Survivors of childhood trauma face higher risks of persistent pain after events like car crashes. New findings in Pain show that early adversity creates a physiological vulnerability to unremitting physical discomfort.




A new analysis of soldiers attempting to join the U.S. Army Special Forces suggests that specific genetic variations play a role in how individuals handle extreme physical and mental pressure. The research identified distinct links between a soldier’s DNA and their cognitive performance, psychological resilience, and physiological stress response during a grueling selection course. These findings were published recently in the academic journal Physiology & Behavior.
To become a member of the elite Army Special Forces, a soldier must first pass the Special Forces Assessment and Selection course. This training program is widely recognized as one of the most difficult military evaluations in the world. Candidates must endure nearly three weeks of intense physical exertion. They face sleep deprivation and complex problem-solving exercises. The attrition rate is notoriously high. Approximately 70 percent of the soldiers who attempt the course fail to complete it. This environment creates a unique laboratory for scientists to study human endurance.
Researchers have sought to understand why some individuals thrive in these punishing environments while others struggle. Resilience is generally defined as the ability to adapt positively to adversity, trauma, or threats. It involves a combination of psychological stability and physiological recovery. While physical training and mental preparation are essential, biological factors also play a substantial role. Genetics help determine how the brain regulates chemicals and how the body processes stress hormones.

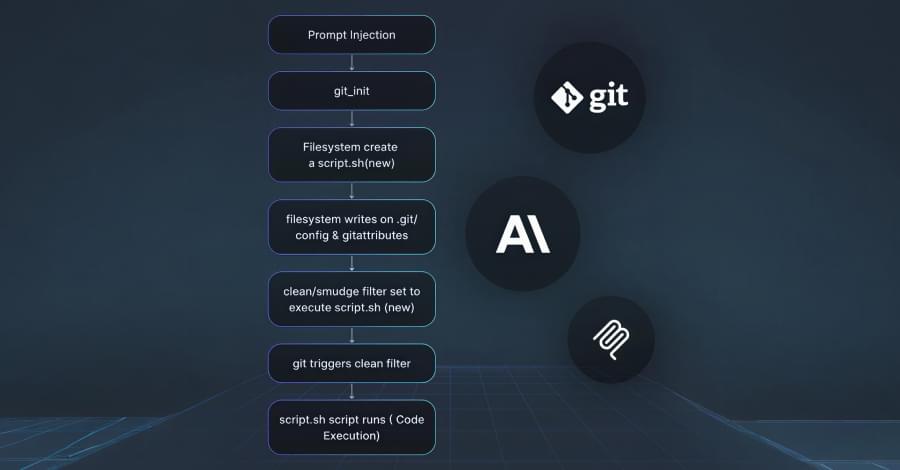
A set of three security vulnerabilities has been disclosed in mcp-server-git, the official Git Model Context Protocol (MCP) server maintained by Anthropic, that could be exploited to read or delete arbitrary files and execute code under certain conditions.
“These flaws can be exploited through prompt injection, meaning an attacker who can influence what an AI assistant reads (a malicious README, a poisoned issue description, a compromised webpage) can weaponize these vulnerabilities without any direct access to the victim’s system,” Cyata researcher Yarden Porat said in a report shared with The Hacker News.
Mcp-server-git is a Python package and an MCP server that provides a set of built-in tools to read, search, and manipulate Git repositories programmatically via large language models (LLMs).


