The hackers started their attack in January but escalated their efforts in recent weeks, security experts say. Business and government agencies were affected.




Under our RADICS program, researchers developed tools to aid in the rapid recovery of our power grids amidst a cyberattack. Today we’re spotlighting the program’s many accomplishments: https://www.darpa.mil/news-events/2021-02-23
Under our RADICS program, researchers developed tools to aid in the rapid recovery of our power grids amidst a cyberattack. Today we’re spotlighting the program’s many accomplishments: https://t.co/ki0VV5bKlI pic.twitter.com/c1dSVewK2b
— DARPA (@DARPA) February 23, 2021



These three pillars of cybersecurity risk management need not stand alone. In fact, they all should be incorporated together in cybersecurity framework strategy to identify gaps, mitigate threats, and build resilience in the case of an inevitable cyberattack. Of course, there are many other elements and protocols associated with utilization of these cyber risk management pillars. Combining them creates a more holistic mindset that also makes it easier to plan and adapt. With the growing sophistication of global cyber-threats and the expanding digital attack surface, a vigilant three pillar approach makes good sense.
Chuck Brooks, President of Brooks Consulting International, is a globally recognized thought leader and evangelist for Cybersecurity and Emerging Technologies. LinkedIn named Chuck as one of “The Top 5 Tech Experts to Follow on LinkedIn.” Chuck was named as a 2020 top leader and influencer in “Who’s Who in Cybersecurity” by Onalytica. He was named by Thompson Reuters as a “Top 50 Global Influencer in Risk, Compliance,” and by IFSEC as the “#2 Global Cybersecurity Influencer.” He was named by The Potomac Officers Club and Executive Mosaic and GovCon as at “One of The Top Five Executives to Watch in GovCon Cybersecurity. Chuck is a two-time Presidential appointee who was an original member of the Department of Homeland Security. Chuck has been a featured speaker at numerous conferences and events including presenting before the G20 country meeting on energy cybersecurity.

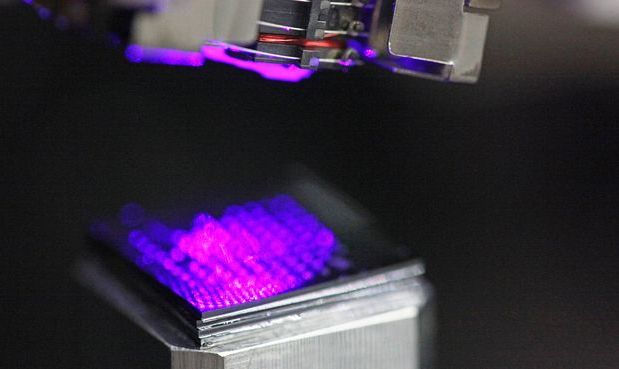
Researchers from the Technical University of Denmark (DTU) have repurposed a component from a Microsoft Xbox 360 to develop a high-resolution large-volume nanoscale 3D printer with various applications in the medical sector.
The team took an optical pick-up unit (OPU) component from an Xbox 360 console to replace a conventional Stereolithography (SLA) optical system, in order to drastically simplify the SLA 3D printing system. With the OPU costing less than $5, the researcher’s solution could potentially increase the affordability of such equipment by thousands of pounds.
“With our 3D printer that can print micro and nanoscale 3D objects, we are able to go from tens of micrometers in printing resolution down to hundreds of nanometers without expensive specialized components,” said DTU PhD Student Tien-Jen Chang and research team member.