Amazon disrupted APT29’s June 2025 campaign exploiting Microsoft device code authentication, redirecting 10% of visitors to malicious domains.



Microsoft has released the KB5064081 preview cumulative update for Windows 11 24H2, which includes thirty-six new features or changes, with many gradually rolling out. These updates include new Recall features and a new way of displaying CPU usage in Task Manager.
The KB5064081 update is part of the company’s optional non-security preview update schedule, which releases updates at the end of each month to test new fixes and features coming to the next month’s Patch Tuesday.
Unlike regular Patch Tuesday cumulative updates, monthly non-security preview updates do not include security updates and are optional.

WhatsApp has patched a security vulnerability in its iOS and macOS messaging clients that was exploited in targeted zero-day attacks.
The company says this zero-click flaw (tracked as CVE-2025–55177) affects WhatsApp for iOS prior to version 2.25.21.73, WhatsApp Business for iOS v2.25.21.78, and WhatsApp for Mac v2.25.21.78.
“Incomplete authorization of linked device synchronization messages in WhatsApp […] could have allowed an unrelated user to trigger processing of content from an arbitrary URL on a target’s device,” WhatsApp said in a Friday security advisory.

Microsoft has found no link between the August 2025 KB5063878 security update and customer reports of failure and data corruption issues affecting solid-state drives (SSDs) and hard disk drives (HDDs).
Redmond first told BleepingComputer last week that it is aware of users reporting SSD failures after installing this month’s Windows 11 24H2 security update.
In a subsequent service alert seen by BleepingComputer, Redmond said that it was unable to reproduce the issue on up-to-date systems and began collecting user reports with additional details from those affected.

Google now reports that the Salesloft Drift breach is larger than initially thought, warning that attackers also used stolen OAuth tokens to access a small number of Google Workspace email accounts in addition to stealing data from Salesforce instances.
Based on new information identified by GTIG, the scope of this compromise is not exclusive to the Salesforce integration with Salesloft Drift and impacts other integrations,’ warns Google.
We now advise all Salesloft Drift customers to treat any and all authentication tokens stored in or connected to the Drift platform as potentially compromised.
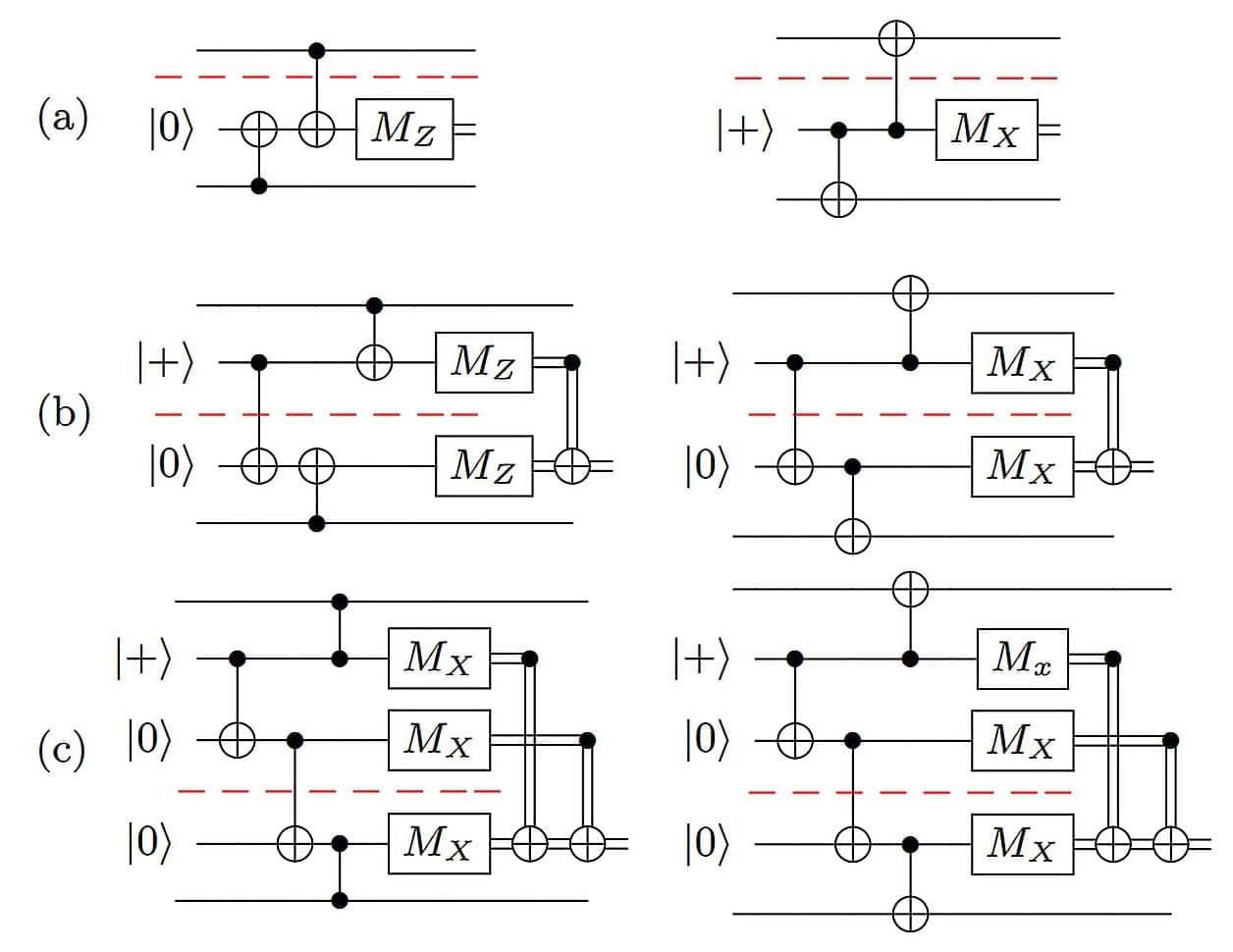
While quantum computers are already being used for research in chemistry, material science, and data security, most are still too small to be useful for large-scale applications. A study led by researchers at the University of California, Riverside, now shows how “scalable” quantum architectures—systems made up of many small chips working together as one powerful unit—can be made.
Quantum dots – semiconductor nanostructures that can emit single photons on demand – are considered among the most promising sources for photonic quantum computing.
However, every quantum dot is slightly different and may emit a slightly different color, according to a team at the University of Innsbruck, Austria, which has developed a technique to improve multi-photon state generation. The Innsbruck team states that, “the different forms of quantum dot means that, to produce multi-photon states we cannot use multiple quantum dots.”
Usually, researchers use a single quantum dot and multiplex the emission into different spatial and temporal modes, using a fast electro-optic modulator. But a contemporary technological challenge: faster electro-optic modulators are expensive and often require very customized engineering. To add to that, it may not be very efficient, which introduces unwanted losses in the system.
Nature Publishing: https://www.nature.com/articles/s41534-025-01083-0
Security wise: The team’s work combines years of research in quantum optics, semiconductor physics, and photonic engineering to open the door for next-generation quantum computers andunwanted losses in the system.
Communications. Here’s what you need to know. Securities IO: https://www.securities.io/passive-two-photon-quantum-dots-secure-communication
Researchers have developed QuantumShield-BC, a blockchain framework designed to resist attacks from quantum computers by integrating post-quantum cryptography (PQC) utilising algorithms such as Dilithium and SPHINCS+, quantum key distribution (QKD), and quantum Byzantine fault tolerance (Q-BFT) leveraging quantum random number generation (QRNG) for unbiased leader selection. The framework was tested on a controlled testbed with up to 100 nodes, demonstrating resistance to simulated quantum attacks and achieving fairness through QRNG-based consensus. An ablation study confirmed the contribution of each quantum component to overall security, although the QKD implementation was simulated and scalability to larger networks requires further investigation.

UK’s new defense system can hit tennis-ball-sized objects traveling at Mach 2 speed.
The U.K. has made a significant effort to upgrade its missile defense power. The country is buying six new Land Ceptor air defense missile systems to bolster national security and defence.
Named Sky Sabre, the system delivers higher accuracy at the time of combat. It’a capable of hitting a tennis-ball sized object travelling twice the speed of sound.
The sophisticated system can also simultaneously control the flight of 24 missiles, guiding them each to intercept separate targets at once.

Microsoft has confirmed that the August 2025 security updates are causing severe lag and stuttering issues with NDI streaming software on some Windows 10 and Windows 11 systems.
This comes after widespread reports from users experiencing a wide range of performance problems when using various streaming apps, including OBS (Open Broadcast Software).
“Severe stuttering, lag, and choppy audio/video might occur when using NDI (Network Device Interface) for streaming or transferring audio/video feeds between PCs after installing the August 2025 Windows security update,” the company said in a new Windows release health update.