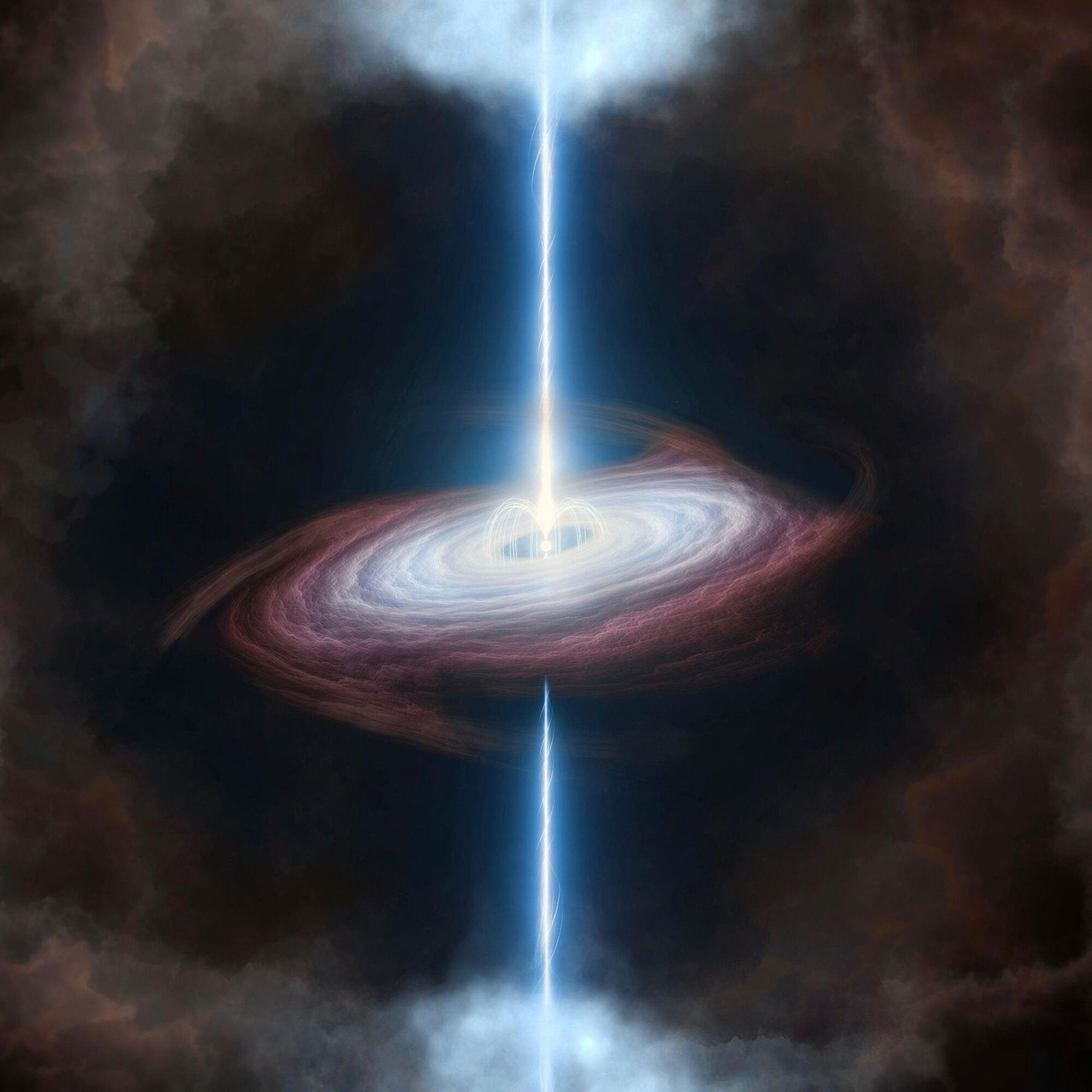
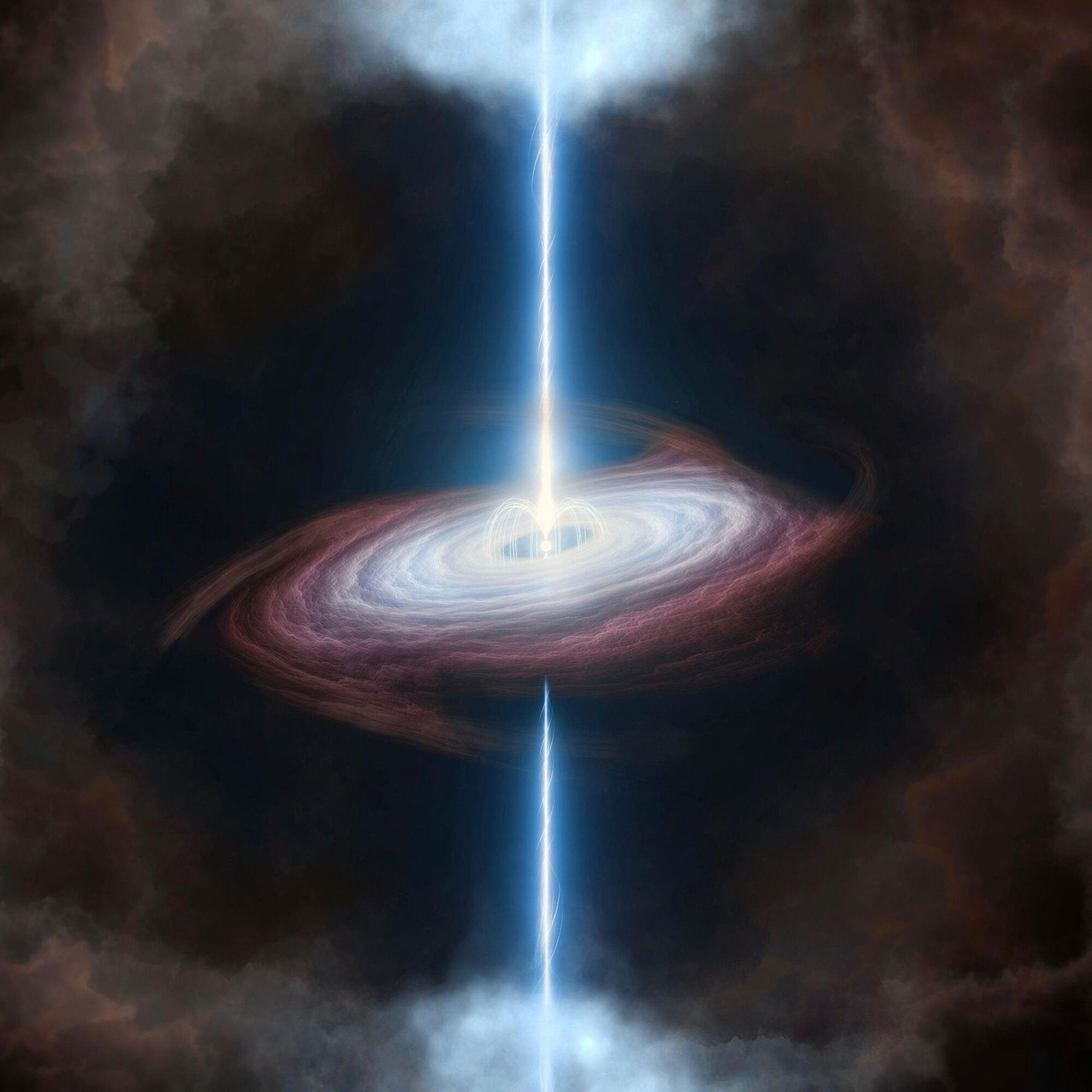
Astronomers have identified the first clear evidence of a magnetar forming during a superluminous supernova, offering new insight into some of the brightest explosions in the universe.



The GlassWorm malware campaign is being used to fuel an ongoing attack that leverages the stolen GitHub tokens to inject malware into hundreds of Python repositories.
“The attack targets Python projects — including Django apps, ML research code, Streamlit dashboards, and PyPI packages — by appending obfuscated code to files like setup.py, main.py, and app.py,” StepSecurity said. “Anyone who runs pip install from a compromised repo or clones and executes the code will trigger the malware.”
According to the software supply chain security company, the earliest injections date back to March 8, 2026. The attackers, upon gaining access to the developer accounts, rebasing the latest legitimate commits on the default branch of the targeted repositories with malicious code, and then force-pushing the changes, while keeping the original commit’s message, author, and author date intact.

To establish persistence, the LNK files are copied to the Windows Startup folder so that they are automatically launched following a system reboot. The attack chain then displays a URL containing lures related to installing Starlink or a Ukrainian charity named Come Back Alive Foundation.
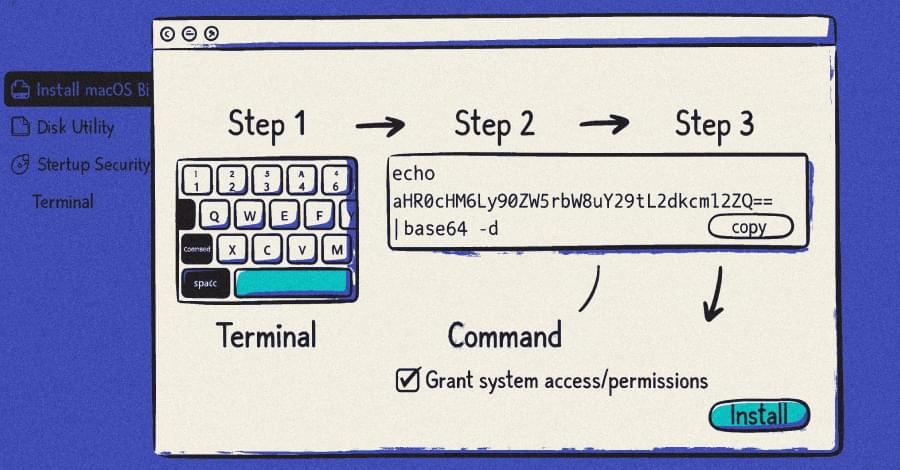
The HTML file is eventually executed via the Microsoft Edge browser in headless mode, which then loads the remote obfuscated script hosted on Pastefy.
The browser is executed with additional parameters like –no-sandbox, –disable-web-security, –allow-file-access-from-files, –use-fake-ui-for-media-stream, –auto-select-screen-capture-source=true, and –disable-user-media-security, granting it access to the local file system, as well as camera, microphone, and screen capture without requiring any user interaction.
