Russian defense firms hit by cyberattacks using EAGLET malware via phishing lures; threat actors linked to Head Mare and Hive0156.


Threat hunters have disclosed two different malware campaigns that have targeted vulnerabilities and misconfigurations across cloud environments to deliver cryptocurrency miners.
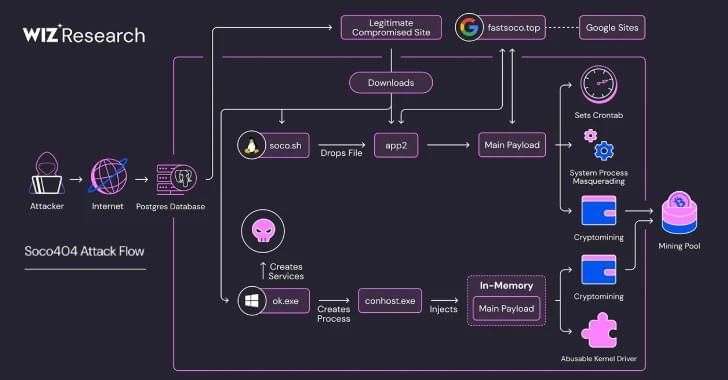
The threat activity clusters have been codenamed Soco404 and Koske by cloud security firms Wiz and Aqua, respectively.
Soco404 “targets both Linux and Windows systems, deploying platform-specific malware,” Wiz researchers Maor Dokhanian, Shahar Dorfman, and Avigayil Mechtinger said. “They use process masquerading to disguise malicious activity as legitimate system processes.”
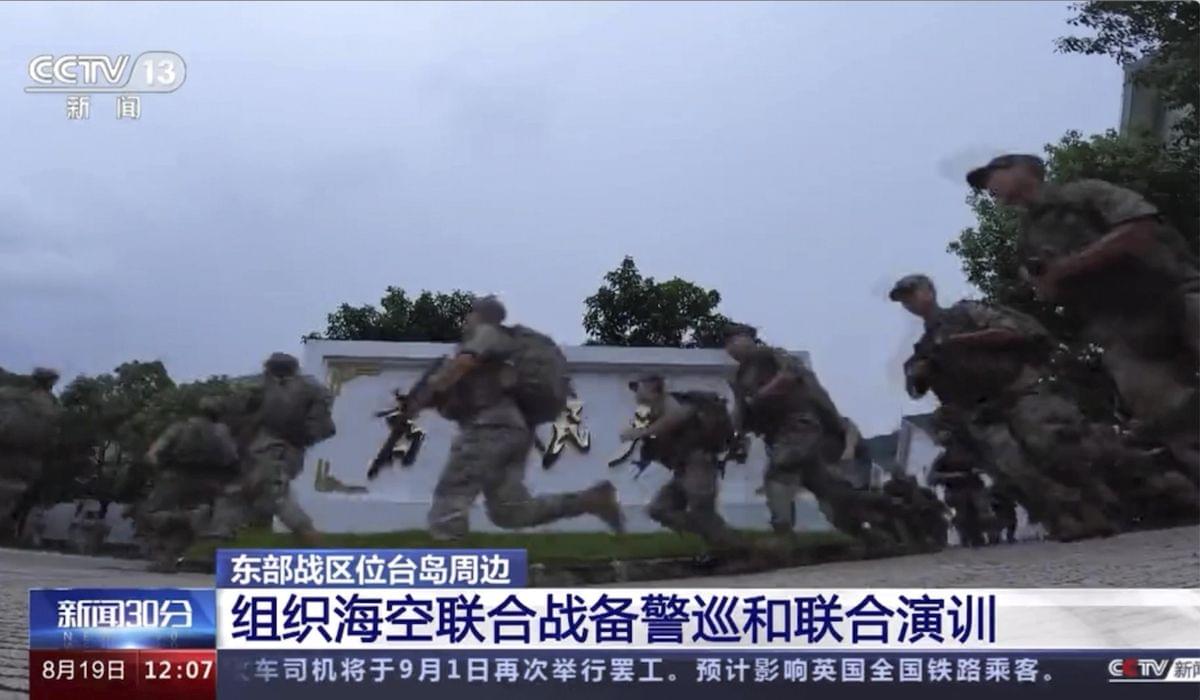
The Chinese military is building sophisticated biological weapons and small-scale electronic tools made with nanotechnology that could be used in covert warfare, a major study warns.
“China’s invisible arsenals encompass a range of advanced weaponry that are distinctly focused on providing the Chinese Communist Party with a range of asymmetric warfare options, including the delivery of biological, biochemical and neurobiological weapons on target populations,” according to a report by three open-source intelligence analysts.
The People’s Liberation Army, or PLA, is developing nanoweapons using highly sophisticated microscopic materials that enhance the effects of biological weapons, according to the report, titled “In the Shadows of Science: Unravelling China’s Invisible Arsenals of Nanoweapons.” It was made public earlier this month.




A new Linux malware named Koske may have been developed with artificial intelligence and is using seemingly benign JPEG images of panda bears to deploy malware directly into system memory.
Researchers from cybersecurity company AquaSec analyzed Koske and described it as “a sophhisticated Linux threat.” Based on the observed adaptive behavior, the researchers believe that the malware was developed using large language models (LLMs) or automation frameworks.
Koske’s purpose is to deploy CPU and GPU-optimized cryptocurrency miners that use the host’s computational resources to mine over 18 distinct coins.

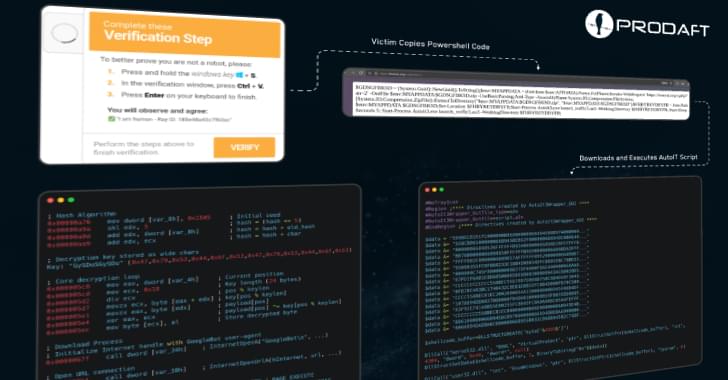
A threat actor called EncryptHub has compromised a game on Steam to distribute info-stealing malware to unsuspecting users downloading the title.
A few days ago, the hacker (also tracked as Larva-208), injected malicious binaries into the Chemia game files hosted on Steam.
Chemia is a survival crafting game from developer ‘Aether Forge Studios,’ which is currently offered as early access on Steam but has no public release date.
A China-based hacking group is deploying Warlock ransomware on Microsoft SharePoint servers vulnerable to widespread attacks targeting the recently patched ToolShell zero-day exploit chain.
Non-profit security organization Shadowserver is currently tracking over 420 SharePoint servers that are exposed online and remain vulnerable to these ongoing attacks.
“Although Microsoft has observed this threat actor deploying Warlock and Lockbit ransomware in the past, Microsoft is currently unable to confidently assess the threat actor’s objectives,” the company said in a Wednesday report.