Starlink has landed what is likely its biggest partnership yet as it signed recently to provide a prominent company with internet service.


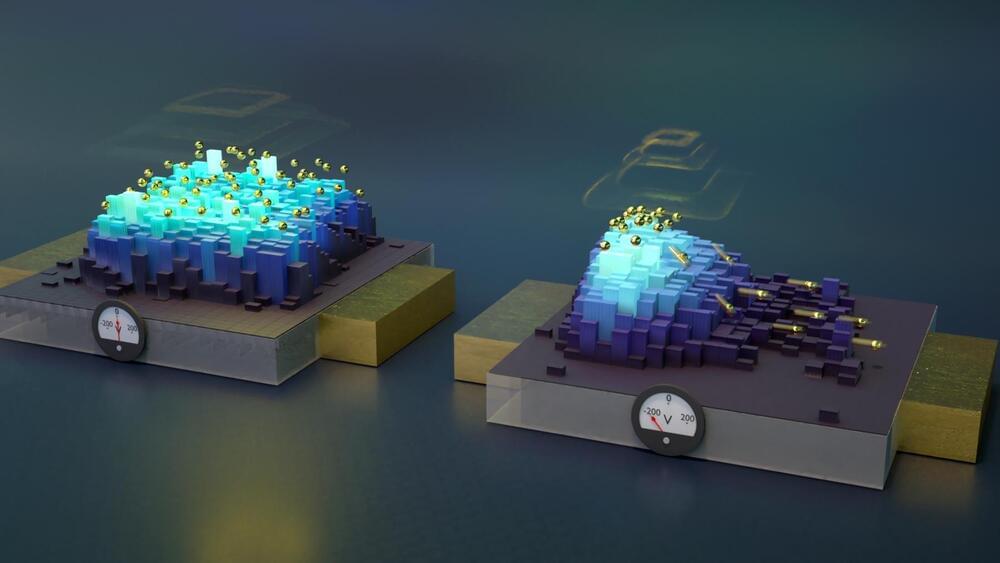
Building the quantum internet could be significantly simplified by leveraging existing telecommunications technologies and infrastructure. In recent years, researchers have identified defects in silicon—a widely used semiconductor material—that hold the potential for transmitting and storing quantum information across the prevalent telecommunications wavelengths. These silicon defects might just be the prime contenders to host qubits for efficient quantum communications.
Exploring Quantum Defects in Silicon
“It’s still a Wild West out there,” said Evelyn Hu, the Tarr-Coyne Professor of Applied Physics and of Electrical Engineering at the Harvard John A. Paulson School of Engineering and Applied Sciences (SEAS). “Even though new candidate defects are a promising quantum memory platform, there is often almost nothing known about why certain recipes are used to create them, and how you can rapidly characterize them and their interactions, even in ensembles. And ultimately, how can we fine-tune their behavior so they exhibit identical characteristics? If we are ever to make a technology out of this wide world of possibilities, we must have ways to characterize them better, faster, and more efficiently.”
AI can turn wi-fi routers into cameras that can see in the dark and track living beings.
This video shows how AI turns WiFi routers into ‘cameras’ that can see people through walls.
With the help of AI, the researchers were able to detect the movement of human bodies in a room using Wi-Fi routers — even through walls.
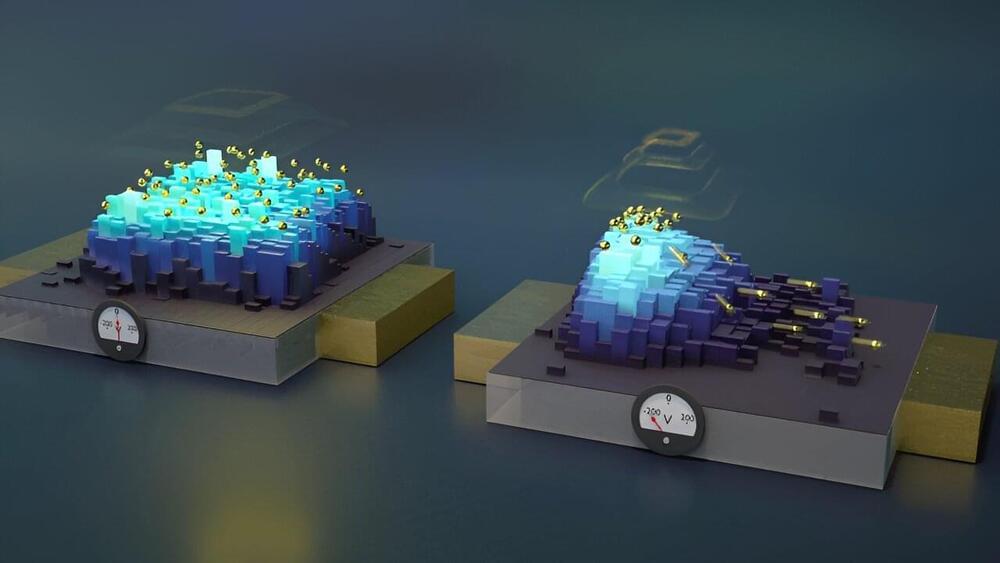
The quantum internet would be a lot easier to build if we could use existing telecommunications technologies and infrastructure. Over the past few years, researchers have discovered defects in silicon—a ubiquitous semiconductor material—that could be used to send and store quantum information over widely used telecommunications wavelengths. Could these defects in silicon be the best choice among all the promising candidates to host qubits for quantum communications?
Researchers have devised a new method of building quantum computers, creating and “annihilating” qubits on demand, using a femtosecond laser to dope silicon with hydrogen.
This breakthrough could pave the way for quantum computers that use programmable optical qubits or “spin-photon qubits” to connect quantum nodes across a remote network.
In turn, this creates a quantum internet that is more secure and capable of transmitting more data than current optical-fiber information technologies.

Internet data scraping is one of the biggest fights in AI right now. Tech companies argue that anything on the public internet is fair game, but they are facing a barrage of lawsuits over their data practices and copyright. It will likely take years until clear rules are in place.
In the meantime, they are running out of training data to build even bigger, more powerful models, and to Meta, your posts are a gold mine.
If you’re uncomfortable with having Meta use your personal information and intellectual property to train its AI models in perpetuity, consider opting out. Although Meta does not guarantee it will allow this, it does say it will “review objection requests in accordance with relevant data protection laws.”
Elon Musk says Tesla could make 100 million Optimus robots a year, costing $10k-20k each, to do everything from babysitting to working in factories, leading to the population of humanoid robots exceeding that of humans.
https://youtube.com/global5gevolution click #subscribe.
#tesla #elonmusk #…
Non-personalized content and ads are influenced by things like the content you’re currently viewing and your location (ad serving is based on general location). Personalized content and ads can also include things like video recommendations, a customized YouTube homepage, and tailored ads based on past activity, like the videos you watch and the things you search for on YouTube. We also use cookies and data to tailor the experience to be age-appropriate, if relevant.
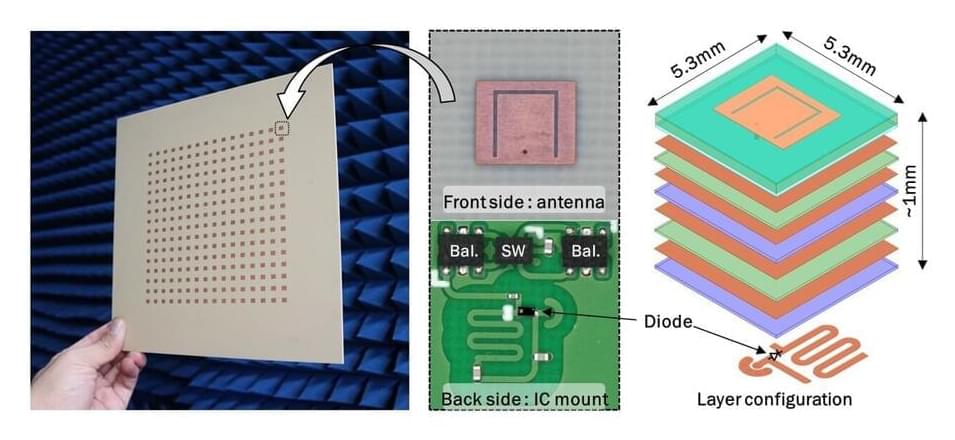
Researchers from the Photonics Research Laboratory (PRL)-iTEAM at the Universitat Politècnica de València, in collaboration with iPRONICS, have developed a groundbreaking photonic chip. This chip is the world’s first to be universal, programmable, and multifunctional, making it a significant advancement for the telecommunications industry, data centers, and AI computing infrastructures. It is poised to enhance a variety of applications including 5G communications, quantum computing, data centers, artificial intelligence, satellites, drones, and autonomous vehicles.
The development of this revolutionary chip is the main result of the European project UMWP-Chip, led by researcher José Capmany and funded by an ERC Advanced Grant from the European Research Council. The work has been published in the Nature Communications journal.