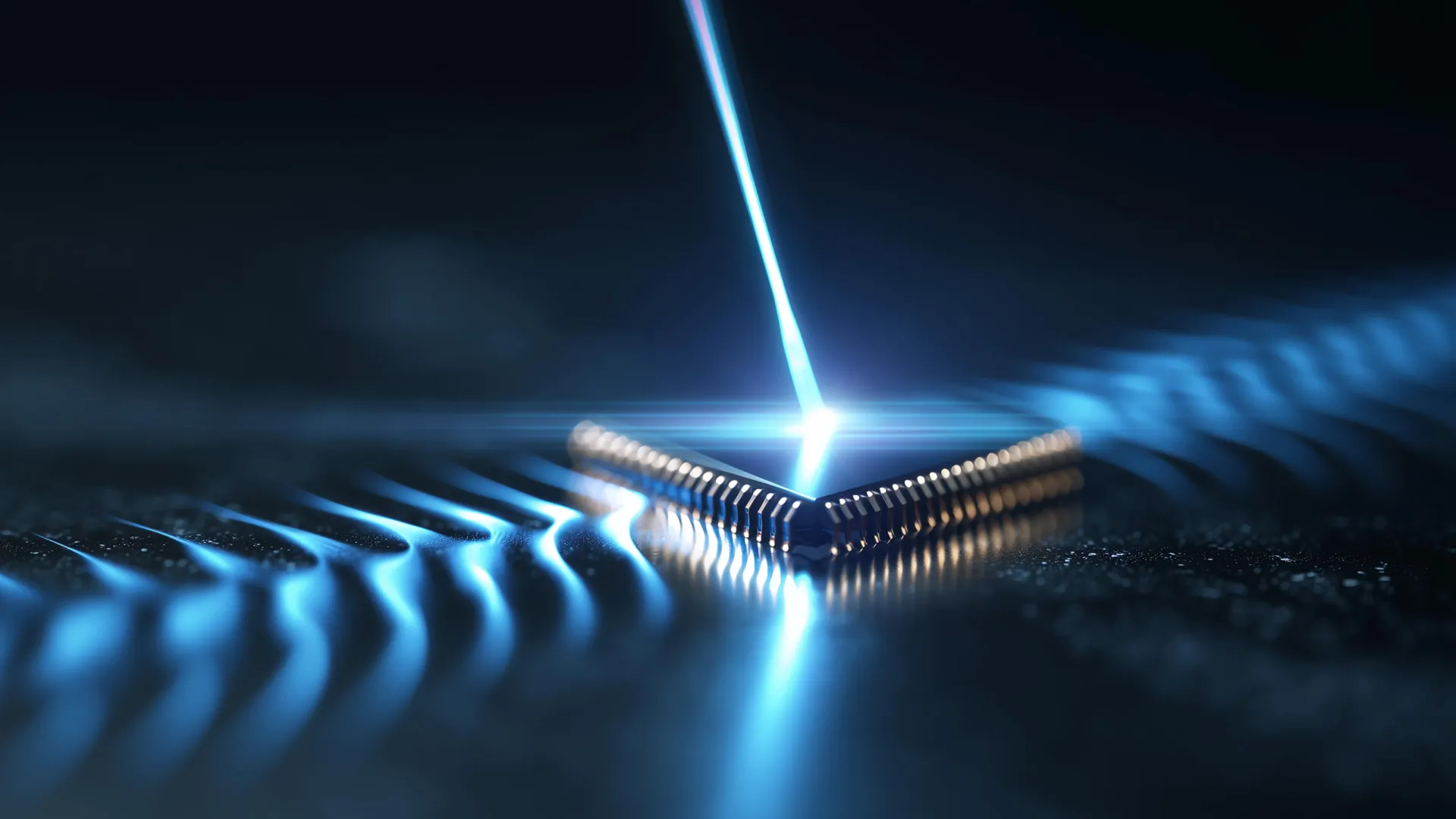
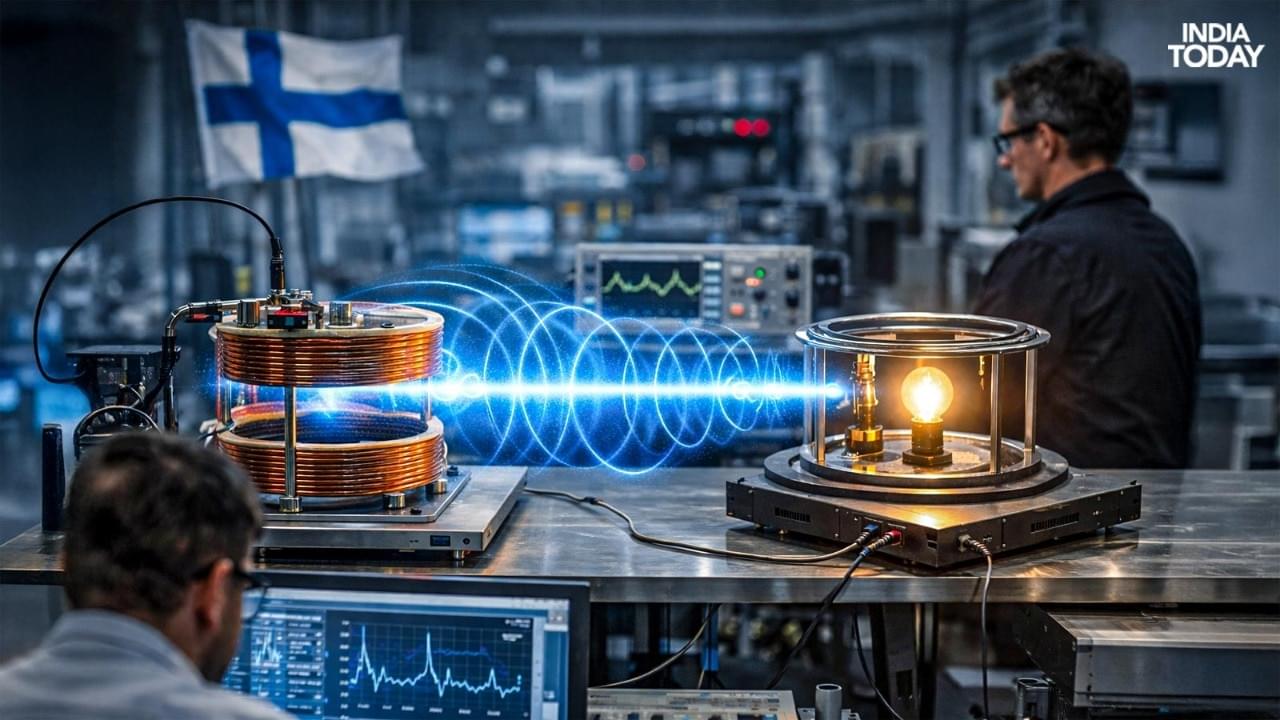
In controlled experiments, engineers have shown that electricity can be transmitted through the air using highly controlled electromagnetic fields and resonant coupling techniques, conceptually similar to the way data is sent via Wi-Fi but tailored for energy transfer.
These approaches build on decades of research into magnetic resonance and inductive power transfer, which seek to send energy efficiently across short distances without physical contact between transmitter and receiver…
…Past research from the university demonstrated that magnetic loop antennas can transfer power wirelessly at relatively high efficiency over short ranges, offering insights into how to optimize coupling and reduce energy losses.
More recent demonstrations reported in global tech news describe Finnish teams successfully powering small devices through the air using wireless power transfer methods.
Finland continues to make progress in the field of wireless electricity transmission, an area of research that aims to send power through the air without the use of traditional cables or plugs.
Recent demonstrations and experiments by Finnish researchers have highlighted steady advancements in technology that could one day reshape how devices are powered, though widespread commercial deployment remains distant.