Circa 2013
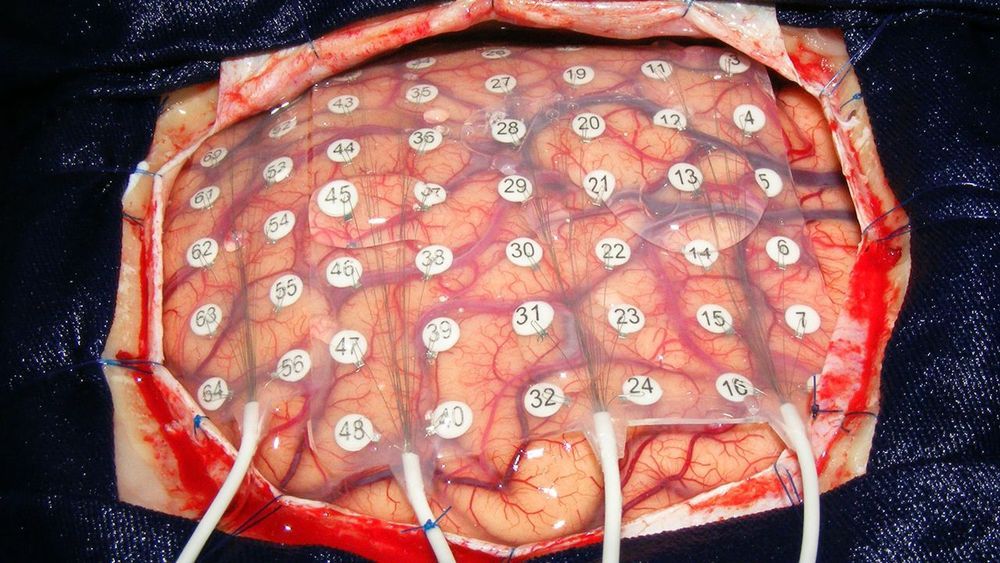
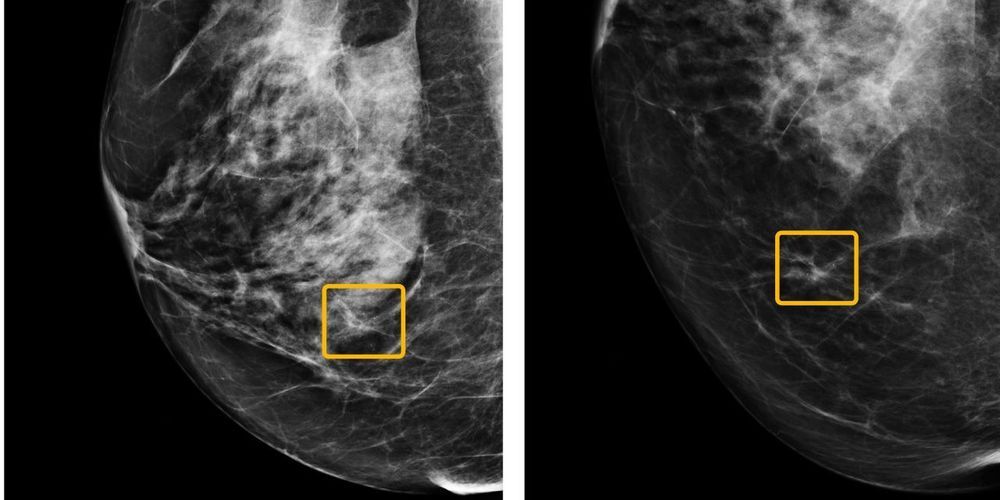
The unique relationship between the coordinates in the bore of a Magnetic Resonance Imaging (MRI) scanner and the magnetic field gradients used for MRI allows building a localization system based on the measurement of these gradients. We have previously presented a miniature 3D Hall probe integrated in a low cost, low voltage 0.35μm CMOS chip from which we were able to measure the magnetic gradient 3D maps of 1.5T and 3T MRI scanners. In this paper, this 3D Hall probe has been integrated in a magnetic tracking device prototype and an algorithm was built to determine the position of the probe. First experimental results show that the probe gives its position with accuracy close to a few millimeters, and that sub-millimeter localization in a one-shot-3ms-measurement should be readily possible. Such a prototype opens the way for the development of MRI compatible real time magnetic tracking systems which could be integrable in surgical tools for MR-guided minimally-invasive surgery.