Circa 2021
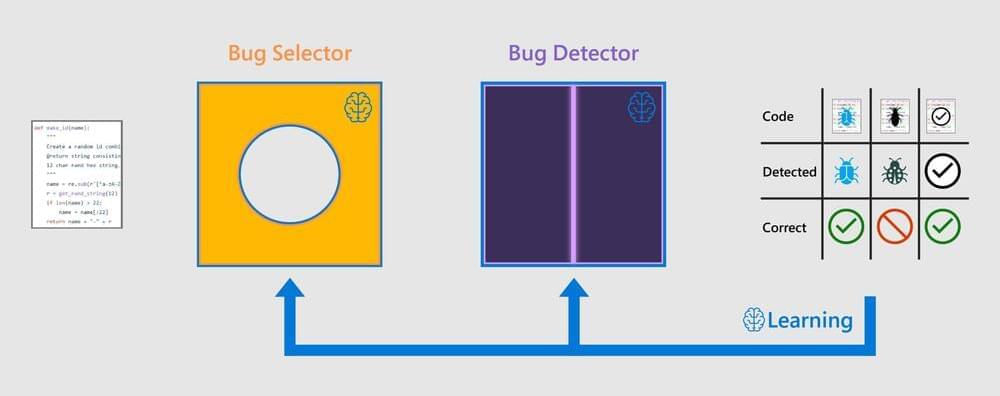
Finding and fixing bugs in code is a time-consuming, and often frustrating, part of everyday work for software developers. Can deep learning address this problem and help developers deliver better software, faster? In a new paper, Self-Supervised Bug Detection and Repair, presented at the 2021 Conference on Neural Information Processing Systems (NeurIPS 2021), we show a promising deep learning model, which we call BugLab can be taught to detect and fix bugs, without using labelled data, through a “hide and seek” game.
To find and fix bugs in code requires not only reasoning over the code’s structure but also understanding ambiguous natural language hints that software developers leave in code comments, variable names, and more. For example, the code snippet below fixes a bug in an open-source project in GitHub.
Here the developer’s intent is clear through the natural language comment as well as the high-level structure of the code. However, a bug slipped through, and the wrong comparison operator was used. Our deep learning model was able to correctly identify this bug and alert the developer.