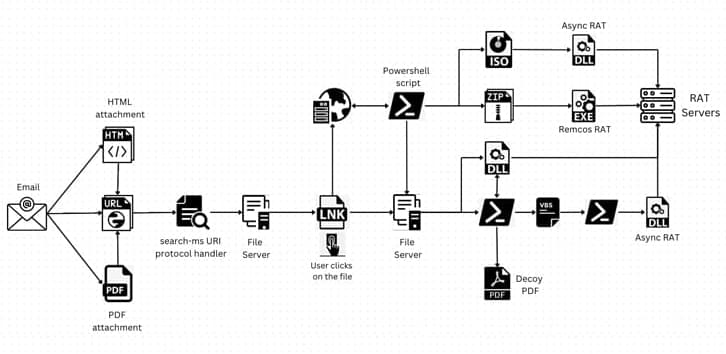
A legitimate Windows search feature is being exploited by unknown malicious actors to download arbitrary payloads from remote servers and compromise targeted systems with remote access trojans such as AsyncRAT and Remcos RAT.
The novel attack technique, per Trellix, takes advantage of the “search-ms:” URI protocol handler, which offers the ability for applications and HTML links to launch custom local searches on a device, and the “search:” application protocol, a mechanism for calling the desktop search application on Windows.
“Attackers are directing users to websites that exploit the ‘search-ms’ functionality using JavaScript hosted on the page,” security researchers Mathanraj Thangaraju and Sijo Jacob said in a Thursday write-up. “This technique has even been extended to HTML attachments, expanding the attack surface.”