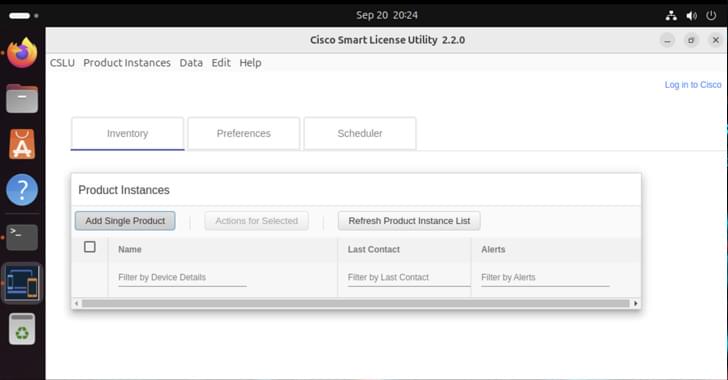
Active exploitation of Cisco CVE-2024–20439 & 20440 in Smart Licensing forces urgent patching of vulnerable versions.


Veeam has patched a critical remote code execution vulnerability tracked as CVE-2025–23120 in its Backup & Replication software that impacts domain-joined installations.
The flaw was disclosed yesterday and affects Veeam Backup & Replication version 12.3.0.310 and all earlier version 12 builds. The company fixed it in version 12.3.1 (build 12.3.1.1139), which was released yesterday.
According to a technical writeup by watchTowr Labs, who discovered the bug, CVE-2025–23120 is a deserialization vulnerability in the Veeam. Backup. EsxManager.xmlFrameworkDs and Veeam.Backup.Core. BackupSummary. NET classes.

Two malicious VSCode Marketplace extensions were found deploying in-development ransomware, exposing critical gaps in Microsoft’s review process.
The extensions, named “ahban.shiba” and “ahban.cychelloworld,” were downloaded seven and eight times, respectively, before they were eventually removed from the store.
It is notable that the extensions were uploaded onto the VSCode Marketplace on October 27, 2024 (ahban.cychelloworld) and February 17, 2025 (ahban.shiba), bypassing safety review processes and remaining on Microsoft’s store for an extensive period of time.

This research note deploys data from a simulation experiment to illustrate the very real effects of monolithic views of technology potential on decision-making within the Homeland Security and Emergency Management field. Specifically, a population of national security decision-makers from across the United States participated in an experimental study that sought to examine their response to encounter different kinds of AI agency in a crisis situation. The results illustrate wariness of overstep and unwillingness to be assertive when AI tools are observed shaping key situational developments, something not apparent when AI is either absent or used as a limited aide to human analysis. These effects are mediated by levels of respondent training. Of great concern, however, these restraining effects disappear and the impact of education on driving professionals towards prudent outcomes is minimized for those individuals that profess to see AI as a full viable replacement of their professional practice. These findings constitute proof of a “Great Machine” problem within professional HSEM practice. Willingness to accept grand, singular assumptions about emerging technologies into operational decision-making clearly encourages ignorance of technological nuance. The result is a serious challenge for HSEM practice that requires more sophisticated solutions than simply raising awareness of AI.
Keywords: artificial intelligence; cybersecurity; experiments; decision-making.

The rapid evolution of artificial intelligence (AI) is poised to create societal transformations. Indeed, AI is already emerging as a factor in geopolitics, with malicious non-state actors exploiting its capabilities to spread misinformation and potentially develop autonomous weapons. To be sure, not all countries are equal in AI, and bridging the “AI divide” between the Global North and South is vital to ensuring equal representation while addressing regulatory concerns and the equitable distribution of benefits that can be derived from the technology.
Most G20 members have established comprehensive national AI strategies, notably technology giants like the United States, United Kingdom, China, and countries of the European Union. Global South nations such as Brazil, Argentina, and India, despite economic constraints, are demonstrating progress in leveraging AI in areas like social services and agriculture. Future strategies must anticipate emerging threats like Generative AI (GenAI) and Quantum AI, prioritising responsible governance to mitigate biases, inequalities, and cybersecurity risks.
This document intends to provide a summary of the cybersecurity threats in Japan with reference to globally observed cyber landscape. It looks at various kinds of cyberattacks their quantum and impact as well as specific verticals that are targeted by various threat actors.
As in February, 2024, in Japan, an organisation faces an average of 1,003 attacks per week, with FakeUpdates being the top malware. Most malicious files are delivered via email, and Remote Code Execution is the most common vulnerability exploit. In recent times, major Japanese incidents include a sophisticated malware by a nation state, attacks on Nissan and JAXA, and data breaches at the University of Tokyo and CASIO. Globally, incidents include Ukrainian media hacks, a ransomware attack on U.S. schools, and disruptions in U.S. healthcare due to cyber-attacks. The document also covers trends in malware types, attack vectors, and impacted industries over the last 6 months.
The details provide an overview of the threat landscape and major incidents in Japan and globally, highlighting the prevalence of attacks, common malware types, and impact on various industries and organisations. The information described should create awareness and help businesses and government organisation prepare well to safely operate in a digital environment.

IINA provides ongoing analysis of international affairs both by region—such as North America, China, and Europe—and by such topics as human security, nontraditional security threats, and cyber security. The articles on this site, written by experts at the Sasakawa Peace Foundation and guest contributors, are carefully selected for their objectivity, accuracy, timeliness, and relevance for Japan.

IINA provides ongoing analysis of international affairs both by region—such as North America, China, and Europe—and by such topics as human security, nontraditional security threats, and cyber security. The articles on this site, written by experts at the Sasakawa Peace Foundation and guest contributors, are carefully selected for their objectivity, accuracy, timeliness, and relevance for Japan.
IINA provides ongoing analysis of international affairs both by region—such as North America, China, and Europe—and by such topics as human security, nontraditional security threats, and cyber security. The articles on this site, written by experts at the Sasakawa Peace Foundation and guest contributors, are carefully selected for their objectivity, accuracy, timeliness, and relevance for Japan.