Hackers are targeting U.S. hospitals just as COVID-19 cases surge again.






“I am used to being harassed online. But this was different,” she added. “It was as if someone had entered my home, my bedroom, my bathroom. I felt so unsafe and traumatized.”
Oueiss is one of several high-profile female journalists and activists who have allegedly been targeted and harassed by authoritarian regimes in the Middle East through hack-and-leak attacks using the Pegasus spyware, created by Israeli surveillance technology company NSO Group. The spyware transforms a phone into a surveillance device, activating microphones and cameras and exporting files without a user knowing.
A trio of researchers at Cornell University has found that it is possible to hide malware code inside of AI neural networks. Zhi Wang, Chaoge Liu and Xiang Cui have posted a paper describing their experiments with injecting code into neural networks on the arXiv preprint server.
As computer technology grows ever more complex, so do attempts by criminals to break into machines running new technology for their own purposes, such as destroying data or encrypting it and demanding payment from users for its return. In this new study, the team has found a new way to infect certain kinds of computer systems running artificial intelligence applications.
AI systems do their work by processing data in ways similar to the human brain. But such networks, the research trio found, are vulnerable to infiltration by foreign code.

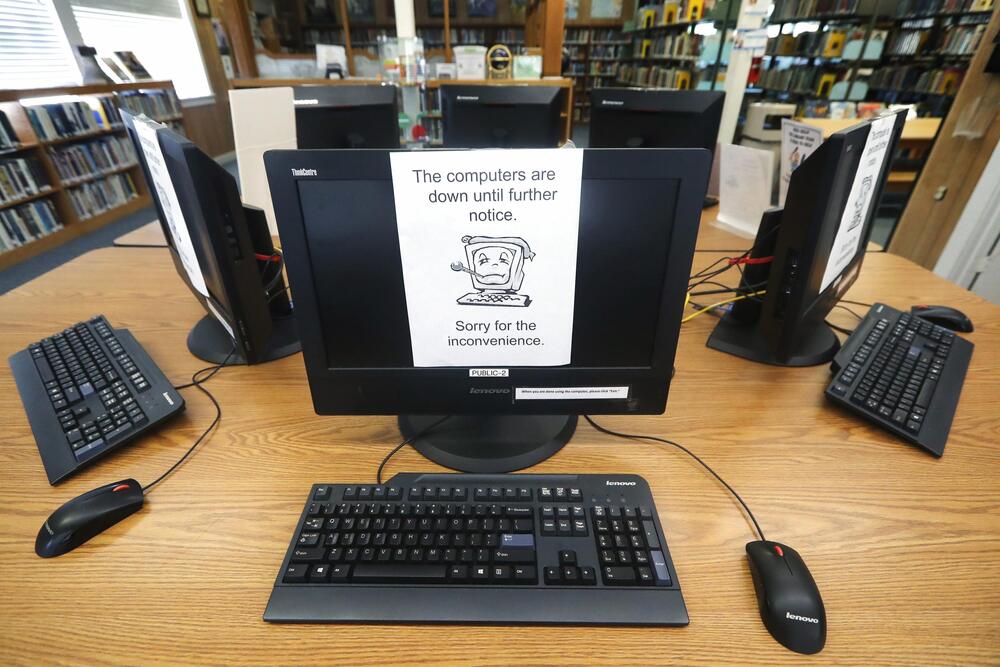
DALLAS (AP) — It was the start of a steamy Friday two Augusts ago when Jason Whisler settled in for a working breakfast at the Coffee Ranch restaurant in the Texas Panhandle city of Borger. The most pressing agenda item for city officials that morning: planning for a country music concert and anniversary event.
Then Whisler’s phone rang. Borger’s computer system had been hacked.
Workers were frozen out of files. Printers spewed out demands for money. Over the next several days, residents couldn’t pay water bills, the government couldn’t process payroll, police officers couldn’t retrieve certain records. Across Texas, similar scenes played out in nearly two dozen communities hit by a cyberattack officials ultimately tied to a Russia-based criminal syndicate.