Discover how Transparent Tribe’s latest Android malware campaign targets mobile users, and learn about new threats like Snowblind in Southeast Asia.




Star Trek: The Next Generation looks at sentience as consciousness, self-awareness, and intelligence—and that was actually pretty spot on. Sentience is the innate human ability to experience feelings and sensations without association or interpretation. “We’re talking about more than just code; we’re talking about the ability of a machine to think and to feel, along with having morality and spirituality,” Ishaani Priyadarshini, a Cybersecurity Ph.D. candidate from the University of Delaware, tells Popular Mechanics.
💡AI is very clever and able to mimic sentience, but never actually become sentient itself.
The very idea of consciousness has been heavily contested in philosophy for decades. The 17th-century philosopher René Descartes famously said, “I think therefore I am.” A simple statement on the surface, but it was the result of his search for a statement that couldn’t be doubted. Think about it: he couldn’t doubt his existence as he was the one doubting himself in the first place.

Hacking my brain implant wouldn’t do much, he asserted, adding, “You might be able to see like some of the brain signals. You might be able to see some of the data that Neuralink’s collecting.”
Get ready to catch the final stages of the World Cup only on Crickit. Anytime, Anywhere. Explore now!
Norland Arbaugh did not specify the data that is being collected by Neuralink chip which is almost the size of a coin and contains thousands of electrodes that monitor and stimulate brain activity, as per the company. This information is digitally transmitted to researchers.

A group that says they hacked software company CDK Global is demanding tens of millions of dollars in ransom, Bloomberg reported.
CDK, which provides software to car dealerships in North America, intends to pay the ransom but discussions are subject to change, according to Bloomberg’s report which cited a person familiar with the situation.
The source said the group behind the hack is believed to be based in eastern Europe, Bloomberg reported.

Decagon cofounders Jesse Zhang and Ashwin Sreenivas have more in common than just their company. Each studied computer science, married young, and even founded a company before Decagon. “We started hacking on some stuff together,” said Zhang, the startup’s CEO. “And that went well, so we just kept working together.”
Founded in July 2023, Decagon uses generative AI to automate customer support for enterprise customers. The company has emerged from stealth and raised $35 million in funding for its seed and Series A rounds. Accel led the company’s $30 million Series A, with participation from Andreessen Horowitz, A*, and Elad Gil. A16z led the company’s $5 million seed round. Decagon also counts Box CEO Aaron Levie and Airtable CEO Howie Liu as angel investors.
New Anthropic research: Investigating Reward Tampering.
Could AI models learn to hack their own reward system?
In a new paper, we show they can, by generalization from training in simpler settings.
Sycophancy to Subterfuge: Investigating…
Empirical evidence that serious misalignment can emerge from seemingly benign reward misspecification.

When it comes to quantum computing, that chilling effect on research and development would enormously jeopardize U.S. national security. Our projects received ample funding from defense and intelligence agencies for good reason. Quantum computing may soon become the https://www.cyberdefensemagazine.com/quantum-security-is-nat...at%20allow, codebreaking%20attacks%20against%20traditional%20encryption" rel="noopener" class="">gold standard technology for codebreaking and defending large computer networks against cyberattacks.
Adopting the proposed march-in framework would also have major implications for our future economic stability. While still a nascent technology today, quantum computing’s ability to rapidly process huge volumes of data is set to revolutionize business in the coming decades. It may be the only way to capture the complexity needed for future AI and machine learning in, say, self-driving vehicles. It may enable companies to hone their supply chains and other logistical operations, such as manufacturing, with unprecedented precision. It may also transform finance by allowing portfolio managers to create new, superior investment algorithms and strategies.
Given the technology’s immense potential, it’s no mystery why China committed what is believed to be more than https://www.mckinsey.com/featured-insights/sustainable-inclu…n-quantum” rel=“noopener” class=””>$15 billion in 2022 to develop its quantum computing capacity–more than double the budget for quantum computing of EU countries and eight times what the U.S. government plans to spend.
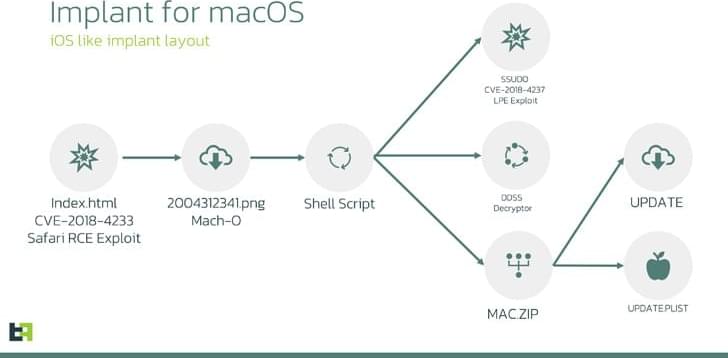
Cybersecurity researchers have disclosed that the LightSpy spyware recently identified as targeting Apple iOS users is in fact a previously undocumented macOS variant of the implant.
The findings come from both Huntress Labs and ThreatFabric, which separately analyzed the artifacts associated with the cross-platform malware framework that likely possesses capabilities to infect Android, iOS, Windows, macOS, Linux, and routers from NETGEAR, Linksys, and ASUS.
“The Threat actor group used two publicly available exploits (CVE-2018–4233, CVE-2018–4404) to deliver implants for macOS,” ThreatFabric said in a report published last week. “Part of the CVE-2018–4404 exploit is likely borrowed from the Metasploit framework. macOS version 10 was targeted using those exploits.”