from the Intelligent Security Summit here.
Generative AI has been all the rage in the recent months, but it is typically generic and not specifically focused on the specific needs of any one company.
San Francisco based startup Jasper is aiming to help make generative AI less generic. The company made a series of announcements today at its Gen AI conference.
CISOs: Self-healing endpoints key to consolidating tech stacks, improving cyber-resiliency
Check out all the on-demand sessions from the Intelligent Security Summit here.
Self-healing endpoint platform providers are under pressure to create new solutions to help CISOs consolidate tech stacks while improving cyber-resiliency. CISOs see the potential of self-healing platforms to reduce costs, increase visibility and capture real-time data that quantifies how cyber-resilient they are becoming. And reducing costs while increasing cyber-resilience is the risk profile their boards of directors want.
A self-healing endpoint is one that combines self-diagnostics with the adaptive intelligence to identify a suspected or actual breach attempt and take immediate action to stop it. Self-healing endpoints can shut themselves off, complete a re-check of all OS and application versioning, and then reset themselves to an optimized, secure configuration — all autonomously with no human intervention.