This article was written by Michael Gillings, Darrell Kemp, and Martin Hilbert from the University of California, Davis, and was originally published by The Conversation.
Living things accumulate and reproduce information. That’s really the driving principle behind life, and behind evolution. But humans have invented a new method of accumulating and reproducing information. It’s digital information, and it’s growing at an astonishing speed. The number of people using the internet is growing, as are the devices connected to it through the Internet of Things.
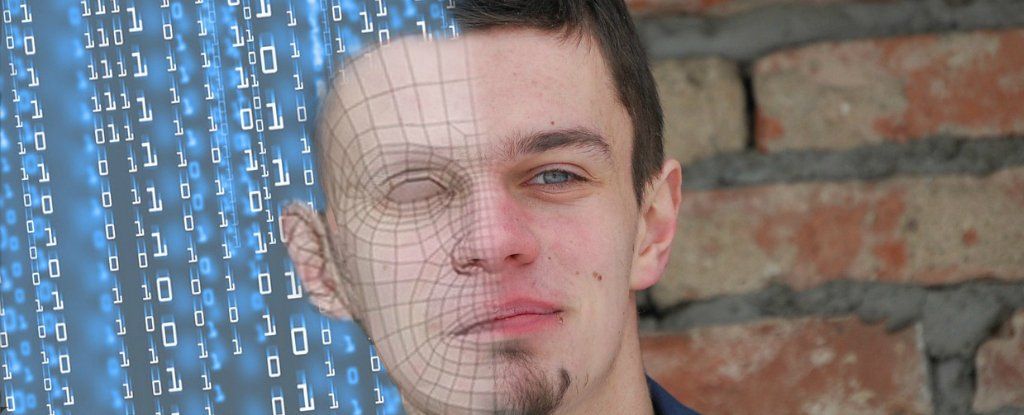
Digital information can copy itself perfectly, increases in copy number with every download or view, can be modified (mutated), or combined to generate novel information packets. And it can be expressed through artificial intelligence. These are characteristics similar to living things. So we should probably start thinking about digital technology as being like an organism that can evolve.