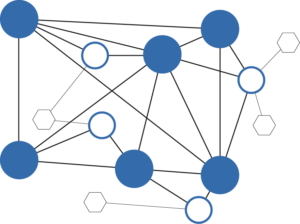
At the heart of Bitcoin or any Blockchain ledger is a distributed consensus mechanism. It’s a lot like voting. A large and diverse deliberative community validates each, individual user transaction, ownership stake or vote.
But a distributed consensus mechanism is only effective and faithful if the community is impartial. To be impartial, voters must be fairly separated. That is, there must be no collusion enabled by concentration or hidden collaboration. They must be separated from the buyer and seller; they must be separated from the big stakeholders; and they must be separated from each other. Without believable and measurable separation, all sorts of problems ensue. One problem that has made news in the Bitcoin word is the geographical concentration of miners and mining pools.
A distributed or decentralized transaction validation is typically achieved based on Proof-of-Work (POW) or Proof-of-Stake (POS). [explain]. But in practice, these methodologies exhibit subtle problems…
The problem is that Proof-of-Work can waste an enormous amount of energy and both techniques result in a concentration of power (either by geography or by special interest) — rather than a fair, distributed consensus.
In a quasi-formal paper, C.V. Alkan describes a fresh approach to Blockchain consensus. that he calls Distributed Objective Consensus. As you try to absorb his mechanism, you encounter concepts of Sybil attacks, minting inequality, the “nothing-at-stake” 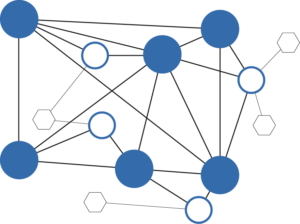 problem, punishment schemes and heartbeat transactions. Could Alkan’s distributed consensus mechanism be too complex for the public to understand or use?…
problem, punishment schemes and heartbeat transactions. Could Alkan’s distributed consensus mechanism be too complex for the public to understand or use?…
While I have a concern that time stamps and parent-child schemes may degrade user anonymity, the complexity doesn’t concern me. Alkan’s paper is a technical proposal for magic under the covers. Properly implemented, a buyer and seller (and even a miner) needn’t fully understand the science. The user interface to their wallet or financial statement would certainly be shielded from the underlying mechanics.
Put another way: You would not expect a user to understand the mechanism any more than an airline passenger understands the combustion process inside a jet engine. They only want to know:
• Does it work? • Is it safe? • Is it cost effective? • Will I get there on time?
So will Alkan’s Decentralized Objective Consensus solve the resource and concentration problems that creep into POW and POS? Perhaps. At first glance, his technical presentation appears promising. I will return to explore the impact on privacy and anonymity, which is my personal hot button. It is a critical component for long term success of any coin transaction system built on distributed consensus. That is, forensic access and analysis of a wallet or transaction audit trail must be impossible without the consent and participation of at least one party to a transaction.
Philip Raymond co-chairs CRYPSA and The Bitcoin Event. He is a Lifeboat board member, editor
at AWildDuck and will deliver the keynote address at Digital Currency Summit in Johannesburg.








 problem, punishment schemes and heartbeat transactions. Could Alkan’s distributed consensus mechanism be too complex for the public to understand or use?…
problem, punishment schemes and heartbeat transactions. Could Alkan’s distributed consensus mechanism be too complex for the public to understand or use?…