Eighteen countries have signed an agreement on AI safety, based on the principle that it should be secure by design.
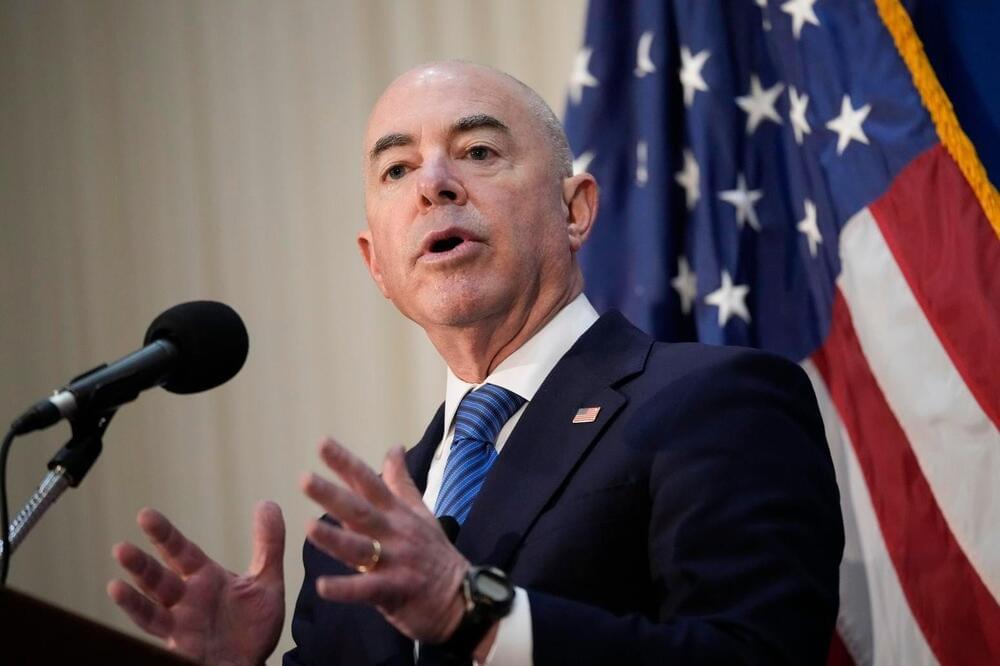
The Guidelines for Secure AI System Development, led by the U.K.’s National Cyber Security Centre and developed with the U.S.’ Cybersecurity and Infrastructure Security Agency, are touted as the first global agreement of their kind.
They’re aimed mainly at providers of AI systems that are using models hosted by an organization, or that are using external application programming interfaces. The aim is to help developers make sure that cybersecurity is baked in as an essential pre-condition of AI system safety and integral to the development process, from the start and throughout.