Malware campaign using Facebook ads and fake crypto apps delivers JSCEAL, targeting credentials and wallets.


Threat hunters have disclosed two different malware campaigns that have targeted vulnerabilities and misconfigurations across cloud environments to deliver cryptocurrency miners.
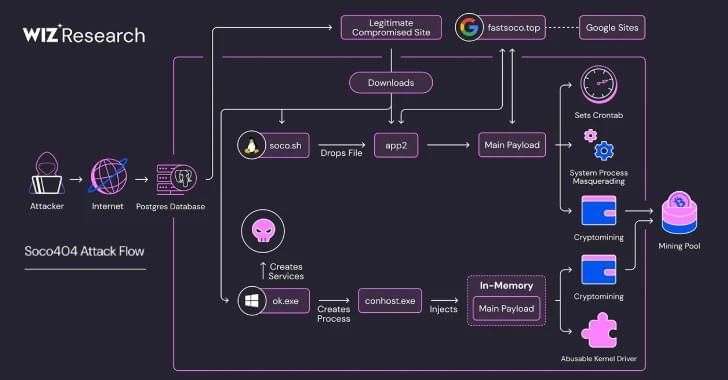
The threat activity clusters have been codenamed Soco404 and Koske by cloud security firms Wiz and Aqua, respectively.
Soco404 “targets both Linux and Windows systems, deploying platform-specific malware,” Wiz researchers Maor Dokhanian, Shahar Dorfman, and Avigayil Mechtinger said. “They use process masquerading to disguise malicious activity as legitimate system processes.”

A new Linux malware named Koske may have been developed with artificial intelligence and is using seemingly benign JPEG images of panda bears to deploy malware directly into system memory.
Researchers from cybersecurity company AquaSec analyzed Koske and described it as “a sophhisticated Linux threat.” Based on the observed adaptive behavior, the researchers believe that the malware was developed using large language models (LLMs) or automation frameworks.
Koske’s purpose is to deploy CPU and GPU-optimized cryptocurrency miners that use the host’s computational resources to mine over 18 distinct coins.

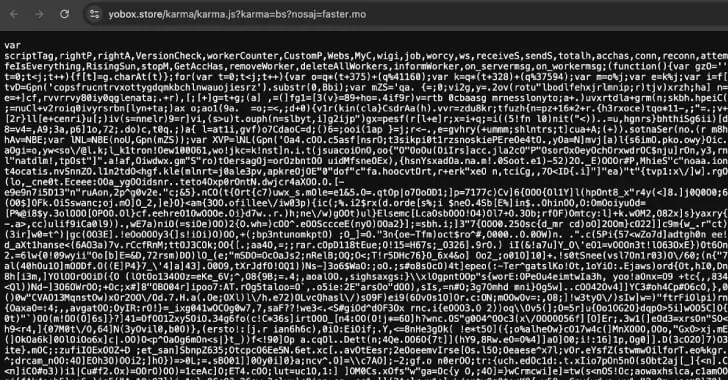
A new attack campaign has compromised more than 3,500 websites worldwide with JavaScript cryptocurrency miners, marking the return of browser-based cryptojacking attacks once popularized by the likes of CoinHive.
Although the service has since shuttered after browser makers took steps to ban miner-related apps and add-ons, researchers from the c/side said they found evidence of a stealthy miner packed within obfuscated JavaScript that assesses the computational power of a device and spawns background Web Workers to execute mining tasks in parallel without raising any alarm.
More importantly, the activity has been found to leverage WebSockets to fetch mining tasks from an external server, so as to dynamically adjust the mining intensity based on the device capabilities and accordingly throttle resource consumption to maintain stealth.


The attack chains begin when one of these adversary-controlled accounts messages a victim through X, Telegram, or Discord, urging them to test out their software in exchange for a cryptocurrency payment.
Should the target agree to the test, they are redirected to a fictitious website from where they are promoted to enter a registration code provided by the employee to download either a Windows Electron application or an Apple disk image (DMG) file, depending on the operating system used.
On Windows systems, opening the malicious application displays a Cloudflare verification screen to the victim while it covertly profiles the machine and proceeds to download and execute an MSI installer. Although the exact nature of the payload is unclear, it’s believed that an information stealer is run at this stage.

Cybersecurity researchers have uncovered over 40 malicious browser extensions for Mozilla Firefox that are designed to steal cryptocurrency wallet secrets, putting users’ digital assets at risk.
“These extensions impersonate legitimate wallet tools from widely-used platforms such as Coinbase, MetaMask, Trust Wallet, Phantom, Exodus, OKX, Keplr, MyMonero, Bitget, Leap, Ethereum Wallet, and Filfox,” Koi Security researcher Yuval Ronen said.
The large-scale campaign is said to have been ongoing since at least April 2025, with new extensions uploaded to the Firefox Add-ons store as recently as last week.

Have you heard about the crazy guys who bought an entire tower to convert it into a vertical village? Yes, that’s us.
Do you want to walk the 16-floor tower and explore the space? Still on the fence, if you should become a citizen? Do you have questions about how you can get involved and co-create? Wanna hear updates on what happened in the last 2 weeks? This event is for you! 👩🚀
About us: We are transforming a 16-floor tower in the heart of San Francisco into a self-governed vertical village —a hub for frontier technologies and creative arts. 8 themed floors will be dedicated to creating tier-one labs, spanning AI, Ethereum, biotech, neuroscience, longevity, robotics, human flourishing, and arts & music. These floors will house innovators and creators pushing the boundaries of human potential in a post-AI-singularity world.